CleanThis
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | March 21, 2011 |
| Last Seen: | January 29, 2019 |
| OS(es) Affected: | Windows |
CleanThis Image
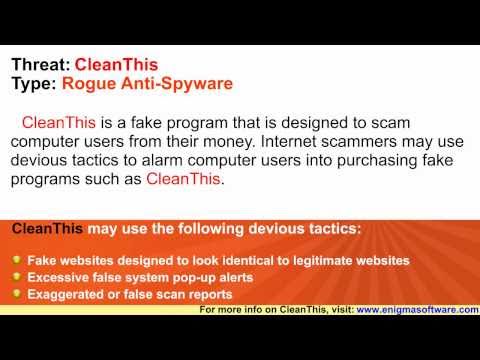
Don't confuse CleanThis with a real anti-virus program. Although the creators of CleanThis obviously want to fool people into confusing CleanThis with a specific malware-analysis tool, CleanThis is nothing but malware.
Table of Contents
The Program that CleanThis Rips Off
CleanThis is a clear attempt at mimicking the name and appearance of a program called HijackThis, published by Trend Micro. Aside from the similarity between the names, CleanThis also uses the HijackThis logo in its phony interfaces. (It's a man with a red hat and trench coat holding a magnifying glass.) HijackThis is widely used by malware researchers and technical support personnel in order to identify changes made to a computer by malware, which makes HijackThis a very well-recognized anti-malware tool, and an easy target for a fake security software scam. Trend Micro does also make software that removes malware, but that software is not CleanThis. CleanThis has no association with Trend Micro or any other reputable company or organization, and the creators of CleanThis are abusing the good reputation of HijackThis in order to propagate their malicious fake security software.
Symptoms of the CleanThis Infection
In terms of the symptoms of an infection with CleanThis, this rogue anti-virus application is entirely typical, despite CleanThis's superficial attempts at making itself look similar to HijackThis. The infection process for CleanThis begins with a Trojan, and in this case, that Trojan is the Fake Microsoft Security EssentialsAlert Malware. The Trojan may be hidden in a file downloaded from a disreputable or malicious website, or it may download itself to your computer when you click on a malicious link. Either way, the first sign you'll see that the Trojan is on your computer is that it will start showing alerts that look as though they are coming from Microsoft Security Essentials.
The first alert will warn that an unidentified Trojan has been found by Windows, and after that you'll get an alert that claims to identify the virus as a specific Trojan. At that point, the fake malware alert will suggest that you download some kind of anti-virus program in order to remove this so-called threat, and CleanThis will provide you with a button in order to start the download. If you start the download, what you're downloading is malware, and CleanThis is one of the fake security programs that you might wind up with. Reportedly, even if you do not agree to download the rogue program, it may be possible for CleanThis to be downloaded and installed by the Trojan. Then, CleanThis will be configured to run every time you start Windows.
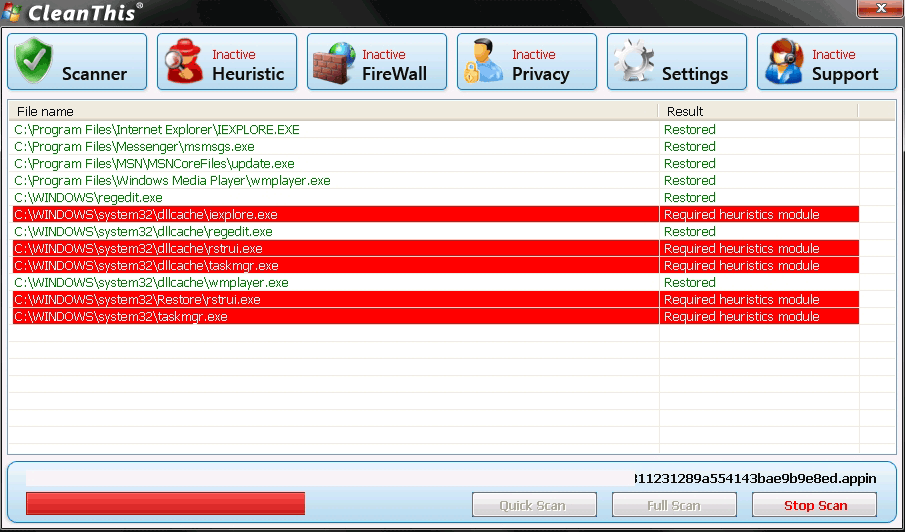
The fake user interface for CleanThis will appear as soon as Windows starts, before you see the taskbar and desktop. CleanThis will use this interface to play some animations simulating a scan of your computer. It is not possible to close the CleanThis window and skip the fake scan, either; CleanThis will prevent that from happening and then tell you that if you want to be able to skip the interface in the future, you need to check your settings. (There aren't any settings to check, of course.) The phony CleanThis scans will always return long lists of results, regardless of the actual condition of your computer, because the results are completely fake. They are only there to scare you, because as soon as the scan finishes and CleanThis presents the list, CleanThis will recommend that you purchase a license for CleanThis in order to enable the program to remove the detected threats. Although it is possible to follow the prompts provided by CleanThis to a website where you can pay for a "license" for the malware, doing so will not do you any good. The entire thing is a scam; CleanThis will never gain any functionality or usefulness, and it makes no difference how much you pay.
