Xorist Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 45 |
| First Seen: | April 13, 2016 |
| Last Seen: | September 15, 2020 |
| OS(es) Affected: | Windows |
The Xorist Ransomware is a family ransomware Trojans that are offered as RaaS (Ransomware as a Service). A marked increase in the Xorist Ransomware infections and requests for help with issues involving this threat was noticed by security analysts. The Xorist Ransomware variants are created by using a ransomware builder that makes it easy for con artists to create a custom version of this ransomware threat quickly. The ease with which the Xorist Ransomware variants can be customized makes it difficult for PC security researchers to offer solutions, since there are countless variants of this threat, using different encrypted file extensions, encryption, ransom messages and various other stratagems. Fortunately, PC security analysts have been able to find the ransomware builder that is used to create the Xorist Ransomware variants and create a decrypter for all threats in this family of ransomware Trojans. If your files have been encrypted by a variant of the Xorist Ransomware, the decryption utility can help you recover your files without having to pay the ransom.
Table of Contents
The Xorist Ransomware and the Many Variants of this Threat
It is easy to create a variant of the Xorist Ransomware if you have access to its builder. Currently, the builder for the Xorist Ransomware is called 'Encoder Builder v. 24' and it may be purchased on underground forums on the Dark Web. Once the con artists have the builder, they can fill in various check boxes and select their desired options to create a custom version of the Xorist Ransomware easily. They can use their method of choice to distribute their threats, which include spam email messages or harmful botnets. The Xorist Ransomware builder has a default ransom note message that contains the option to send an SMS text message with an ID number to a specific number. In this way, the fraudsters can match up the victim to their ID number and send them the password to decrypt their files once they have paid the ransom. All variants of a custom designed Xorist Ransomware executable will use the same password, which is selected (and can be selected at random) when creating the Xorist Ransomware variant.
Taking a Look at the Xorist Ransomware Variant Default Settings
The default encryption option for the Xorist Ransomware variants is TEA, and the default password is 4kuxF2j6JU4i18KGbEYLyK2d. The default version of the Xorist Ransomware uses the file extension EnCiPhErEd. The default ransom note associated with the Xorist Ransomware is named HOW TO DECRYPT FILES.txt and includes the following text:
Attention! All your files are encrypted!
To restore your files and access them,
please send an SMS with the text XXXX to YYYY number.
You have N attempts to enter the code.
When that number has been exceeded,
all the data irreversibly is destroyed.
Be careful when you enter the code!
By default, the Xorist Ransomware variants will target the following extensions (more may be added to the list):
*.zip, *.rar, *.7z, *.tar, *.gzip, *.jpg, *.jpeg, *.psd, *.cdr, *.dwg, *.max, *.bmp, *.gif, *.png, *.doc, *.docx, *.xls, *.xlsx, *.ppt, *.pptx, *.txt, *.pdf, *.djvu, *.htm, *.html, *.mdb, *.cer, *.p12, *.pfx, *.kwm, *.pwm, *.1cd, *.md, *.mdf, *.dbf, *.odt, *.vob, *.ifo, *.lnk, *.torrent, *.mov, *.m2v, *.3gp, *.mpeg, *.mpg, *.flv, *.avi, *.mp4, *.wmv, *.divx, *.mkv, *.mp3, *.wav, *.flac, *.ape, *.wma, *.ac3.
Con artists can use the Xorist Ransomware builder to change the ransom note text, encrypted file extensions, types of files targeted, amount of password attempts allowed, when to display the ransom message, TEA or XOR encryption, the decryption password, the icon for the threat's executable file, whether to alter the affected computer system's Desktop image, automatic start-up, if text ransom notes should be dropped, whether the Xorist Ransomware should be packed using UPX, etc. The Xorist Ransomware is not a particularly sophisticated ransomware Trojan infection. However, the fact that the Xorist Ransomware is so highly customizable and easy to create may pose the threat of bringing in numerous new infections and con artists to an already increased number of ransomware infections.
Update January 5th, 2019 — BooM Ransomware
The BooM Ransomware, or as its author calls it the 'Boom Ransomeware,' is an encryption Trojan that load a customized version of the Xorist Ransomware and a new GUI (General User Interface). The BooM Ransomware is produced with the Xorist Builder, but it differs from most versions we have recorded earlier like the Xorist-XWZ Ransomware and the Xorist-Frozen Ransomware. The BooM Ransomware is believed to spread among PC users via spam emails and fake hacking tools for social media services. The Ransomware operators are reported to use programs like 'hack facebook 2019' to deliver the threat payload.
The BooM Ransomware is known to create a process called 'Tempsvchost.exe' and 'BooM.exe' on the infected devices. The BooM Ransomware is designed to encipher data like photos, audio, video, text, PDFs and databases on the compromised machines. The BooM Ransomware enciphers files and removes their Shadow Volume Copies made by Windows to prevent data recovery. However, you should be able to use data backups created with other backup services available to the Windows users. The BooM Ransomware creates a program window titled 'Boom Ransomeware,' a text note called 'HOW TO DECRYPT FILES.txt' and leaves a desktop image background to inform victims of what happened with their data. The affected files receive the '.Boom' extension and something like 'Anthem 2019.mp4' is renamed to 'Anthem 2019.mp4.Boom.'
