Cerber Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 11,686 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 71,941 |
| First Seen: | March 4, 2016 |
| Last Seen: | March 25, 2025 |
| OS(es) Affected: | Windows |
Cerber Ransomware Image
The Cerber Ransomware is a ransomware infection that is used to encrypt the victims' files. The Cerber Ransomware adds the extension CERBER to every file that the Cerber Ransomware encrypts. After the Cerber Ransomware has encrypted some of the files of the victim, the Cerber Ransomware demands the payment of a ransom in exchange for the decryption key. According to Cerber Ransomware's ransom note, computer users have one week to pay the ransom amount before this amount is doubled.
Table of Contents
The Cerber Ransomware Contains an Audio Message
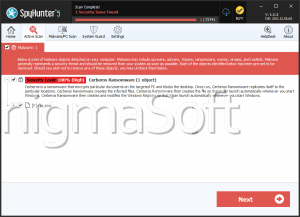
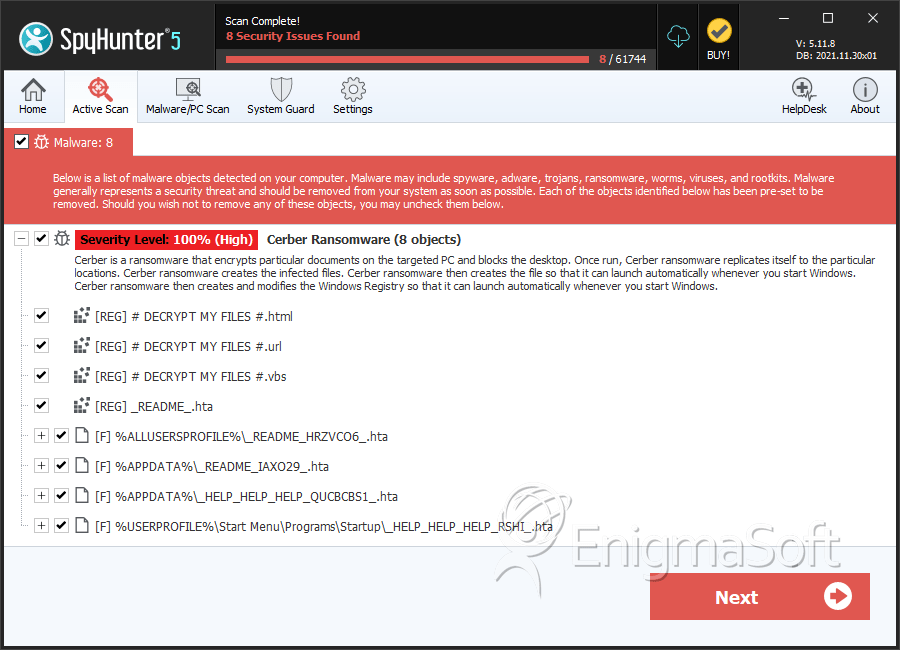
As the Cerber Ransomware encrypts the victim's files, it creates TXT, HTML, and VBS files named 'DECRYPT MY FILES' with instructions on how to pay the Cerber Ransomware's ransom. These files are dropped on every folder that contains files that were encrypted by Cerber Ransomware. According to these ransom notes, the only way to decrypt the files is by using the 'Cerber Decryptor,' provided by the people responsible for the Cerber Ransomware. The VBS file contains an audio message with this same information. According to the Cerber Ransomware attack, victims must pay 1.24 BitCoin to gain access to the decryption utility (in 2016, this amount is between $500 and $800 USD on average). After a week, the amount is doubled. The Cerber Ransomware demands the payment to be made through TOR.
The Cerber Ransomware is very similar to other ransomware Trojans, including CryptoWall and TeslaCrypt. These attacks are nearly identical, only differing in small details, and it is highly likely that they share large portions of their code. Computer users should avoid paying the Cerber Ransomware ransom for two reasons: first, computer users have no guarantee that the con artists responsible for the Cerber Ransomware attack will honor their part of the bargain and provide the decryptor after the payment has been made. Secondly, paying the Cerber Ransomware ransom enables these fraudsters to continue carrying out these attacks and financing the development of new ransomware.
The basic characteristic of Cerber is the use of AES-256 encryption to scramble its victims' files. The ransomware appends a number of different extensions to the encrypted files, including .cerber, .cerber2, .cerber3, .beef, .af47, .ba99. The ransom notes used in different versions also have different names: # DECRYPT MY FILES #.txt, # HELP DECRYPT#.html and _R_E_A_D___T_H_I_S___[random]_.txt, to name a few.