CleanThis will remind you to "acivate" or "license" your copy of its program by causing pop-up warnings and alerts to appear, once you have cleared the interface and made it to the desktop. CleanThis will even prevent your real anti-virus software and several key system tools, like Task Manager and Regedit, from running – and CleanThis will do so along with a message that says that these programs have been disabled for the safety of your computer, because they are "malicious." You may even find that your Internet connection seems slower than usual, or that your computer as a whole runs more slowly, as CleanThis consumes system resources.
CleanThis is essentially identical to the rogue anti-virus applications ThinkPoint and Palladium Pro, which are notoriously dangerous. So, although CleanThis emerged as a threat in March 2011, CleanThis is part of a family of malware that has been causing infections since at least fall 2010.















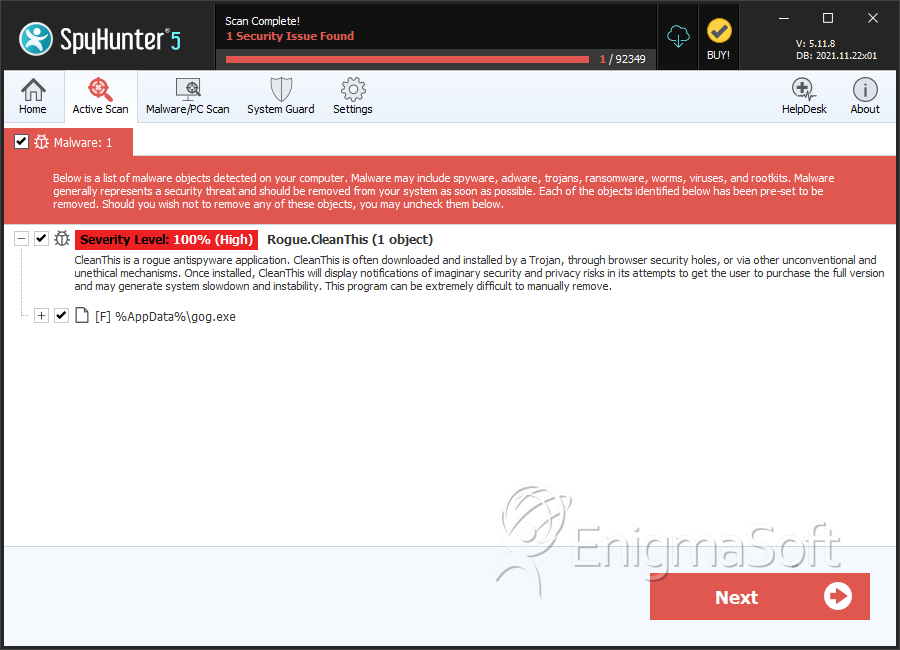
SpyHunter Detects & Remove CleanThis
CleanThis Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | gog.exe | 17fc78683265940605870d1c789b4720 | 0 |

