XP Antivirus 2012
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 15,794 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 32 |
| First Seen: | August 9, 2011 |
| Last Seen: | May 6, 2024 |
| OS(es) Affected: | Windows |
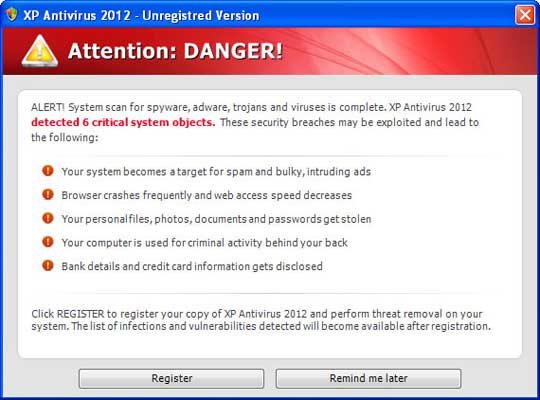
XP Antivirus 2012 Image
XP Antivirus 2012 is a rogue anti-virus application that exclusively affects computers with the Windows XP operating system. XP Antivirus 2012 is one of the many different disguises of the Ppn.exe executable file. Ppn.exe is characterized by its ability to slip on different disguises, depending on the operating system it is infecting. XP Antivirus 2012 is one of many possible names it can take, when invading a Windows XP operating system.
Table of Contents
XP Antivirus 2012 and the Many Faces of Ppn.exe
One of the main advantages Ppn.exe has over other files is its ability to change its name and appearance. The creators of rogue security applications often circumvent real security programs by creating clones of their harmful software. Clones are copies of the same program. They tend to have different names and often a different graphics theme. However, creating clones is not an easy task for criminals. The makers of Ppn.exe avoided the problem of constantly having to make clones of rogue security programs in a rather clever way. Instead of making clones, they gave the file the ability to download different skins to change its name and appearance each time. Giving Ppn.exe new faces and disguises to choose from is much easier than having to create entirely new versions of the same program. This new development quickly caught the attention of computer security experts all over the world.
How Ppn.exe Disguises Itself as XP Antivirus 2012
Just like a criminal master of disguise, Ppn.exe can choose from a virtual closet full of masks and disguises. There are three main sets of possible disguises. Each of these has skins corresponding to the three most widespread versions of the Windows operating system: Windows Vista, Windows 7, and Windows XP. When Ppn.exe is being installed, it checks the operating system of the computer it is invading. Then, it downloads a disguise corresponding to the operating system it found. XP Antivirus 2012 is one of the possible skins for computer users using the Windows XP operating system. Similar disguises in the other two sets of skin would be named something like Win 7 Antivirus 2012 or Vista Antivirus 2012.
What XP Antivirus 2012 Does to Your Computer
XP Antivirus 2012 has several avenues of attack, all of these designed to make the computer user panic and reveal his/her credit card information. Some of these are done directly in the foreground, while some are done without the computer user's knowledge. Here is a list of XP Antivirus 2012 actions that are clearly visible and easy to detect.
- XP Antivirus 2012 starts up without your authorization. XP Antivirus 2012 is often the first thing the computer user will see after Windows starts up.
- XP Antivirus 2012 will perform fake system scans, detect numerous false infections on your system.
- XP Antivirus 2012 alarms the computer user with a constant barrage of alerts, error messages, and pop-up notifications.
Using Trojans and dangerous scripts, XP Antivirus 2012 performs several actions in the background. Here is a list of possible actions that Trojans associated with XP Antivirus 2012 perform without your knowledge.
- Block or hide executable files, programs, and restrict access to system folders on your own computer.
- Block access to the Internet or change your browser settings to redirect you to XP Antivirus 2012's own websites.
- Can alter your security settings, registry, and other important system files to make your computer more vulnerable to attacks.
