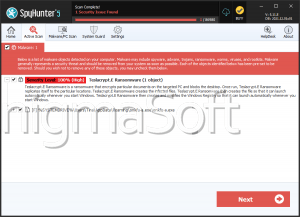
TeslaCrypt Ransomware
TeslaCrypt is a ransomware infection that uses AES encryption to encrypt the victims' files. TeslaCrypt then demands that the victim pay a ransom of $500 USD in BitCoin or $1000 USD using the PayPal My Cash Cards. PC security analysts have noted that TeslaCrypt is different from other recent rasomware attacks in that TeslaCrypt authorize victims to pay using an alternative to BitCoin, which allows TeslaCrypt to reach a wider potential group of victims. PayPal My Cash cards can be bought in stores in the United States, making it clear that TeslaCrypt is designed to attack mainly computer users in the United States. However, it is more likely that PayPal can confiscate these types of profits, meaning that TeslaCrypt demands twice as much for these types of payments. This is one of the reasons why these attacks do not use credit card payments or similar methods since these would be much too easy to trace.
PC security analysts have noted that, unlike other types of ransomware, TeslaCrypt specifically targets video game files. Many ransomware Trojans will encrypt all document files on the victim's computer, ranging from word processor documents to pictures. TeslaCrypt pays particular attention to popular games such as Minecraft, World of Warcraft and Steam. TeslaCrypt may target more than fifty different video games on victim's computers. This points to the fact that third parties are attempting to exploit the addictive quality and time sink involved in these games to increase the likelihood that victims will pay the ransom to regain access to their favorite games. PC security experts advise PC users to protect their machines from TeslaCrypt attacks.
The TeslaCrypt Ransomware Trojan will Take Your Files Hostage
TeslaCrypt is threatening in that TeslaCrypt directly attacks computers. Unlike PUPs (Potentially Unwanted Programs) that may limit themselves to displaying irritating advertisements, or ransomware Winlockers that may simply try to alarm inexperienced computer users into believing that their machines have been blocked by a third-party, TeslaCrypt encrypts the victim's files and holds those files for ransom until the money transaction occurs.
Ransomware, like its name implies, involve taking the victim's files hostage and holding them in exchange for a ransom. Essentially, TeslaCrypt will scan a computer for files with popular extensions such as DOC, 7Z, RAR, M4A, etc. Then, TeslaCrypt will encrypt the files using an AES encryption algorithm. There is no way to decrypt these files without obtaining that unique decryption key, making these types of attacks especially irritating. As part of its attack, TeslaCrypt will create .TXT files named HELP_TO_DECRYPT_YOUR_FILES.txt and change the victim's desktop image to a banner that reads as follows:
Your personal files are encrypted!
Your files have been safely encrypted on this PC: photos, videos, documents, etc. Click "Show Encrypted Files" button to view a complete list on encrypted files, and you can personally verify this.
Encryption was produced using a unique public key RSA-2048 generated for this computer. To decrypt files you need to obtain the private key.
Known files affected by TeslaCrypt:
.7z, .map, .m2, .rb, .jpg, .rar, .wmo, .mcmeta, .png, .cdr, .m4a, .itm, .vfs0, .jpeg, .indd, .wma, .sb, .mpqge, .txt, .ai, .avi, .fos, .kdb, .p7c, .eps, .wmv, .mcgame, .db0, .p7b, .pdf, .csv, .vdf, .DayZProfile, .p12, .pdd, .d3dbsp, .ztmp, .rofl, .pfx, .psd, .sc2save, .sis, .hkx, .pem, .dbfv, .sie, .sid, .bar, .crt, .mdf, .sum, .ncf, .upk, .cer, .wb2, .ibank, .menu, .das, .der, .rtf, .t13, .layout, .iwi, .x3f, .wpd, .t12, .dmp, .litemod, .srw, .dxg, .qdf, .blob, .asset, .pef, .xf, .gdb, .esm, .forge, .ptx, .dwg, .tax, .001, .ltx, .r3d, .pst, .pkpass, .vtf, .bsa, .rw2, .accdb, .bc6, .dazip, .apk, .rwl, .mdb, .bc7, .fpk, .re4, .raw, .pptm, .bkp, .mlx, .sav, .raf, .pptx, .qic, .kf, .lbf, .orf, .ppt, .bkf, .iwd, .slm, .nrw, .xlk, .sidn, .vpk, .bik, .mrwref, .xlsb, .sidd, .tor, .epk, .mef, .xlsm, .mddata, .psk, .rgss3a, .erf, .xlsx, .itl, .rim, .pak, .kdc, .xls, .itdb, .w3x, .big, .dcr, .wps, .icxs, .fsh, .unity3d, .cr2, .docm, .hvpl, .ntl, .wotreplay, .crw, .docx, .hplg, .arch00, .xxx, .bay, .doc, .hkdb, .lvl, .desc, .sr2, .odb, .mdbackup, .snx, .py, .srf, .odc, .syncdb, .cfr, .m3u, .arw, .odm, .gho, .ff, .flv, .3fr, .odp, .cas, .vpp, _pc, .js, .dng, .ods, .svg, .lrf, .css, .jpe, .odt
TeslaCrypt will claim that the victim has only three days to make the payment and enable the victim to decrypt only one file for free as proof that they can perform the task. TeslaCrypt may be distributed using typical threat delivery methods. This means that the use of strong security software and common online safety habits can prevent these types of attacks. PC security analysts strongly advise against paying the TeslaCrypt fine. This encourages third parties and funds their activities, and computer users cannot trust ill minded people to keep their word and provide the decryption key. It is sometimes possible to restore some files using the Shadow Explorer and other specialized tools. Prevention and the use of off-site back-ups to properly restore encrypted files are the best course of action when dealing with ransomware threats.