Are You Sure You’re NOT Infected with Malware?
Don’t Fall Victim to Malware or Ransomware Attacks!
Detect and remove malware, viruses, ransomware & other threats for FREE! Get Protected with SpyHunter.
Download SpyHunter (FREE Trial!)*A rogue anti-virus program is a type of computer parasite not unlike that of a Trojan horse virus. Rogue anti-virus programs are typically installed onto your computer system due to web-surfing activities and the acceptance of advertisements claiming that leaving the current website will leave a trace or bug infection that their product can remove.
Rogue anti-virus applications differ from Trojan viruses by utilizing scare tactics in order to intimidate you into purchasing their product. In the case that one has already been installed on your system, many infections are possibly installed along with it will not appear in any “Add or Remove Programs” menu.
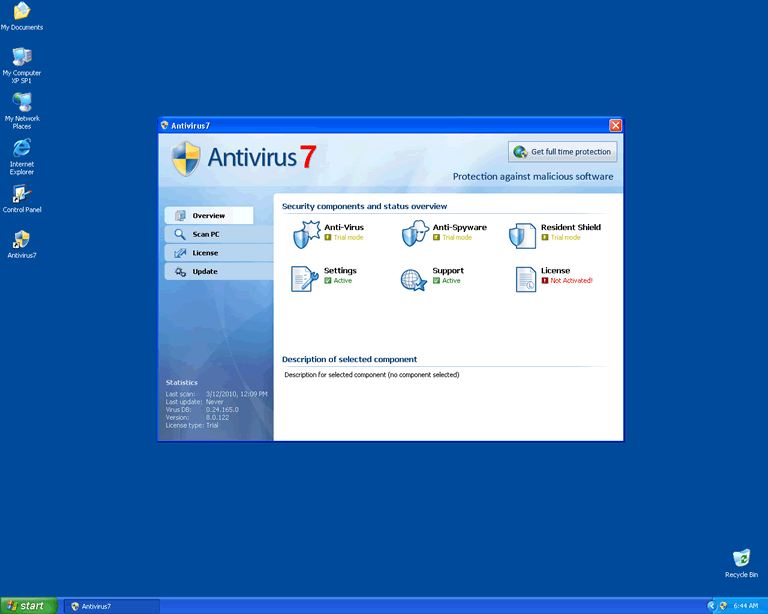
Example of a Rogue Anti-Virus program interface
The Internet landscape is peppered with distributors of rogue anti-virus programs, thus making it hard for PC users to distinguish between the good anti-virus programs and the bad or rogue anti-virus programs. So what makes a program rogue? A rogue computer program is any program that is dishonest and on the surface offers one thing but in actuality does another, especially something that is harmful.
Rogue anti-virus programs mimic the look and behaviors of legitimate anti-virus programs to fool unsuspecting PC users into trusting its offers. Rogues anti-virus programs offer to block or remove infections, when in fact they do the opposite. Rogue anti-virus programs stage a security breach and use fake alerts, scans, and reporting in hopes of scaring the victim into buying fraudulent software, much like rogue anti-spyware programs. However, while the victim eyes are busy absorbing the explosion on their screen (i.e. presentation of fake alerts, scans, and reporting), the rogue anti-virus program, courtesy of its engineer, a Trojan, wages an underlying attack.
Most rogue anti-virus programs are distributed as follows:
Most rogue anti-virus programs behave the same:
Hidden (happening in the background)
Visual (happening in the foreground)
The above is typical behavior of most rogue anti-virus programs. Unfortunately, buying the rogue anti-virus program will not end the nightmare. In fact, by entering your credit card information you will be helping a cybercriminal possibly ruin your financial future. Unless you like throwing away your money and turning your computer over to a hacker, you will need to remove the rogue anti-virus program and associated files or components. However, removal may be easier said than done. Trojans and other malicious programs are known to use rootkit technology to mask and bury malicious files from persons or tools hoping to remove it. So while manual removal is not impossible, it will be hampered by obfuscation tricks, i.e. polymorphic coding and rootkits.
Trojans are stealth and can make system changes comparable to that of an IT expert. One change will involve editing the registry and adding an auto run key that runs the malicious executable each time the operating system is booted. Another change, thanks to rootkit technology, involves masking file names so they read the same as legitimate operating system files. If you are not familiar with the operating system structure, you may not realize the malicious file is mapped incorrectly. However, if you delete the wrong file, you could corrupt your own hard drive and erase valuable data. Therefore, use of a professional antimalware solution containing an anti-rootkit component is highly recommended. A stealth antimalware solution can not only uproot hidden malware in the kernel or BIOS and remove without causing further harm, but too restored corrupted files, i.e. operating system files the Trojan hooked or injected with malicious code.
