forceCopy Stealer
The North Korea-linked hacking group Kimsuky has been found using spear-phishing attacks to distribute a newly identified information-stealing malware called forceCopy. These attacks begin with phishing emails that contain a disguised Windows shortcut (LNK) file, made to appear like a Microsoft Office or PDF document. Unsuspecting recipients who open the file unknowingly set off a chain reaction that executes malicious commands.
Table of Contents
Exploiting Legitimate Tools to DeliverThreatening Payloads
Once the user interacts with the harmful attachment, the infection process starts by executing PowerShell or ‘mshta.exe,’ a legitimate Windows utility used to run HTML Application (HTA) files. This technique allows the attackers to fetch and deploy additional malware payloads from an external source without raising suspicion.
Deploying Trojans and Remote Desktop Tools
The attacks ultimately result in the deployment of known threats, including the PEBBLEDASH Trojan and a modified version of the RDP Wrapper, an open-source tool used for remote desktop access. Alongside these, proxy malware is introduced to ensure a continuous connection between the compromised device and the attackers’ external network via Remote Desktop Protocol (RDP).
A Keylogger and forceCopy: Targeting Stored Credentials
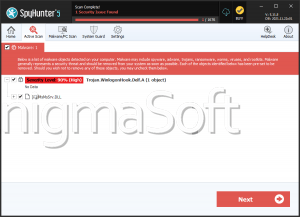
Kimsuky has also been seen using a PowerShell-based keylogger to capture keystrokes, further enhancing their ability to steal sensitive information. Additionally, the newly discovered forceCopy malware is specifically designed to extract files stored in web browser directories. This suggests an attempt to bypass security restrictions and directly access browser configuration files where login credentials are often stored.
A Strategic Shift: Using RDP for Host Control
The group’s reliance on RDP Wrapper and proxy malware highlights a tactical shift in their operations. Previously, Kimsuky primarily used custom-built backdoors to control infected systems. Now, by leveraging widely available tools, they aim to maintain persistence while reducing the chances of detection.
APT43: A Long-Standing Cyber Espionage Threat
Kimsuky, also known by aliases such as APT43, Black Banshee, and Emerald Sleet, is believed to operate under North Korea’s Reconnaissance General Bureau (RGB), the country’s leading foreign intelligence service. Active since at least 2012, the group has a long history of executing sophisticated social engineering attacks to bypass email security defenses.
Expanding Operations with Russian-Based Phishing Campaigns
Recent findings indicate that Kimsuky has been using phishing emails sent from Russian email services to carry out credential theft campaigns. This adaptation, observed in December 2024, reflects the group’s evolving tactics as it continues to refine its social engineering techniques to target high-value individuals and organizations.