Personal Shield Pro
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 51 |
| First Seen: | June 10, 2011 |
| Last Seen: | April 18, 2018 |
| OS(es) Affected: | Windows |
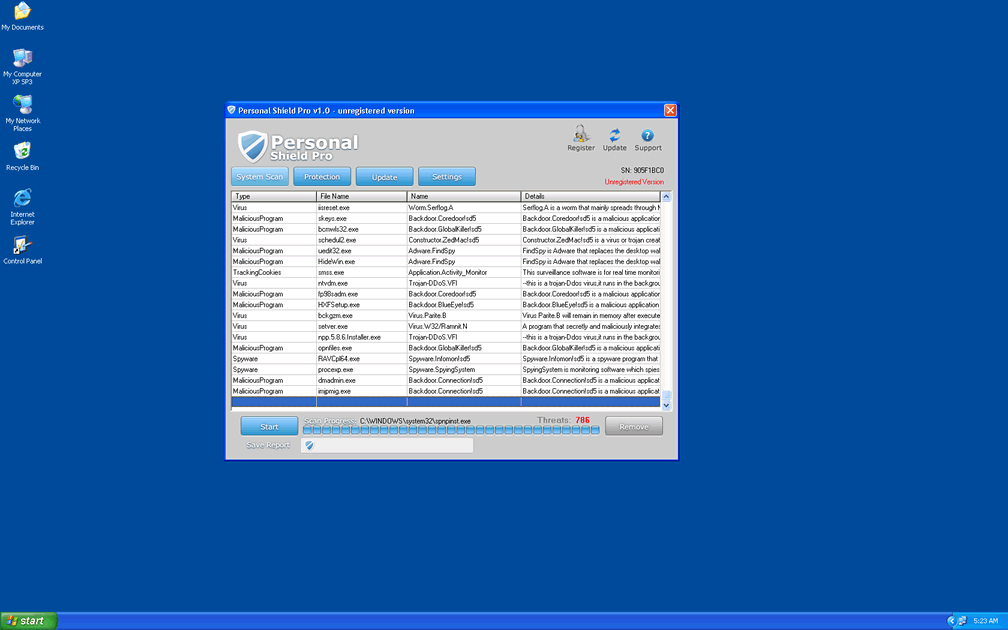
Personal Shield Pro Image
Personal Shield Pro is a rogue anti-virus program that can damage your computer and steal your credit card information. Personal Shield Pro is a clone of Ultimate Guard and XP Antivirus 2012. Rogue anti-virus programs are a category of malicious software known as scareware. These fake anti-spyware applications try to convince computer users that they need to buy a false anti-virus application. To convince computer users of this, Personal Shield Pro causes all kinds of problems on the infected computer. It will also display constant notifications claiming that the machine has any number of security problems. For example, Personal Shield Pro is known for detecting false infections like Adware.FindSpy, Email-Worm.Bagle, and Backdoor.Dreamy!sd6. It even takes the extra step of including malware descriptions of the supposed infections on the system. The problem is that these infections are completely imaginary. These are names and descriptions taken from virus databases. However, none of them are present on the infected system.
Table of Contents
How Does Personal Shield Pro Infect Users?
There is a website network dedicated to selling Personal Shield Pro on the Internet. There is a similar network for each of this program's clones, like Ultimate Guard or XP Antivirus 2012. Each of these websites displays pop-ups selling Personal Shield Pro. They also offer to perform a free online scan on your computer, supposedly to detect malicious software affecting your system. Worse of all, these advertisements may also deliver Personal Shield Pro by way of a Trojan. Eventually, each one of these websites will get to the point. Visitors will be directed to websites asking for the computer user's credit card information.
How Does the Personal Shield Pro Scam Work?
The main problem with Personal Shield Pro is that there is nothing beyond the authentic-looking interface. Personal Shield Pro uses Trojans and malicious scripts to cause problems on users' computers. Then Personal Shield Pro's interface advertises Personal Shield Pro as a solution to all of the problems. However, Personal Shield Pro will refuse to fix the problems, until the computer user enters his credit card information. The Trojan related to Personal Shield Pro has also been known to cause other problems on a computer system:
- Can alter browser settings to affect Internet browsing. It does this so that the user cannot use the Internet to get help. It also does this to redirect browsing to Personal Shield Pro websites.