The infection vectors used in various Cerber campaigns are more or less standard fare - spam email campaigns containing malicious attachments ranging from office files to JavaScript chunks, exploit kits that deliver the payload, as well as malicious sites that contain code that downloads the ransomware. Another curious feature of the ransomware is that it runs a system check and avoids users located in former Soviet republics, including Armenia, Georgia, Belarus, Moldova, Russia itself and Ukraine, among others. This alone could be some indication about the origins of the threat.
Execution and Behavior
Once it executes, Cerber drops a randomly named copy of itself in a uniquely named folder located in %AppData%. Together with this, it also establishes a form of persistence, creating a shortcut to the executable under %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup. The ransomware also edits the system's registry, creating two new entries under HKEY_CURRENT_USER\Printers\Defaults\. The entries are called Component_00 and Component_01 and contain binary data. Additional registry keys are added to ensure persistence in various registry autorun locations.
When it encrypts the victim's files, Cerber doesn't need a live connection to its command and control (C&C) server, which means unplugging your ethernet cable won't do any good. The encryption doesn't simply append a new extension, as is customary with ransomwares, it also changes the original file name, making all encrypted files completely unrecognizable. The most commonly used extension appended by the ransomware is .cerber, with some versions using .cerber2 and .cerber3, as well as unusual ones such as .ba99 and .beef.
PC security researchers have determined that the Cerber Ransomware targets and encrypts files with the following extensions:
.gif, .groups, .hdd, .hpp, .log, .m2ts, .m4p, .mkv, .mpeg, .ndf, .nvram, .ogg, .ost, .pab, .pdb, .pif, .png, .qed, .qcow, .qcow2, .rvt, .st7, .stm, .vbox, .vdi, .vhd, .vhdx, .vmdk, .vmsd, .vmx, .vmxf, .3fr, .3pr, .ab4, .accde, .accdr, .accdt, .ach, .acr, .adb, .advertisements, .agdl, .ait, .apj, .asm, .awg, .back, .backup, .backupdb, .bay, .bdb, .bgt, .bik, .bpw, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .ce1, .ce2, .cib, .craw, .crw, .csh, .csl, .db_journal, .dc2, .dcs, .ddoc, .ddrw, .der, .des, .dgc, .djvu, .dng, .drf, .dxg, .eml, .erbsql, .erf, .exf, .ffd, .fh, .fhd, .gray, .grey, .gry, .hbk, .ibd, .ibz, .iiq, .incpas, .jpe, .kc2, .kdbx, .kdc, .kpdx, .lua, .mdc, .mef, .mfw, .mmw, .mny, .mrw, .myd, .ndd, .nef, .nk2, .nop, .nrw, .ns2, .ns3, .ns4, .nwb, .nx2, .nxl, .nyf, .odb, .odf, .odg, .odm, .orf, .otg, .oth, .otp, .ots, .ott, .p12, .p7b, .p7c, .pdd, .pem, .plus_muhd, .plc, .pot, .pptx, .psafe3, .py, .qba, .qbr, .qbw, .qbx, .qby, .raf, .rat, .raw, .rdb, .rwl, .rwz, .s3db, .sd0, .sda, .sdf, .sqlite, .sqlite3, .sqlitedb, .sr2, .srf, .srw, .st5, .st8, .std, .sti, .stw, .stx, .sxd, .sxg, .sxi, .sxm, .tex, .wallet, .wb2, .wpd, .x11, .x3f, .xis, .ycbcra, .yuv, .contact, .dbx, .doc, .docx, .jnt, .jpg, .msg, .oab, .ods, .pdf, .pps, .ppsm, .ppt, .pptm, .prf, .pst, .rar, .rtf, .txt, .wab, .xls, .xlsx, .xml, .zip, .1cd, .3ds, .3g2, .3gp, .7z, .7zip, .accdb, .aoi, .asf, .asp, .aspx, .asx, .avi, .bak, .cer, .cfg, .class, .config, .css, .csv, .db, .dds, .dwg, .dxf, .flf, .flv, .html, .idx, .js, .key, .kwm, .laccdb, .ldf, .lit, .m3u, .mbx, .md, .mdf, .mid, .mlb, .mov, .mp3, .mp4, .mpg, .obj, .odt, .pages, .php, .psd, .pwm, .rm, .safe, .sav, .save, .sql, .srt, .swf, .thm, .vob, .wav, .wma, .wmv, .xlsb,3dm, .aac, .ai, .arw, .c, .cdr, .cls, .cpi, .cpp, .cs, .db3, .docm, .dot, .dotm, .dotx, .drw, .dxb, .eps, .fla, .flac, .fxg, .java, .m, .m4v, .max, .mdb, .pcd, .pct, .pl, .potm, .potx, .ppam, .ppsm, .ppsx, .pptm, .ps, .r3d, .rw2, .sldm, .sldx, .svg, .tga, .wps, .xla, .xlam, .xlm, .xlr, .xlsm, .xlt, .xltm, .xltx, .xlw, .act, .adp, .al, .bkp, .blend, .cdf, .cdx, .cgm, .cr2, .crt, .dac, .dbf, .dcr, .ddd, .design, .dtd, .fdb, .fff, .fpx, .h, .iif, .indd, .jpeg, .mos, .nd, .nsd, .nsf, .nsg, .nsh, .odc, .odp, .oil, .pas, .pat, .pef, .pfx, .ptx, .qbb, .qbm, .sas7bdat, .say, .st4, .st6, .stc, .sxc, .sxw, .tlg, .wad, .xlk, .aiff, .bin, .bmp, .cmt, .dat, .dit, .edb, .flvv