XP Antivirus 2012 belongs to the FakeXPA family of rogue security programs and nas among its clones Antivirus 360, AntivirusBEST, Nortel Antivirus, Alpha Antivirus, Anti-virus Professional, Antivirus 2010, Cyber Security, MaCatte Antivirus 2009, Eco Antivirus, Antivir, Personal Security, Ghost Antivirus, Antivirus 7, Antivirus GT, Earth Antivirus, Antivirus 8, AVG Antivirus 2011, E-Set Antivirus 2011, XP Antivirus 2013.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Antiy-AVL | AdWare/Win32.Zwangi.gen |
| AVG | OneStepSearcher.AG |
| Kaspersky | not-a-virus:AdWare.Win32.Zwangi.heur |
| NOD32 | a variant of Win32/Adware.OneStep.AI |
| Panda | Suspicious file |
| Kaspersky | UDS:DangerousObject.Multi.Generic |
| BitDefender | Trojan.Generic.KD.273651 |
| Kaspersky | HEUR:Trojan.Win32.Generic |
| Panda | Generic Trojan |
| AVG | Cryptic.CZI |
| Ikarus | Trojan.Win32.FakeAV |
| AntiVir | Joke/ExpProc.aelf |
| DrWeb | Trojan.AVKill.7187 |
| BitDefender | Trojan.Generic.KDV.269798 |
| Kaspersky | Hoax.Win32.ExpProc.aelf |
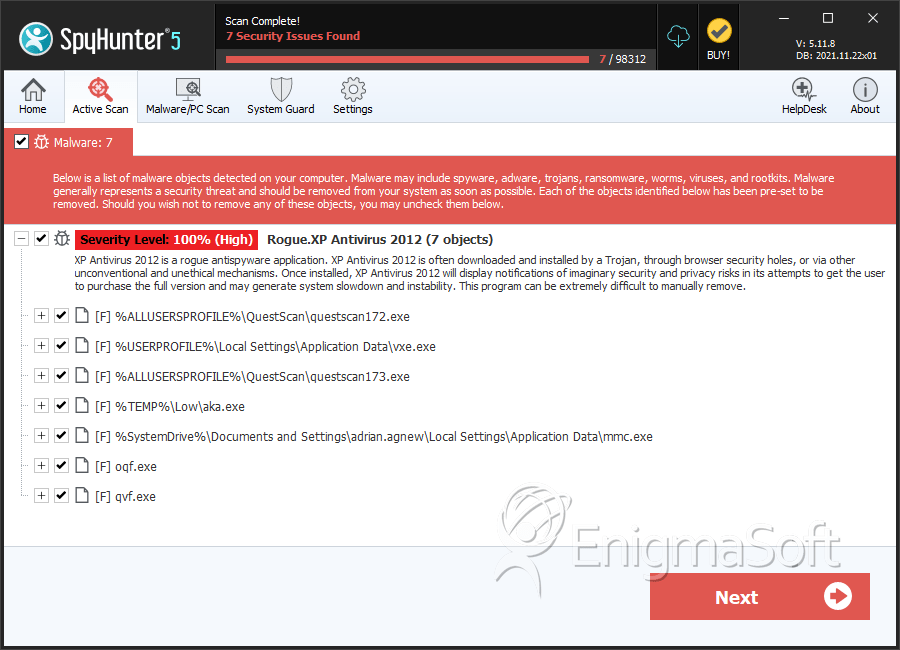
SpyHunter Detects & Remove XP Antivirus 2012
XP Antivirus 2012 Video
Tip: Turn your sound ON and watch the video in Full Screen mode.

File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | vxe (2).exe | 45d35cc0fbd7ffdf35f7ef86730cdc15 | 9 |
| 2. | questscan172.exe | 5bffd0b4493b22b8385b73e17638fff6 | 8 |
| 3. | aka.exe | 8759b185ac5d846a6665f47e0a9bdf13 | 4 |
| 4. | questscan173.exe | e53fb610fb4c8800db4dd1209066d2e0 | 2 |
| 5. | mmc.exe | 1434c50385a6e81f7ba5d081aafa9e0e | 1 |
| 6. | %AppData%\Local\random.exe | ||
| 7. | %UserProfile%Local SettingsApplication Datapw.exe | ||
| 8. | %UserProfile%AppDataLocalMSASCui.exe | ||
| 9. | %AppData%\Local\.exe | ||
| 10. | %Temp%\random.exe | ||
| 11. | %UserProfile%Local SettingsApplication Datavz.exe | ||
| 12. | %UserProfile%AppDataLocalvz.exe | ||
| 13. | %AllUsersProfile%\random.exe | ||
| 14. | %AppData%\Roaming\Microsoft\Windows\Templates\random.exe | ||
| 15. | %UserProfile%Local SettingsApplication DataMSASCui.exe | ||
| 16. | %UserProfile%AppDataLocalpw.exe | ||
| 17. | %UserProfile%AppDataLocalopRSK | ||
| 18. | %UserProfile%Local SettingsApplication DataopRSK | ||
| 19. | oqf.exe | 718b31c6d90a7731f88f92400cc1a212 | 0 |
| 20. | qvf.exe | f6dd62fb6849e79d8025036a097e8f80 | 0 |

Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.