Total Security
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 7,927 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 45 |
| First Seen: | July 24, 2009 |
| Last Seen: | May 6, 2024 |
| OS(es) Affected: | Windows |
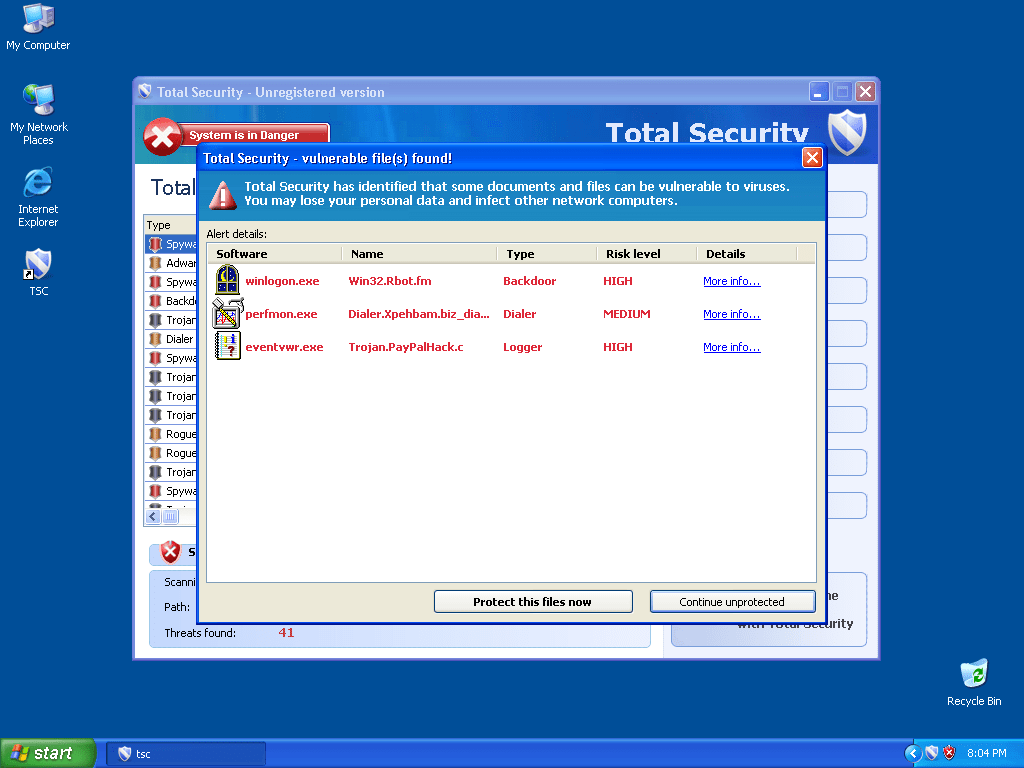
Total Security Image
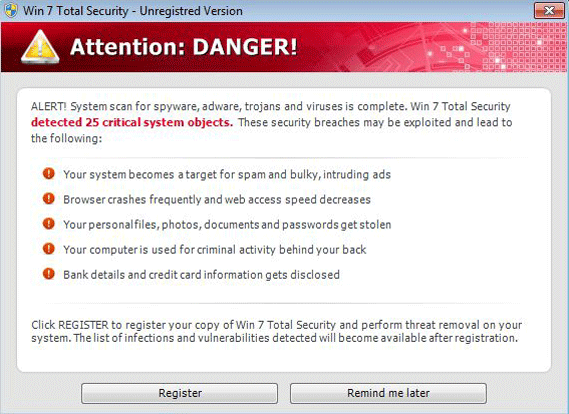
Total Security, also known as Total Virus Protection, Total Security 2009, Total Virus Protection 2009 or Total Security Pro is a rogue security program. Rogue security programs are fake security applications that are used as a way to scam unwary computer users. They are typically delivered by Trojans, like the Zlob Trojan or the Fake Microsoft Security Essentials AlertTrojan. Total Security has been associated with Trojan.Fraudpack and Trojan.FakeAlert. The removal of Total Security or its clones is strongly recommended by ESG security researchers. It is also imperative to make sure to remove the Trojan infection that installed the fake security program Total Security in the first place. This can be done by using an up-to-date anti-malware tool in Safe Mode. If you are receiving fake alerts, error messages or malware scans from Total Security, ESG security researchers recommend that you ignore all of these and that you immediately remove this fake anti-malware program from your computer.
