Win 7 Antivirus 2012
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 12,989 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 307 |
| First Seen: | December 5, 2011 |
| Last Seen: | September 5, 2023 |
| OS(es) Affected: | Windows |
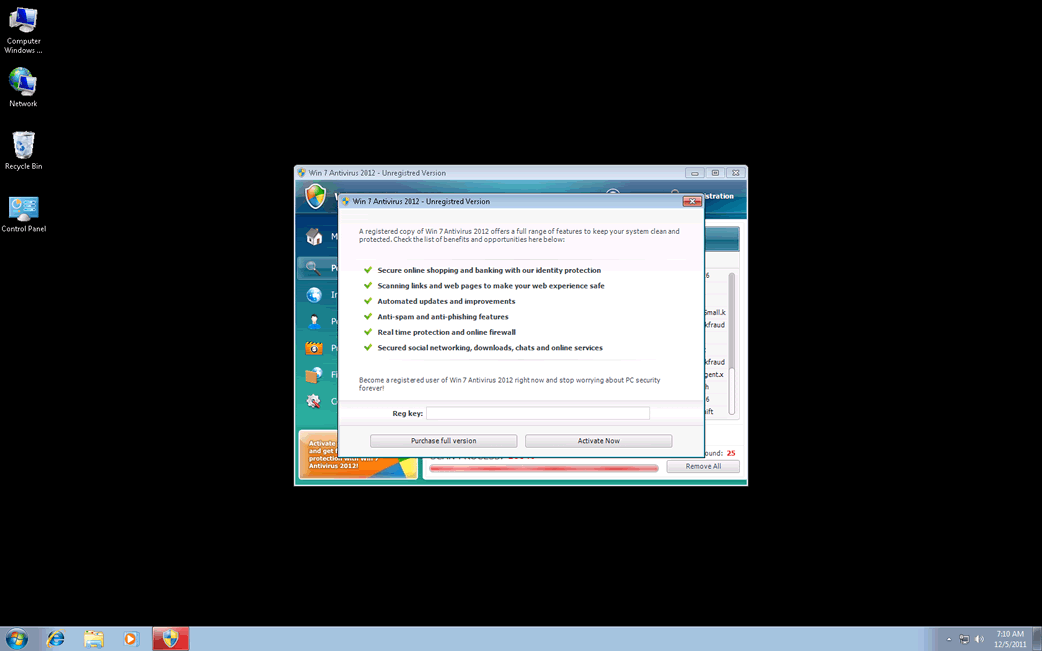
Win 7 Antivirus 2012 Image
Win 7 Antivirus 2012 is a dangerous application that affects users with the Windows 7 operating system. To be more accurate, Win 7 Antivirus 2012 is one of numerous possible names and skins for the Ppn.exe file process, which can affect most Windows systems. However, this process is known for changing its name and downloading skins specific to the user's operating system, with the Win 7 Antivirus 2012 rogue security application being one of those, corresponding to Windows 7.
Table of Contents
Win 7 Antivirus 2012 Clones and Copies
There are dozens of known clones and copies of this rogue anti-virus application, all belonging to the FakeRean family, with new ones being released every day. However, most of these fake security tools correspond to the same underlying process, Ppn.exe. There are other similar files, usually with names that are three seemingly random letters long. Ppn.exe and similar processes download specific themes and skins when they are installing themselves into a user's computer. There are three sets of Win 7 Antivirus 2012 clones that are currently known. Each of these sets has dozens of different possible names and skins that correspond to three of the most common Windows operating systems. These are Windows XP, Windows Vista, and Windows 7. Win 7 Antivirus 2012 will only show up on Windows 7 machines, and the corresponding programs for other operating systems can be named something like XP Anti-Virus 2012, or Vista Anti-Virus 2012.
Other clones of Win 7 Antivirus 2012 include Antivirus 2008, Windows Antivirus 2008, Vista Antivirus 2008, Antivirus Pro 2009, AntiSpy Safeguard, ThinkPoint, Spyware Protection 2010, Internet Antivirus 2011, Palladium Pro, XP Anti-Virus 2011, CleanThis, PC Clean Pro, XP Home Security 2012, Windows Clear Problems, XP Security 2012, Antivirus PRO 2015.
Background and Foreground of Win 7 Antivirus 2012 Actions
Win 7 Antivirus 2012 performs two main functions. On the foreground, completely visible to the user, is a series of escalating system alerts and fake virus scans. These alerts are designed to alarm, causing the panicked computer user to enter his credit card information to save the data on his computer. On the background, completely hidden, Win 7 Antivirus 2012 uses its partner, a Trojan, to perform dangerous modifications to the user's system. These modifications can compromise the computer's security, report the user's browsing habits and personal information to a third party, and make it next to impossible to remove manually Win 7 Antivirus 2012.
Special Removal Considerations for Win 7 Antivirus 2012
The best way to get rid of Win 7 Antivirus 2012 is by using a trustworthy anti-virus or anti-malware utility. It is also possible to remove Win 7 Antivirus 2012 manually, by deleting the registry entries, DLL files, and processes associated with Win 7 Antivirus 2012. However, this can be somewhat difficult because the Trojan that installed Win 7 Antivirus 2012 blocks the Task Manager and essential system files, under the pretext that they have been infected. There's a couple of steps specific to the removal of the Ppn.exe process that can be also used to remove Win 7 Antivirus 2012. First of all is entering a registration key proven to work. These registration key changes every day, and can be found with a quick search on the Internet. This will not remove Win 7 Antivirus 2012 but will remove most of the system alerts and annoying pop-up notifications. Another step that can help is changing the system date, setting it one full week ahead. If an infected user does these two things, he/she may gain access to the necessary parts of the computer for removing Win 7 Antivirus 2012.








Win 7 Antivirus 2012 Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%\Local\[RANDOM CHARACTERS].exe | |
| 2. | %AppData%\Roaming\Microsoft\Windows\Templates\[RANDOM CHARACTERS] | |
| 3. | %AppData%\Local\[RANDOM CHARACTERS] | |
| 4. | %AllUsersProfile%\[RANDOM CHARACTERS] | |
| 5. | %Temp%\[RANDOM CHARACTERS] |

