CerberTear Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 88 |
| First Seen: | November 9, 2016 |
| OS(es) Affected: | Windows |
The CerberTear Ransomware is an identification name used by security researchers when talking about Trojans based on the Hidden Tear project, which pretends to be variants of the Cerber Ransomware. Experts agree that the authors of the CerberTear Ransomware attempt to present their Trojan as a new version of Cerber that encrypts nearly one hundred and thirty data containers. The CerberTear Trojans are delivered to users via spam emails that are loaded with a Trojan-Dropper packed as a macro-enabled document. Computer users need to be extra careful when an email appears to be sent from an account on social media and invites the user to open an interesting file that is attached to the message.
Table of Contents
The AES-256 Cipher is Favored by the Authors of the CerberTear Ransomware
The CerberTear Ransomware is an encryption Trojan that uses the AES-256 cipher to lock targeted data containers. The implementation of the AES-256 encryption routine allows the CerberTear Ransomware to lock files securely and discourage brute-force attacks. As stated above the CerberTear Trojans are based on the Hidden tear open-source project that was released by the research Utku Sen on Github.com. Analysis of sample that belong to the CerberTear Ransomware reveal that the Trojan is programmed to encode more than 130 file types. Researchers were able to extract the list of extensions targeted by the CerberTear Ransomware:
.RAW, .TIF, .GIF, .PNG, .BMP, .3DM, .MAX, .ACCDB, .DB, .DBF, .MDB, .PDB, .SQL, .SAV, .SPV, .GRLE, .MLX, .SV5, .GAME, .SLOT, .DWG, .DXF, .C, .CPP, .CS, .H, .PHP, .ASP, .RB, .JAVA, .JAR, .CLASS, .AAF, .AEP, .AEPX, .PLB, .PREL, .PRPROJ, .AET, .PPJ, .PSD, .INDD, .INDL, .INDT, .INDB, .INX, .IDML, .PMD, .XQX, .XQX, .AI, .EPS, .PS, .SVG, .SWF, .FLA, .AS3, .AS, .TXT, .DOC, .DOT, .DOCX, .DOCM, .DOTX, .DOTM, .DOCB, .RTF, .WPD, .WPS, .MSG, .PDF, .XLS, .XLT, .XLM, .XLSX, .XLSM, .XLTX, .XLTM, .XLSB, .XLA, .XLAM, .XLL, .XLW, .PPT, .POT, .PPS, .PPTX, .PPTM, .POTX, .POTM, .PPAM, .PPSX, .PPSM, .SLDX, .SLDM, .WAV, .MP3, .AIF, .IFF, .M3U, .M4U, .MID, .MPA, .WMA, .RA, .AVI, .MOV, .MP4, .3GP, .MPEG, .3G2, .ASF, .ASX, .FLV, .MPG, .WMV, .VOB, .M3U8, .CSV, .EFX, .SDF, .VCF, .XML, .SES.
Encoded objects can be recognized with ease by looking at the '.cerber' suffix placed after the original filename. For example, 'spotted_seal.jpeg' will be transformed to 'spotted_seal.jpeg.cerber' and will be represented by an icon that looks like a blank sheet of paper. The ransom note for CerberTear can be found on the desktop as 'HOW_TO_RESTORE_YOUR_DATA.html,' which offers the following message:
'CERBER RANSOMWARE DECRYPTOR
Your document, photos, databases and other important files have been encrypted!
To decrypt your tiles you need to buy the special software - Cerber Decryptor
All transactions should be performed via Bitcoin network only.
What is encryption?
Encryption is a reversible modification of information for security reasons but providing full access to it for authorized users.
To become an authorized user and keep the modification absolutely reversible (in other words to have a possibility to decrypt your files) you should have an individual private key.
But not only it.
It is required also to have the special decryption software (in your case 'Cerber Decryptor software) for safe and complete decryption of all your files and data.
Everything is clear for me but what should I do?
The first step is reading these instructions to the end. Your files have been encrypted with the 'Cerber Ransomware' software; the instructions ('HOW TO DECRYPT FILES.html) in the folders with your encrypted files are not viruses, they will help you.'