- Can block access to the user's own files. It can also cause files to become hidden, and your computer to crash randomly.
- Constant pop-up notifications and security alerts. These can alarm users into paying for Personal Shield Pro. As anyone that has suffered through a Personal Shield Pro infection can tell you, these can also be really annoying.
Dealing with Personal Shield Pro
First of all, you need to keep in mind that anything Personal Shield Pro claims is most likely a lie. You should not give Personal Shield Pro your credit card information. You should also not take any action against files marked as infected. These are often essential system files; removing these files may cause irreparable damage to your computer. Avoid the temptation of giving in and paying Personal Shield Pro to leave you alone. Entering your credit card information will not make the problems stop. Worse, you'll be left at risk for identity theft and loss of money.
SpyHunter Detects & Remove Personal Shield Pro
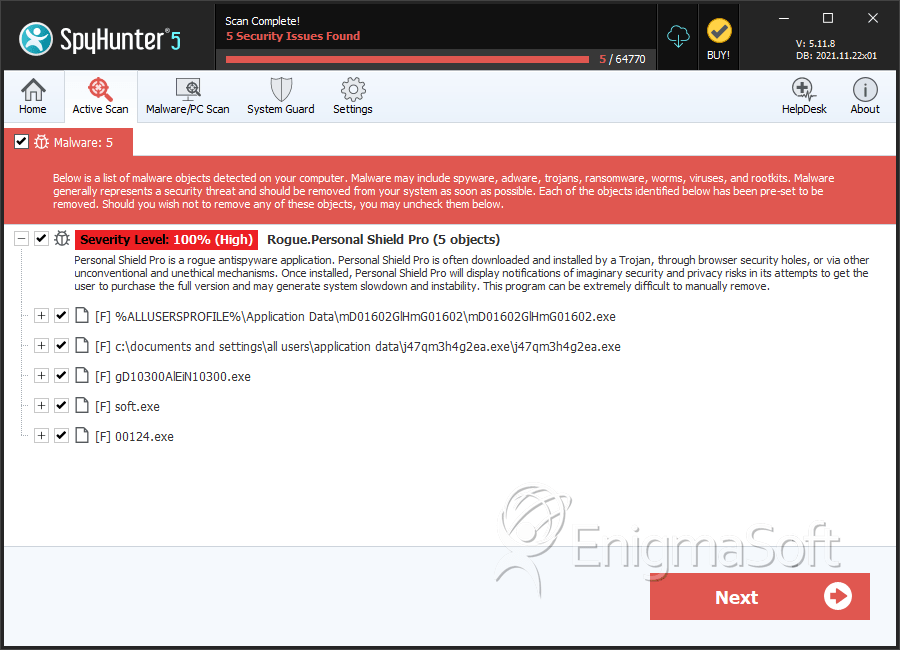
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | mD01602GlHmG01602.exe | 19dab1a5fdfff11669c4c1467c6baff0 | 45 |
| 2. | j47qm3h4g2ea.exe | a2ba596574440a49cb012ea30b148eab | 2 |
| 3. | %AllUsersProfile%\1030010300\1030010300.exe | ||
| 4. | %Temp%\[RANDOM CHARACTERS]\[RANDOM CHARACTERS].exe | ||
| 5. | %AllUsersProfile%\1030010300 | ||
| 6. | %Temp%\[RANDOM CHARACTERS]\ | ||
| 7. | %Documents and Settings%\All Users\Desktop\Personal Shield Pro.lnk | ||
| 8. | %AllUsersProfile%\1030010300\1030010300 | ||
| 9. | gD10300AlEiN10300.exe | 84a3010129e24ac954645ab0bfc488de | 0 |
| 10. | soft.exe | e28b3f70d688e78e6c7f8f711ae8174e | 0 |
| 11. | 00124.exe | 84d455e3b246818b8096a9b2762f8019 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.