In order to keep malware at bay, it will be important to keep an antimalware solution in effect at all times, keep software updated and patched, and follow safety guidelines when using the Internet. Otherwise, if you are using Microsoft Windows, you can expect a repeat performance at next and every boot thereafter.
| # | Threat Name |
Severity Level
Severity Level: The determined severity level of an object, represented
numerically, based on our risk modeling process and research, as explained in our
Threat Assessment Criteria.
|
Alias(es) |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|---|
| 1. | MAC Defender | |||
| 2. | Windows Guardian Angel | 100 % (High) | ||
| 3. | Vista Defender Pro | |||
| 4. | Quick Heal Antivirus Plus 2009 | |||
| 5. | Net Protector AntiVirus 2010 | |||
| 6. | Windows Antivirus Adviser | 100 % (High) | 2 | |
| 7. | Total PC Defender 2010 | 100 % (High) |
Mal/Koobface-E Suspicious file Trojan.Win32.VBKrypt.nt |
|
| 8. | Sirius XP/Vista/Win7/Win8 Antivirus 2014 | |||
| 9. | AKM Antivirus 2010 Pro | 100 % (High) |
Trojan:Win32/FakeScanti Trojan.Win32.FakeScanti Win32/Rogue.BWShield2s_i |
22 |
| 10. | AntivirusVista | 100 % (High) |
Suspicious.Insight TROJ_FAKEAL.SMDO VirTool:Win32/Obfuscator.HG |
|
| 11. | VirusCure | |||
| 12. | Rogue Anti-Virus Program.QA | 100 % (High) | 16 | |
| 13. | Vista AntiVirus | |||
| 14. | Powerful PC Protection | |||
| 15. | Win 7 Antivirus Pro | |||
| 16. | XP Antivirus 2013 | 50 % (Medium) | 27 | |
| 17. | Win 7 Antivirus 2014 | |||
| 18. | Paladin Antivirus | 100 % (High) |
Trojan.Win32.Generic!BT Heuristic.LooksLike.Trojan.TDss.B Virus.Win32.Heur |
39 |
| 19. | Win 7 Antivirus Plus 2013 | 20 % (Normal) | 3,806 | |
| 20. | Antivirus Scan | 100 % (High) | ||
| 21. | Wireshark Antivirus | 100 % (High) |
Trojan.FakeAV Suspicious file Artemis!EAC83866829C |
1 |
| 22. | XP Home Security 2012 | 100 % (High) | ||
| 23. | Windows Secure Kit 2012 | 20 % (Normal) | ||
| 24. | Windows No-Risk Center | 20 % (Normal) | ||
| 25. | Antivirus Pro 2017 | 100 % (High) | 18 | |
| 26. | Vista Security 2013 | 10 % (Normal) | 2 | |
| 27. | Antivirus Live 2010 | |||
| 28. | Windows Safety Checkpoint | 100 % (High) | 1 | |
| 29. | Win 8 Security System | 100 % (High) | 339 | |
| 30. | Win 8 Protection 2013 | 20 % (Normal) |
Last updated: 2026-05-31
| Threat Name |
Severity Level
Severity Level: The determined severity level of an object, represented
numerically, based on our risk modeling process and research, as explained in our
Threat Assessment Criteria.
|
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 'Internet Security – designed to protect' Fake AV | 100 % (High) | 1,241 |
| A-Fast Antivirus | 100 % (High) | 13 |
| A-Secure 2015 | 100 % (High) | 0 |
| Activeris Antimalware | 10 % (Normal) | 5,491 |
| AKM Antivirus 2010 Pro | 100 % (High) | 22 |
| Albinos Defender | 20 % (Normal) | 0 |
| AlfaAntivirus | 100 % (High) | 10 |
| Anit-Virus Scanner | 20 % (Normal) | 68,776 |
| Anti Virus Armor | ||
| Antimalware - Proven Antivirus Protection | 20 % (Normal) | 0 |
| Antiprotect | ||
| Antivir 2010 | ||
| Antivir Antispyware | ||
| Antivir Pro | ||
| Antivir Solution Basic | ||
| Antivir Solution Plus | ||
| Antivirii 2011 | 100 % (High) | 11 |
| AntivirSolution | ||
| Antivirus 10 | 100 % (High) | 9 |
| Antivirus 2010 RTK | ||
| Antivirus 2010 Security Center | ||
| Antivirus 7 | 100 % (High) | 15 |
| Antivirus Action | 100 % (High) | 0 |
| Antivirus Antimalware 2011 | ||
| Antivirus Center | 100 % (High) | 356 |