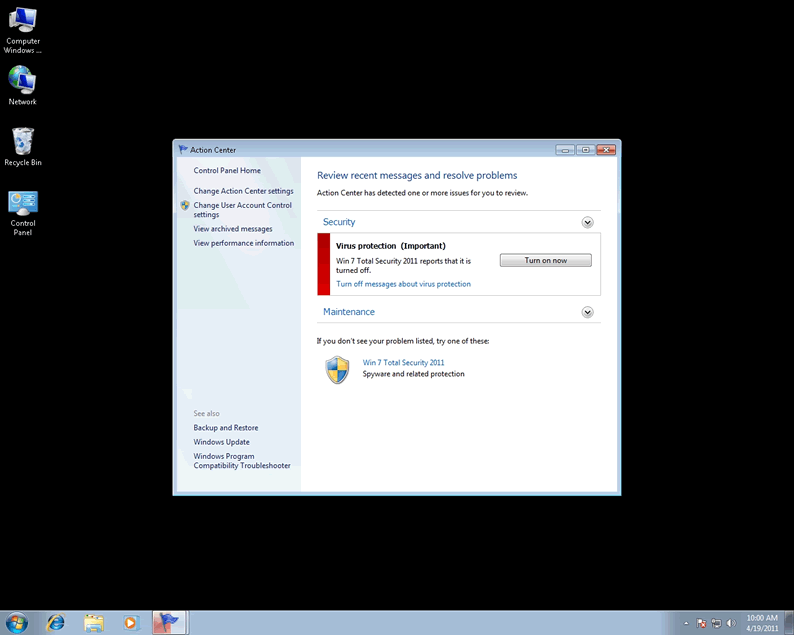
Most fake security program scams work in the same way. Typically, a Trojan installs Total Security in your computer through deceptive means. Usually, the Trojan will be disguised as something else, like a video codec or as a popular file on file sharing communities. Once the Trojan has been downloaded and installed, it will alter your system settings to display fake error messages. These error messages will typically claim to have discovered a malware infection on your computer. Then, they will recommend that you download Total Security to fix these problems. The error messages that these Trojans display are often disguised as legitimate error messages from your computer. However, reading them carefully will reveal a number of inconsistencies that are not congruent with what your operating system would normally display.
If a computer user falls for the Trojan's trap, the fake security program Total Security will be installed, and the computer will reboot. Total Security makes changes to the Windows Registry that allows Total Security to start up with Windows. This allows Total Security to block access to the desktop until Total Security finished running a fake scan of your computer. Regardless of the state of your computer, Total Security's fake scan will always return similar results. Total Security also causes a large number of problems on an infected computer; an infected computer will often run slowly, become unstable, and will display constant error messages and fake security alerts. Total Security attempts to charge its victims for a "full version" of this fake security program. Don't fall for the constant lies; ESG team of malware analysts recommends ignoring all alerts displayed by this fake security program.





Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| TrendMicro | TROJ_FAKEAV.AUH |
| NOD32 | Win32/Adware.Antivirus360 |
| McAfee | Generic Dropper.dz |
| eSafe | Win32.TrojanFakeXPA |
| AVG | FakeAlert.IB |
| TrendMicro | TROJ_FAKEAV.BRC |
| McAfee-GW-Edition | Trojan.FraudPack.unq |
| McAfee | FakeAlert-CN |
| Fortinet | W32/FraudPack.UNQ!tr |
| F-Secure | Trojan.Win32.FraudPack.unq |
