Security Monitor 2012
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 14,312 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 225 |
| First Seen: | December 14, 2011 |
| Last Seen: | August 19, 2023 |
| OS(es) Affected: | Windows |
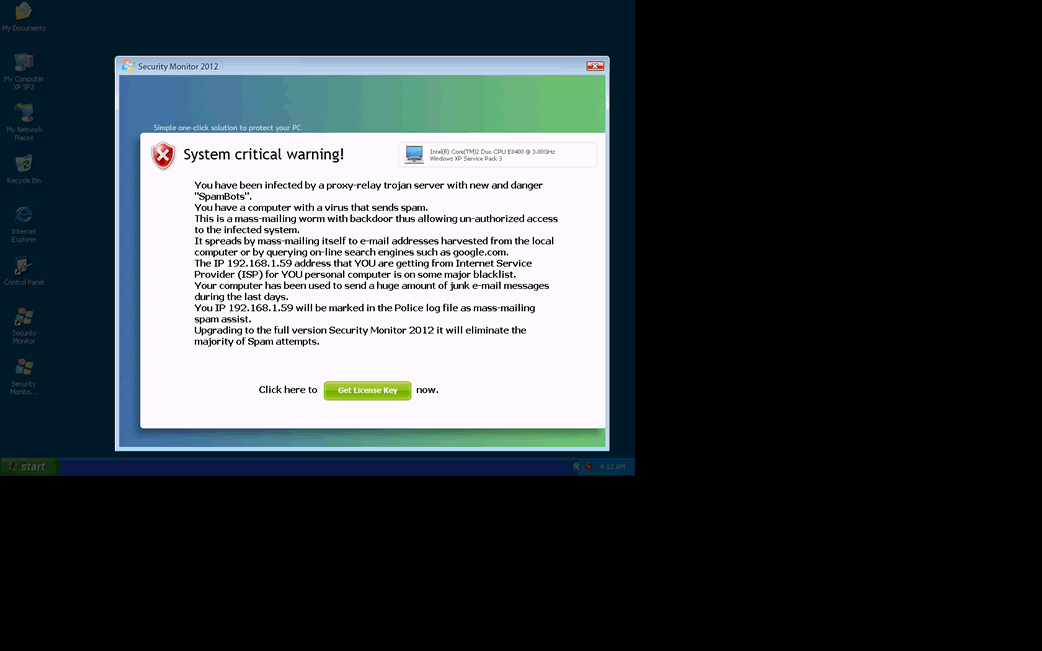
Security Monitor 2012 Image
Security Monitor 2012 is a fake security program affiliated with the WinWeb Security family. The rogue security programs belonging to this family are all cause by variants of the WinWeb Security Trojan infection. Security Monitor 2012 is not unique in the way Security Monitor 2012 infects a computer system. According to ESG security researchers, Security Monitor 2012 is practically identical in every way to previous iterations of WinWeb Security. As the year 2011 comes to a close, the criminals behind this harmful malware infection have started releasing a batch of clones of WinWeb Security with the number '2012' attached to the end, in order to make it appear as if they are new versions of legitimate security software. In fact, there is practically no difference between Security Monitor 2012 and the 2011 and 2010 editions of this rogue security program, except for the small interface changes to accommodate the change to its name. If Security Monitor 2012 is installed on your computer system, ESG security researchers strongly recommend starting your computer up in Safe Mode and using a legitimate anti-malware program to remove Security Monitor 2012 and all of its associated malware. Failure to remove Security Monitor 2012 in a timely manner can result in the theft of your credit card information, as well as further malware making its way into your computer system.
The Security Monitor 2012 scam is a typical version of the rogue security application scam. Most infections follow the same pattern in order to trick their victims into giving up their hard-earned cash. Usually, the Security Monitor 2012 scam follows the same steps:
- Security Monitor 2012 is first installed onto a computer system with the help of a dropper or downloader Trojan. These are malware infections designed to enter a computer system and install or download other Trojans. Examples of these kinds of malware include Zlob, Vundo and the Fake Microsoft Security Essentials Alert Trojan.
- Once installed, Security Monitor 2012 will display a large number of alerts claiming that the computer system is severely infected with a variety of malware. ESG malware analysts recommend that you disregard all of Security Monitor 2012's warnings. The real infection on your computer is Security Monitor 2012 itself.
- Security Monitor 2012 then offers to fix these nonexistent problems as long as you purchase a 'full version' of this useless program.
Among the numerous clones of Security Monitor 2012 are System Security, Antivirus Security, Total Security 2009, Security Tool, Trojan.RogueAV.a.gen, System Adware Scanner 2010, FakeAlert-KW.e, Advanced Security Tool 2010, System Tool 2011, Security Shield, MS Removal Tool, Total Security, System Security 2011, Essential Cleaner, Security Shield Pro 2011, Personal Shield Pro, Security Shield 2011, Security Sphere 2012, Advanced PC Shield 2012, Futurro Antivirus.









Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Fortinet | Adware/Zugo |
| DrWeb | Trojan.PWS.Banker.62728 |
| NOD32 | a variant of Win32/Toolbar.Zugo |
| McAfee | Artemis!87811BBEF243 |
| AVG | Dropper.Generic6.ACLT |
| Fortinet | W32/Jorik_IRCbot.ABH!tr |
| Ikarus | Trojan.Win32.Vilsel |
| Antiy-AVL | Trojan/Win32.Jorik.gen |
| AntiVir | TR/Pincav.L |
| DrWeb | BackDoor.IRC.NgrBot.42 |
| Sophos | Mal/VB-ABH |
| BitDefender | Gen:Variant.Barys.5089 |
| Kaspersky | Trojan.Win32.Jorik.IRCbot.nis |
| Avast | Win32:IRCBot-ETV [Trj] |
| Symantec | Trojan.Gen.2 |
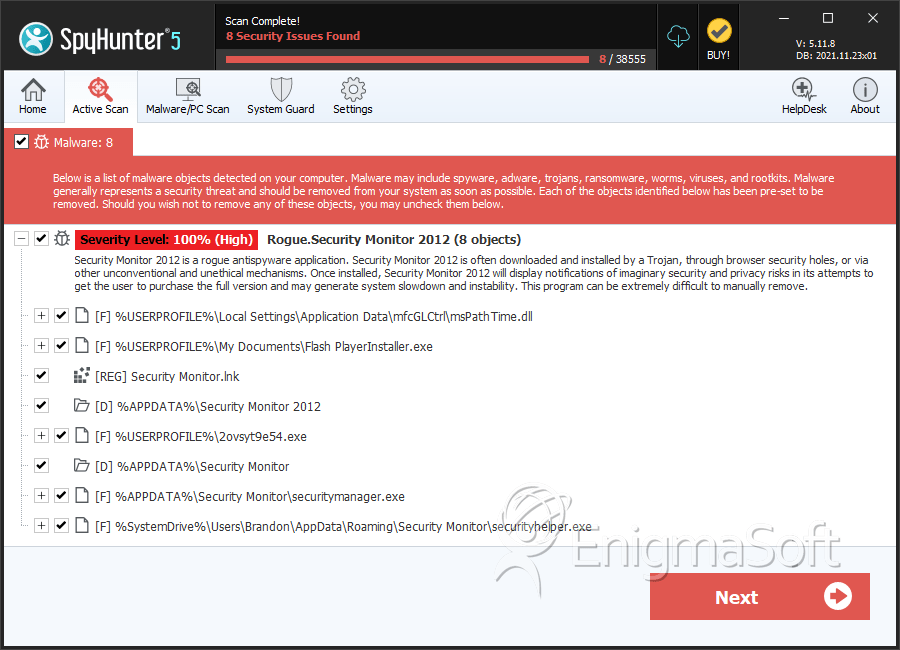
SpyHunter Detects & Remove Security Monitor 2012
Security Monitor 2012 Video
Tip: Turn your sound ON and watch the video in Full Screen mode.

File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | msPathTime.dll | 90351a17627d9e1e25c3213da4c17402 | 148 |
| 2. | Flash PlayerInstaller.exe | 87811bbef2433a2562a68bb08a493281 | 19 |
| 3. | 2ovsyt9e54.exe | 659016d93cc17add1338e407d38a2d15 | 4 |
| 4. | securitymanager.exe | ef68a96bc9f69ef5b3353dea40f0e57e | 2 |
| 5. | securitymanager.exe | 64b837773b6f54856c54385a52723d73 | 2 |
| 6. | securityhelper.exe | 0ac67e08915f2cd8f5e3dea7b0c5faae | 1 |
| 7. | Edvqvu.scr | cd2a77b834bb90be3330500240c2062b | 1 |
| 8. | 2463.exe | d66745ef5614720b0259cc54ec7bef24 | 1 |
| 9. | %AppData%\Security Monitor 2012\securitymanager.exe | ||
| 10. | %AppData%\Security Monitor 2012\Security Monitor.exe | ||
| 11. | %AppData%\Security Monitor 2012\securityhelper.exe | ||
| 12. | %AppData%\Security Monitor 2012\antivirus antispyware.exe | ||
| 13. | %AppData%\Security Monitor 2012\IcoUninstall.ico | ||
| 14. | %Programs%\Security Monitor 2012\Help Security Monitor 2012.lnk | ||
| 15. | %Desctop%\Security Monitor 2012.lnk | ||
| 16. | %Programs%\Security Monitor 2012\Activate Security Monitor 2012.lnk | ||
| 17. | %AppData%\Security Monitor 2012\IcoHelp.ico | ||
| 18. | %Programs%\Security Monitor 2012\Security Monitor 2012.lnk | ||
| 19. | %Programs%\Security Monitor 2012.lnk | ||
| 20. | %Programs%\Security Monitor 2012\ | ||
| 21. | %AppData%\Security Monitor 2012\IcoActivate.ico | ||
| 22. | %AppData%\Security Monitor 2012\ | ||
| 23. | %Programs%\Security Monitor 2012\How to Activate Security Monitor 2012.lnk | ||
| 24. | %AppData%\Microsoft\Internet Explorer\Quick Launch\Security Monitor 2012.lnk | ||
| 25. | %Desktop%\Security Monitor 2012.lnk |
Registry Details
Directories
Security Monitor 2012 may create the following directory or directories:
| %APPDATA%\Security Monitor |
| %APPDATA%\Security Monitor 2012 |

