Vista Antivirus Pro 2013
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 3,737 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 6,438 |
| First Seen: | September 22, 2014 |
| Last Seen: | September 20, 2023 |
| OS(es) Affected: | Windows |
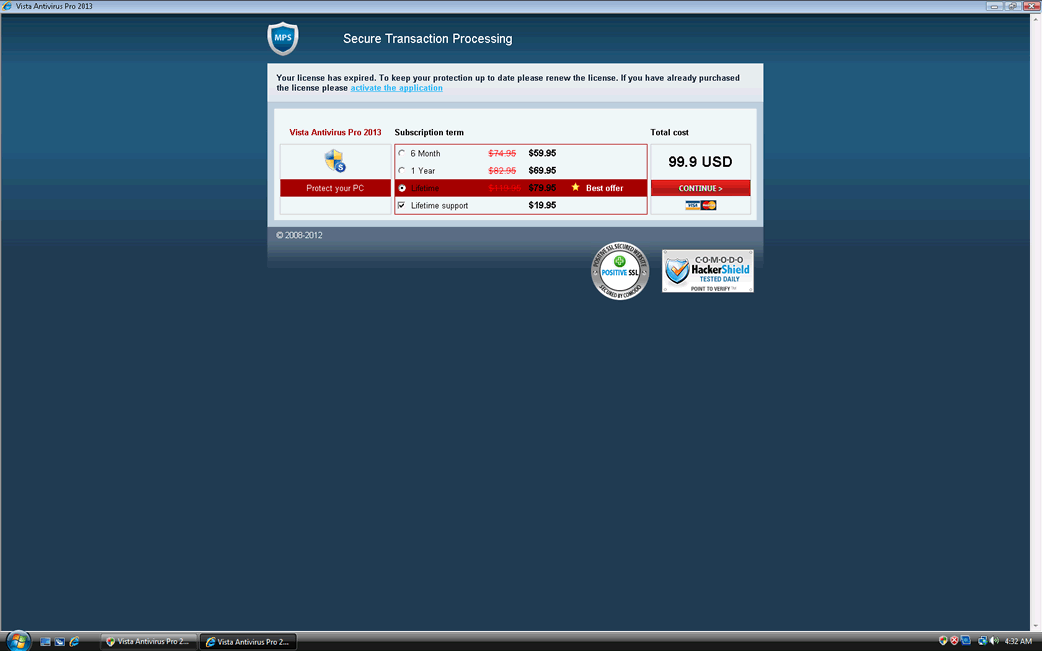
Vista Antivirus Pro 2013 Image
Vista Antivirus Pro 2013 is one of the many rogue security applications that are part of a notorious family of malware known as FakeRean or Braviax. Fake security programs like Vista Antivirus Pro 2013 are used to carry out a well known online scam that is used to steal money from inexperienced computer users. Every year updated versions of malware in this family are released. Vista Antivirus Pro 2013 is part of a large batch of rogue security software released in October of 2012. Although the programs themselves are essentially the same from year to year, their names are updated with the current year – as 2013 approaches, ESG security researchers have started to observe the '2013' versions of these fake security programs being released.
Vista Antivirus Pro 2013 and its clones are typically quite easy to detect. These fake security programs use identical interfaces and use a naming pattern that is probably generated automatically. As can be observed in Vista Antivirus Pro 2013, these fake security programs tend to use names that are made up of three distinct elements:
- These fake security programs' names typically being with the targeted operating system's name. While Vista Antivirus Pro 2013 targets computers running Windows Vista, there are variants of Vista Antivirus Pro 2013 named XP Antivirus Pro 2013, Win 7 Antivirus Pro 2013 or Win 8 Antivirus Pro 2013, installed on the operating system that corresponds to each fake security program's name.
- After the targeted operating system's name, these fake security applications will typically use a misleading generic term that is commonly used to name security software. Examples of this include words like antivirus, antimalware, antivirus pro or home security.