| CAT-QuickHeal | Trojan.FakeRean |
| AntiVir | TR/FraudPack.unq |
| McAfee-GW-Edition | Trojan.Dldr.FraudLoa.XF |
| McAfee | Generic FakeAlert.c |
| Ikarus | Trojan-Downloader.FraudLoa |
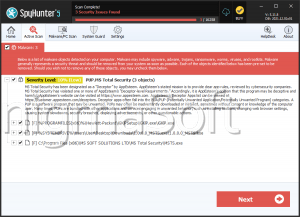
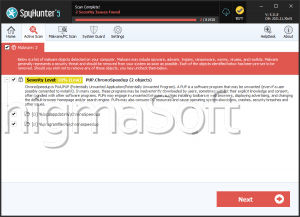
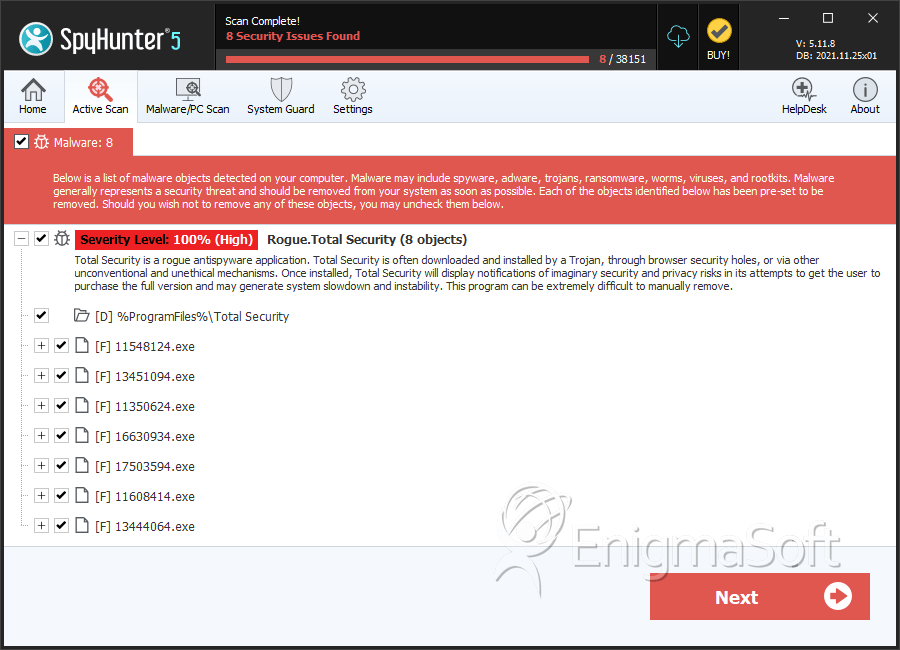
SpyHunter Detects & Remove Total Security
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | tsc.exe | 88e5d845aab95754ea30990aae77ab7c | 0 |
| 2. | tsc.exe | 75bcee693561a0cad8a2a2bfe04e90f3 | 0 |
| 3. | tsc.exe | 846aea02e9a0c72cc18fcd7dafface9d | 0 |
| 4. | tsc.exe | a047b3b0a53c46b2956e4de134aa78df | 0 |
| 5. | tsc.exe | 973adeacbc9167fb99a6a9167505e21a | 0 |
| 6. | tsc.exe | 0204361be928bf8cdb4bb3d67790541e | 0 |
| 7. | tsc.exe | 31bc83504f6bbda7772a8270629af8b7 | 0 |
| 8. | tsc.exe | 98d0970ea411dd7d3d8a0c57be157d91 | 0 |
| 9. | tsc.exe | eaa1f05cc5291278cbbf02e88342d7dc | 0 |
| 10. | 12931874.exe | 67a74888fab241d755651ba747c7c2d5 | 0 |
| 11. | 11242504.exe | 649bb1f470bf412ca14e1b56757319f5 | 0 |
| 12. | 10680464.exe | 2efc6d10996a66db68fd11fcb79e1a8d | 0 |
| 13. | 16849224.exe | 31808d15431c3cdbdbe225d357d9b94f | 0 |
| 14. | 14555314.exe | 4fcdf7b0b29f8475472d9cd2532bef05 | 0 |
| 15. | 19695784.exe | 2cf1b1114f131125fd93c27bc34c3cd2 | 0 |
| 16. | 18597034.exe | 10fb8949380da48c32c2e63e2d66cc51 | 0 |
| 17. | 12118904.exe | 582e8a00f47c669c62462806f685a0eb | 0 |
| 18. | 16864684.exe | 03a3f49f5cc910a0ec96ef3fbd3ae3dc | 0 |
| 19. | tsc.exe | 908a4df8bc14a4c458d15d7af3081029 | 0 |
| 20. | tsc.exe | 852d10dfb2d8bab2624dcb9599da3153 | 0 |
| 21. | tsc.exe | dedaa33b7ef1a9f7bd4f1542e48a07c3 | 0 |
| 22. | tsc.exe | b9c7778f60ab00805377c6c2cd4bf096 | 0 |
| 23. | tsc.exe | cdbb73331c2c4747283a70fa962b7a4a | 0 |
| 24. | 17076094.exe | 329d3db7d0ea93a74802bcc3be26d13c | 0 |
| 25. | tsc.exe | 0267cefe83702666b1846c57d1035450 | 0 |
| 26. | tsc.exe | e0847bb98636aa371361ce2863f32ee6 | 0 |
| 27. | tsc.exe | b0dd371ddc168c83abfb31e91856ca65 | 0 |
| 28. | tsc.exe | 26517b0f66b7ad516987182a181e7d8c | 0 |
Directories
Total Security may create the following directory or directories:
| %ProgramFiles%\Total Security |
URLs
Total Security may call the following URLs:
| starktyscan.com |