Cyber Security
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 15,697 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 19 |
| First Seen: | December 1, 2009 |
| Last Seen: | May 6, 2024 |
| OS(es) Affected: | Windows |
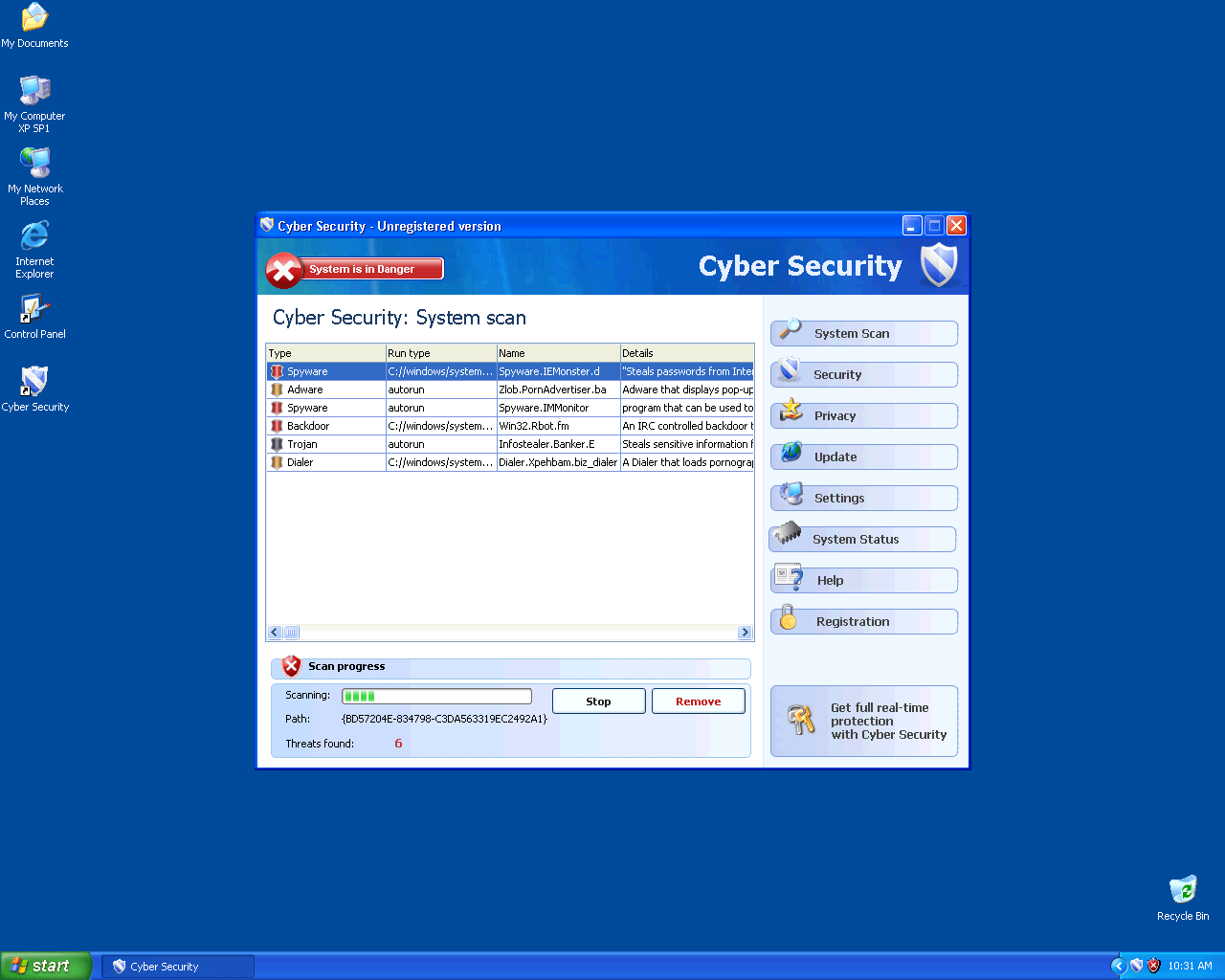
Cyber Security Image
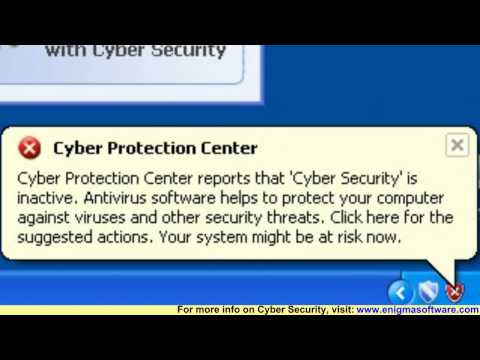
Cyber Security is a fake security application. Cyber Security comes from the same hackers that make and aggressively market the rogue anti-spyware programs that belong to the FakeXPA family. Cyber Security, through the use of fabricated warning popup messages and systems scans that return bogus results, is able to scare computer users into purchasing the full version of Cyber Security. Cyber Security is not able to detect and remove legitimate computer parasites including spyware, malware, Trojans and even viruses. Manual detection and removal of Cyber Security can be difficult to successfully perform.
Other members of the Cyber Security family include Antivirus 360, AntivirusBEST, Nortel Antivirus, Alpha Antivirus, Anti-virus Professional, Antivirus 2010, MaCatte Antivirus 2009, Eco Antivirus, Antivir, Personal Security, Ghost Antivirus, Antivirus 7, Antivirus GT, Earth Antivirus, Antivirus 8, AVG Antivirus 2011, E-Set Antivirus 2011, XP Antivirus 2013.



Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| NOD32 | a variant of Win32/Kryptik.BBU |
| McAfee-GW-Edition | Trojan.PCK.Katusha.E.1512 |
| McAfee+Artemis | Artemis!43CEF8481158 |
| AntiVir | TR/PCK.Katusha.E.1512 |
| NOD32 | a variant of Win32/Kryptik.BAQ |
| McAfee+Artemis | Artemis!B47FF6274C38 |
| Kaspersky | Packed.Win32.Katusha.e |
| Ikarus | Trojan.Win32.FakeAV |
| a-squared | Trojan.Win32.FakeAV!IK |
| Sophos | Troj/FakeAV-AHC |
| McAfee-GW-Edition | Trojan.Crypt.XPACK.Gen |
| McAfee+Artemis | Artemis!6443CA87E9B8 |
| K7AntiVirus | Trojan.Win32.Malware.1 |
| Ikarus | Packed.Win32.Katusha |
| CAT-QuickHeal | Trojan.Katusha.e |
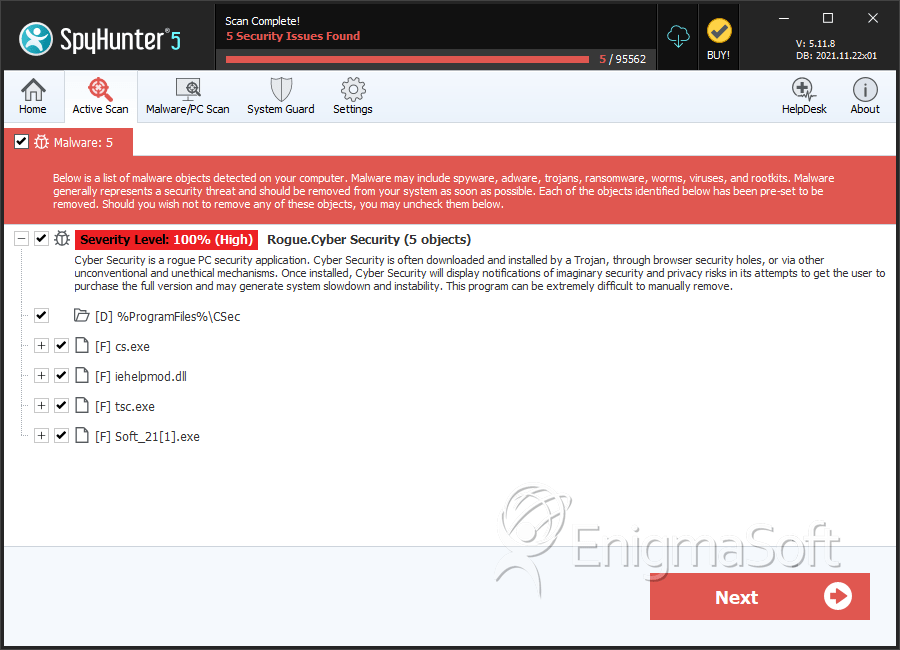
SpyHunter Detects & Remove Cyber Security
Cyber Security Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | cs.exe | 389a2325fc1fd7621e1172df2e066760 | 0 |
| 2. | cs.exe | 37093e2b885cc1554228773b28b9d215 | 0 |
| 3. | cs.exe | 95c9b493f30b17faa66740b9c4555002 | 0 |
| 4. | cs.exe | 7e6858e20f6db55fd100a99547bb618d | 0 |
| 5. | cs.exe | 57c1e358d8f0cb2377ad9c552f5b2b92 | 0 |
| 6. | cs.exe | 2269844aee2b118733064e7c940ac957 | 0 |
| 7. | cs.exe | 2f466f9174bf0ed10bb3c20591b37c6f | 0 |
| 8. | cs.exe | 8e81ab590f99cafc2e76db5fcb0c3ab7 | 0 |
| 9. | iehelpmod.dll | d851385da57f2e1a18fe7f79eb725946 | 0 |
| 10. | iehelpmod.dll | 33486e5bbd3e97a85441d2de1d00915e | 0 |
| 11. | cs.exe | 7227d11c88e05ccf73e69fdaef8b52ab | 0 |
| 12. | cs.exe | 0f389c167733fce56fa215e31d51caa9 | 0 |
| 13. | cs.exe | a1eb4cdb40bd1b0d6464f34f6702c684 | 0 |
| 14. | tsc.exe | 838caeb63b82925ea86a900c02d2d8c8 | 0 |
| 15. | tsc.exe | 6f81b9116bfaf79a14271c000a60610c | 0 |
| 16. | tsc.exe | d29c011c97cc6a412939b6037c641e7e | 0 |
| 17. | tsc.exe | c71c7d864408b4b64c542269f52af140 | 0 |
| 18. | cs.exe | ad62d1413a613031561a3c184f605d4a | 0 |
| 19. | cs.exe | 336235804fcdd192b0e38754f6062050 | 0 |
| 20. | Soft_21[1].exe | 6e160c22bb387fc307b0b5d1bef09208 | 0 |
| 21. | cs.exe | 68652018f3c1a04915c75cb3e9c7c167 | 0 |
| 22. | cs.exe | 6f57b4ec73e3b60d8bd659a7eb959edf | 0 |
| 23. | cs.exe | 0bfee00c1f76042e3ff6c2ea76e516f4 | 0 |
| 24. | cs.exe | 657b16b08888e043c490651b1f37284a | 0 |
| 25. | cs.exe | 43cef84811586d1e21b5e51557133923 | 0 |
| 26. | cs.exe | 5960dcf32bb4731c538adf40abf28470 | 0 |
Directories
Cyber Security may create the following directory or directories:
| %ProgramFiles%\CSec |