- To make it appear as if these fake security programs are newly released with current technology, they will often have the current year added to the end of each program's name, as is the case of Vista Antivirus Pro 2013. There are versions of Vista Antivirus Pro 2013 ending with 2009, 2010, 2011 and 2012 which correspond to previous releases of this rogue security application.
There are also versions with different names such as Antivirus 2008, Windows Antivirus 2008, Vista Antivirus 2008, Antivirus Pro 2009, AntiSpy Safeguard, ThinkPoint, Spyware Protection 2010, Internet Antivirus 2011, Palladium Pro, XP Anti-Virus 2011, CleanThis, PC Clean Pro, XP Home Security 2012, Windows Clear Problems, XP Security 2012, Antivirus PRO 2015.
The Vista Antivirus Pro 2013 scam is not sophisticated. These fake security programs cause problems on the infected computer deliberately and then claim that it is necessary to purchase an upgrade in order to stop these problems. Instead, ESG malware researchers advise removing Vista Antivirus Pro 2013 with the help of real anti-malware program.
Table of Contents
Vista Antivirus Pro 2013 Technical Report
As new Vista Antivirus Pro 2013 details are reported by our customers and findings from our Threat Research Center, we will update this section.







Fake message for Vista Antivirus Pro 2013:
The following fake error message(s) appears for Vista Antivirus Pro 2013:
| Vista Antivirus Pro 2013 Firewall Alert Vista Antivirus Pro 2013 has blocked a program from accessing the internet Internet Explorer is infected with Trojan-BNK.Win32.Keylogger.gen Private data can be stolen by third parties, including credit card details and passwords |
Vista Antivirus Pro 2013 creates the following files in the system:
| %CommonApplData%\[RANDOM CHARACTERS_2] |
| %LocalAppData%\[RANDOM CHARACTERS_2] |
| %Temp%\[RANDOM CHARACTERS_2] |
| %UserProfile%\Templates\[RANDOM CHARACTERS_2] |
Vista Antivirus Pro 2013 creates the following registry entries:
| HKEY_CURRENT_USER\Software\Classes\.exe |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\open\command |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\runas |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\open\command\IsolatedCommand "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\runas\command\ "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\open\command\IsolatedCommand "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\runas\command\ "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\open |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\DefaultIcon |
| HKEY_CURRENT_USER\Software\Classes\.exe\DefaultIcon |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\open |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\open\command\ "[RANDOM CHARACTERS_1].exe" -a "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\ Application |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\open\command\ "[RANDOM CHARACTERS_1].exe" -a "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\runas\command |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\Content Type application/x-msdownload |
| HKEY_CURRENT_USER\Software\Classes\.exe\Content Type application/x-msdownload |
| HKEY_CURRENT_USER\Software\Classes\.exe\ [RANDOM CHARACTERS_0] |
| HKEY_CURRENT_USER\Software\Classes\.exe\DefaultIcon\ %1 |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\runas\command |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0] |
| HKEY_CURRENT_USER\Software\Classes\.exe\shell\runas\command\IsolatedCommand "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\runas |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\runas\command\IsolatedCommand "%1" %* |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\shell\open\command |
| HKEY_CURRENT_USER\Software\Classes\[RANDOM CHARACTERS_0]\DefaultIcon\ %1 |
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%\Roaming\Microsoft\Windows\Templates\[RANDOM NUMBERS AND CHARACTERS] | |
| 2. | %CommonAppData%\[RANDOM NUMBERS AND CHARACTERS] | |
| 3. | %LocalAppData%\[RANDOM 3 CHARACTERS].exe | |
| 4. | %LocalAppData%\[RANDOM NUMBERS AND CHARACTERS] | |
| 5. | %Temp%\[RANDOM NUMBERS AND CHARACTERS] | |
| 6. | %UserProfile%\Templates\[RANDOM NUMBERS AND CHARACTERS] |
Registry Details
URLs
Vista Antivirus Pro 2013 may call the following URLs:
| onlinestreamsearch.com |