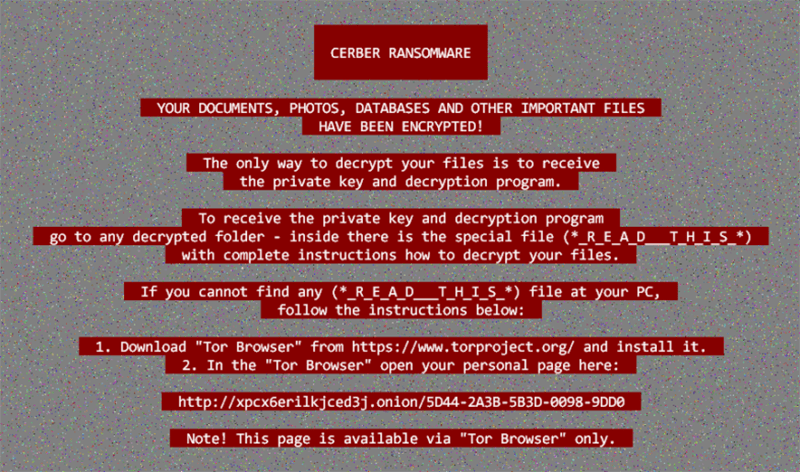
Ransom Note
Some versions of Cerber display their ransom note as a wallpaper image that replaces the old one, while others use HTML and plain text files for the note. However, the text in all notes is largely the same:
CERBER RANSOMWARE
Your documents, photos, databases and other important files have been encrypted!
The only way to decrypt your files is to receive the private key and your decryption program.
To receive the private key and decryption program go to any decrypted folder - inside is a special file (*README*) with complete instructions how to decrypt your files.
If you cannot find any (*README*) file at your PC, follow the instructions below:
[Tor url]
Note! This page is available via "Tor Browser" only.
The ransom note associated with the Cerber Ransomware will contain the following information:
Your documents, photos, databases and other important files have been encrypted!
To decrypt your files follow the instructions:
---------------------------------------------------------------------------------------
1. Download and install the "Tor Browser" from https://www.torproject.org/
2. Run it
3. In the "Tor Browser" open website: [redacted]
4. Follow the instructions at this website
---------------------------------------------------------------------------------------
CERBER DECRYPTOR
Your documents, photos, databases and other important files have been encrypted!
To decrypt your files you need to buy the special software - .
All transactions should be performed via bitcoin network only.
Within 7 days you can purchase this product at a special price 1.24 BTC (approximately $524).
After 7 days the price of this product will increase up to 2.48 BTC (approximately $1048).
The HTML versions of the ransom note come with a snippet in Visual Basic that reads the ransom note to the victim - an interesting touch, even if somewhat pointless. The Tor url in the ransom note leads to a pesonalized page that can be viewd in a number of languages, to ensure as many victims as possible are able to try and pay the ransom.
Cerber Rented Out as a Service
Well into its lifespan, Cerber turned into ransomware-as-a-service. The criminal network that originally produced Cerber started renting it out to any other cyber criminals who were willing to split their profits. The idea behind this model is that any ransom payments made by victims of the criminal third parties spreading the malware are split between them and the original authors of Cerber. This has proven to be a very profitable mode of operation for the bad actors behind the ransomware, with estimates of Cerber making around $200,000 in Bitcoin each month. This allows the authors of the ransomware-as-a-service to virtually do nothing more while someone else runs the spam email dissemination campaigns for them.
The Cerber ransomware went through a number of versions, some of them given numeric descriptors by security researchers. The last one given an official number is Cerber 6 - a version that came out sometime in 2017. It boasted improved anti-detection capabilities due to a new multi-component design, checking for active anti-malware software and whether or not it's running in a sandbox VM environment. Cerber 6 was also found distributed in self-extracting executable archives that contained VB scripts as well as a DLL component.
