Beware: Cybercriminals Leveraging Coronavirus to Exploit Computer Users and Spread Malware
 It hasn't taken a lot of time for threat actors to realize the social engineering opportunity that the novel coronavirus (2019-nCoV) has presented them. The respiratory infection that originated in Wuhan, China, has become front-page news in recent weeks, although the first cases were reported in December 2019.
It hasn't taken a lot of time for threat actors to realize the social engineering opportunity that the novel coronavirus (2019-nCoV) has presented them. The respiratory infection that originated in Wuhan, China, has become front-page news in recent weeks, although the first cases were reported in December 2019.
In about a month since the first reported infections, there are more than 8,000 confirmed cases, with the death toll rising to more than 170 people. By now, the coronavirus has spread to every province of China, as well as several other countries, including the US, Canada, Japan, France, Germany, Taiwan, and Thailand, prompting the World Health Organization to declare a global health emergency.
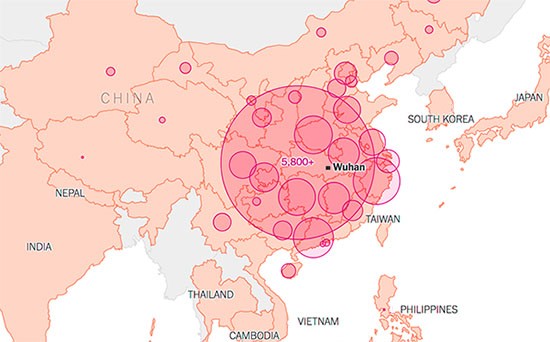
Map via upnewsinfo.com of Coronavirus spreading throughout China and neighboring countries
It comes as no surprise that cybercriminals are beginning to exploit the coronavirus threat as a way to disseminate their own viruses. Security researchers have come across a phishing campaign that is spreading the notorious Emotet banking trojan in Japan, with emails that mimic legitimate warnings from health organizations in the Gifu, Tottori, and Osaka prefectures.
According to a report from IBM X-Force, the emails are written in Japanese, and "The text briefly states that there have been reports of coronavirus patients in the Gifu prefecture in Japan and urges the reader to view the attached document." They also have a footer that features all the correct mailing addresses, fax and phone numbers, for the relevant health organizations in the respective prefectures, for added authenticity.
The documents that the threat actors attach are alleged instructions on how to protect yourself from the virus, updates on its spread, and virus-detection procedures. This can't be farther from the truth, especially considering the recent news that the novel coronavirus can be spread by people showing no symptoms of the illness.
This Week in Malware Video: A CoronaVirus Malware Alert discussing how hackers are continually leveraging the COVID-19 epidemic to spread malware, phishing emails, fake apps, fake websites, and malware-laced advertisements.
Although the geographical position of Japan makes it the most obvious target for the initial phishing campaigns, security researchers warn that these sorts of attacks are going to become more widespread as the coronavirus itself affects more countries worldwide. There have already been detections of coronavirus-related files with the following names: UDS:DangerousObject.Multi.Generic, Worm.Python.Agent.c, Worm.VBS.Dinihou.r, Trojan.WinLNK.Agent.gg, HEUR:Trojan.WinLNK.Agent.gen, HEUR:Trojan.PDF.Badur.b, and Trojan.WinLNK.Agent.ew.
Such news stories are bound to be exploited by criminal gangs, both online and offline. Take, for example, the recent Sodinokibi ransomware attack against Travelex, which was later used by criminal gangs to conduct telephone scams.
The best way to protect yourself from phishing campaigns is to avoid opening unsolicited emails and any attachments that they might contain. In the case that you come across an email that piques your interest, it is advisable to try to find and access the information that it allegedly contains directly from its source, instead of opening any suspicious attachments.