How to Deal with the CerberTear Ransomware
We should note that the author of the CerberTear Ransomware implements the 'Cerber' brand name in its campaign, but we observe an entirely different Trojan. However, the encryption mechanism employed by the CerberTear Ransomware cannot be broken and users may consider paying the ransom. At the time of writing this, the payment required by CerberTear is 0.4 Bitcoin, which equals approximate 290 USD. The payment for decryption is on the low end of the spectrum compared to threats like the Domino Ransomware and the LowLevel04 Ransomware, which require 1 BTC and 4 BTC respectively. Either way, you should reconsider spending money on a decryptor released by the maker of the CerberTear Ransomware. It is more than likely that your data will remain locked unless you take matters into your hands. You will need to use a credible anti-malware scanner to purge the CerberTear Ransomware. Backups from unmapped storage like DVD/CD disks, portable HDD, and USB drives should allow you to recover your data structure even if it takes a few hours. AV applications may flag files related to the CerberTear Ransomware as:
- BehavesLike.Win32.Downloader.gc
- Heur.Advml.Gen!c
- Ransom_HiddenTearCerber.A
- Riskware ( 0040eff71 )
- Trojan.GenericKD.3587705
- Trojan.Win32.Generic!BT
- Trojan.Win32.Z.Agent.474400[h]
- Trojan:Win32/Skeeyah.A!rfn
- W32/Malicious_Behavior.VEX
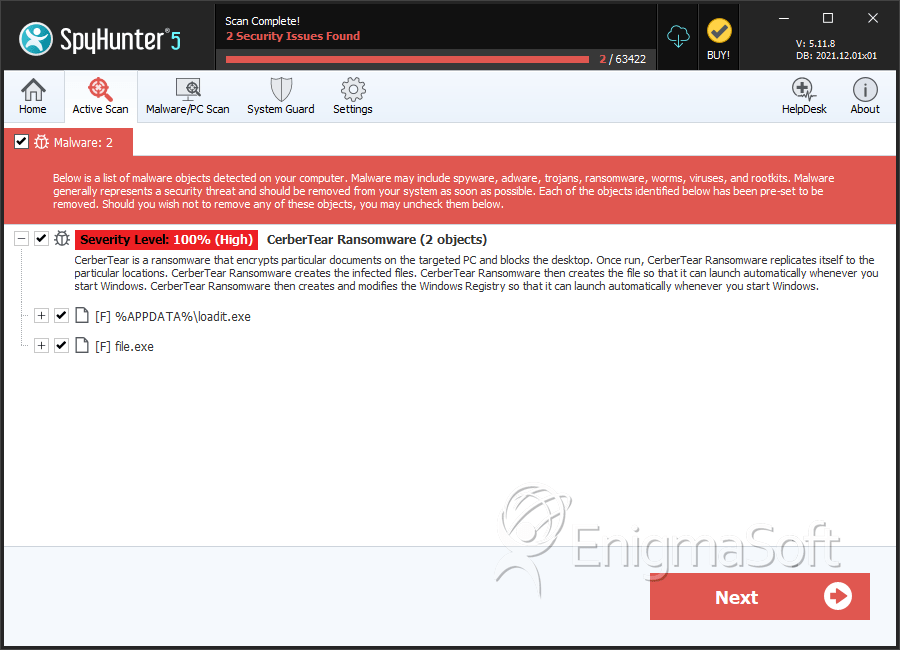
SpyHunter Detects & Remove CerberTear Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | loadit.exe | 11db0fc2064d7c858067b99b413e357b | 47 |
| 2. | loadit.exe | 2186c90605a735796b1d330d58feb037 | 25 |
| 3. | loadit.exe | 99cfe74ee73fa6f896edbb07be4f74ee | 14 |
| 4. | loadit.exe | 7d181574893ec9cb2795166623f8e531 | 2 |
| 5. | file.exe | 1ec959e01ba7b96e5c0583cade38ff1a | 0 |