In recent years, a new ransomware has been doing damage, named Magniber by security researchers. The name is a mashup of the Magnitude exploit kit and Cerber, as it was believed that the new ransomware carried by the Magnitude EK was Cerber. However, it turned out that the Magniber payload is actually from a family different from Cerber’s and shares little with it under the hood.
Security researchers working with Checkpoint have released a decryption tool, which works for just a few of the versions of the ransomware.
Dealing with the Cerber Ransomware
If the Cerber Ransomware has been installed on your computer, the best solution is to restore the encrypted files is from a backup. Because of this, the best protective measure against the Cerber Ransomware and similar encryption Trojans is to backup all important data regularly. You should avoid websites that may be associated with questionable content and use a reliable security program that is fully up-to-date.
SpyHunter Detects & Remove Cerber Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | README.hta | 777e13c9a5cad4e1d2134d5104188ff6 | 43 |
| 2. | _HELP_HELP_HELP_QUCBCBS1_.hta | c042f1d91619e9b4f91bf1e1b78fee85 | 14 |
| 3. | _HELP_HELP_HELP_RSHI_.hta | a46e5f2ce8a20bbb8548959debb9ac0c | 10 |
| 4. | _HELP_HELP_HELP_STOV8H1_.hta | 1632ca0953d5499bf251455159a80ea0 | 6 |
| 5. | _HELP_HELP_HELP_ND8FZ.hta | 041ef4b6a12e0b3165172884301b0d1e | 5 |
| 6. | _HELP_HELP_HELP_Z49XU_.hta | 243d0fd4f4bee5f11698c20d43b958ff | 4 |
| 7. | _HELP_HELP_HELP_XJ7UC8.hta | 4ab1a256a5115d00fa7a3222936ddc03 | 3 |
| 8. | _HELP_HELP_HELP_WMB7F1L.hta | 9befacccf34d60ad1f141e531ddbba52 | 3 |
| 9. | _HELP_HELP_HELP_XFCV_.hta | 01ec9e50d17de043a23997d6562293ad | 3 |
| 10. | _HELP_HELP_HELP_2AK4U21_.hta | 55790c64ce1ff75647d5cadcadf3876e | 3 |
| 11. | _HELP_HELP_HELP_3NNARI.hta | 0ef13a9213c456db231825061eec294c | 2 |
| 12. | _HELP_HELP_HELP_L41VV_.hta | c63b4a524713e4c5f3802463cb46dab8 | 2 |
| 13. | _READ_THI$_FILE_L81EB65A_.hta | 2a6828d2ba37bb97efb4773619b80715 | 2 |
| 14. | _HELP_HELP_HELP_KJ2P.hta | 6689ad9f43ab19a1ccfad9db6a16b772 | 1 |
| 15. | _HELP_HELP_HELP_IGTRU.hta | c1ea46e1877d089983a4d9060997b04f | 1 |
| 16. | _HELP_HELP_HELP_5B3HEZ6.hta | b10e6f69d0c16008410b5c8cfaae0138 | 1 |
| 17. | _HELP_HELP_HELP_8EWN8.hta | 6f59455817d32c34ae35aac63043f285 | 1 |
| 18. | _HELP_HELP_HELP_2R9I63OS.hta | a2daec078c54bb6bc5e96038a1506f2c | 1 |
| 19. | _HELP_HELP_HELP_UYUR4YE.hta | bc0c75128b9cbc02c8c053c1155fb6d9 | 1 |
| 20. | _HELP_HELP_HELP_CKJ4GL.hta | 99d3fc208d3623107cfb18a9069e23bd | 1 |
| 21. | _HELP_HELP_HELP_SUXEZY_.hta | 5190e890725bf431ba44001e190c70f5 | 1 |
| 22. | _HELP_HELP_HELP_GLP9_.hta | 5f7533c663ddb4c0ae4dbbaafb50d491 | 1 |
| 23. | _HELP_HELP_HELP_HUUKTW_.hta | 0224da72bc3638b351cf509cdfc443c2 | 1 |
| 24. | _READ_THI$_FILE_DB3DT9_.hta | 7476a75b0680d99f5338b886bc7def62 | 1 |
| 25. | wP6fT.exe | 731279e3c09f8e52a849c0a9c1043bb5 | 1 |
| 26. | cmdkey.exe | 27cf39d205567505d840391e4761a7a0 | 1 |
| 27. | u.exe | 3dabcb3463ab266e734c83285c977106 | 0 |