The desktop background provided by the BooM Ransomware is a black screen with red text on top that reads:
'ooooops You have been infected with a virus Boom Ransomeware
All your files have been encrypted To decrypt the encoder. enter PIN
To show you the password to decrypt files
see you soon'
The program window includes a new icon — a red lock icon, the user's account name and a link to an account on Facebook belonging to someone named Mohamed Naser Ahmed. At the time of writing, the user has changed the name to 'Ibrahim Rady' and the page remains active. The text on the 'Boom Ransomeware' window reads:
'Welcome
in Boom Ransomeware
Ooooops All Your Files Have Been
Encrypted With Password
To Show The Password You Enter PIN First
See you soon
password::: [TEXT BOX] [Copy|BUTTON]
Enter PIN [TEXT BOX] [Show password|BUTTON]
[Get PIN|BUTTON]'
Strangely, the operators of the BooM Ransomware choose to negotiate with the infected users via Facebook. The note mentioned above — 'HOW TO DECRYPT FILES.txt' — can be found on the desktop and includes the following message:
'How to decrypt files
Get your pin
Pur it in the virus
In order to extract the password to decrypt the files
In a folder on your desktop
Then put it in a password in the small window that will show you
For pin
Talk to me on Facebook
My name = Mohamed Naser Ahmed
my ID = 100027091457754'
However, computer researchers discovered a hardcoded PIN and password in the BooM Ransomware. PC users that may have been compromised during the initial release of the BooM Ransomware may try to enter the PIN '34584384186746875497' and the password 'B3ht4w316MsyQS47Sx18SA4q' into the 'Boom Ransomeware' program window. We are not sure if the PIN and password mentioned before would work for everyone, but you should try them. Don't pay money to the accounts promoted through the BooM Ransomware and avoid contact with potential "decryption services" paid in Bitcoin. It is better to get help from a computer technician and your preferred cybersecurity vendor. It may be possible to decode the data affected by the BooM Ransomware if you contact experts working with Ransomware samples.
Detection names for the BooM Ransomware include:
Artemis!E8E07496DF53
HEUR/QVM11.1.5569.Malware.Gen
Malware@#38vlyeighbrin
Ransom:Win32/Sorikrypt.A
Ransom_Sorikrypt.R014C0DLN18
TR/Ransom.Xorist.EJ
TrojWare.Win32.Kryptik.ER@4o1ar2
Trojan ( 001f8f911 )
Trojan-Ransom.Win32.Xorist.ln
Trojan.GenericKD.40867299 (B)
Trojan.Ransom.AIG
Trojan.Win32.Xorist.4!c
malicious.92f093
malicious_confidence_100% (W)
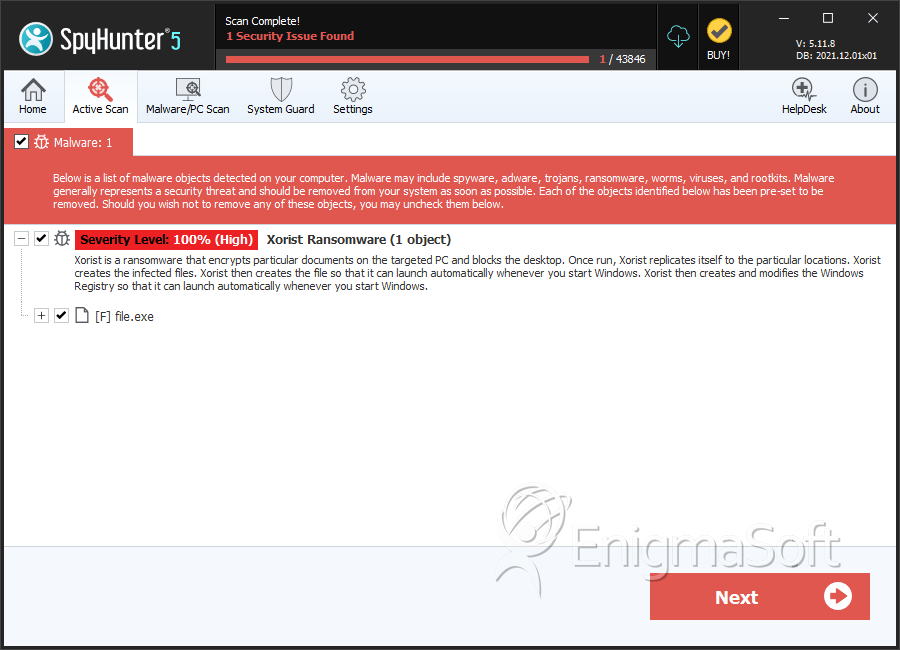
SpyHunter Detects & Remove Xorist Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | e9db7fe38dfea5668c74d6f192ae847b | 1 |
| 2. | file.exe | 27def0c68ee542333a8a99995429273a | 1 |
| 3. | file.exe | 1a2bcbcf04aeb44e406cc0b12e095fb4 | 0 |