QRYPT Ransomware
QRYPT is threatening ransomware designed to encrypt victims' files, making them unreachable until a ransom is paid. This ransomware variant is known for its advanced encryption techniques and stealthy propagation methods. Indeed, this harmful software is specifically created to encrypt files and then modify their filenames by adding a unique extension - '.qrypt.' Additionally, it also delivers a ransom note entitled 'Readme How to Recover.txt.' To illustrate how QRYPT carries out its file renaming process, it alters files, such as '1.jpg' into '1.jpg.qrypt' and '2.png' into '2.png.qrypt.' This pattern continues for every affected file.
Table of Contents
The QRYPT Ransomware Locks Data on Infected Devices
The ransom note of the QRYPT Ransomware says that the victim's data has been encrypted and can only be decrypted with the attackers' help. To restore files, the victim is instructed to obtain a decryption tool from the attackers. The note also warns that ignoring it will result in the attackers publishing the victim's data on the Dark Web.
Additionally, the ransom note explains that in order to contact the attackers, the victim must download the TOR browser and access their website using the provided ID and password. The note warns against modifying or recovering files independently, as this could make them unrecoverable.
How to Proceed Following a Ransomware Attack?
In today's digital landscape, it is crucial for victims of ransomware attacks to understand the dire consequences of succumbing to the demands of threat actors. While it may seem like paying the ransom is the easiest solution, one must know that there is nothing that can guarantee that the attackers will actually provide a decryption tool. Moreover, this course of action may lead to significant monetary and data loss, exacerbating the already distressing situation.
It is useful to acknowledge that decrypting the files encrypted by ransomware is an exceedingly complex task, one that is rarely achievable without the direct involvement of the attackers themselves. This means that victims are essentially powerless in their quest to regain access to their valuable data, and paying the ransom becomes an even riskier proposition.
Given these staggering odds, it is imperative for victims to focus their efforts on eliminating ransomware from their compromised systems. By doing so, they can not only prevent future encryptions but also safeguard other computers connected to their local network from falling prey to similar attacks.
Ultimately, the decision not to pay the ransom is one that prioritizes long-term security and integrity over short-term convenience. Victims must remain vigilant, seek professional assistance and explore alternative avenues for data recovery. By staying enlightened and taking proactive measures, individuals and organizations can strengthen their resilience against the ever-looming threat of ransomware attacks.
Protecting Your Devices from Ransomware Threats
To defend devices and data from ransomware attacks, users should adopt a comprehensive security strategy:
- Regular Backups: Safeguard your data by regularly backing it up to an autonomous hard drive or cloud storage. Ensure that you keep your backups up-to-date.
- Offline Backups: To protect your data even if your system gets infected by ransomware, it is crucial to maintain at least one offline backup copy.
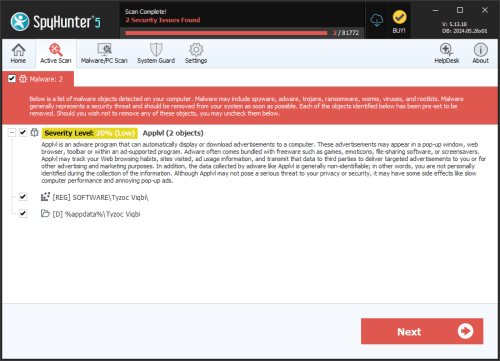
- Use Security Software: Protect your devices by installing reputable antivirus and anti-malware software. Keep these tools updated and run regular system scans.
- Firewalls: Enable and configure a firewall to prevent unauthorized access to your network and devices.
- Keep Software Updated: Patch vulnerabilities that ransomware can exploit by regularly updating your operating system. Ensure that all applications, including web browsers and plugins, are also kept up-to-date with the latest security patches.
- Implement Email Security: Reduce the risk of ransomware by using robust spam filters that can detect and block phishing emails. Use caution when dealing with email attachments and links, especially if they are sent from unknown or suspicious sources.
- Practice Safe Browsing: Only visit dedicated websites and do not click on pop-up advertisements or download files from untrusted sites. Use ad blockers to minimize the risk of malicious advertisements that can lead to ransomware infections.
- Limit User Privileges: Adhere to the least privilege principle by assigning users the minimum necessary permissions for their tasks. Avoid using accounts with administrative privileges for everyday activities. Enable User Account Control (UAC) to prevent unauthorized changes to your system.
- Educate Yourself and Your Team: Enhance awareness of ransomware risks and the importance of cybersecurity best practices among yourself and your team. Elaborate and communicate an incident response plan in case of a ransomware attack.
- Disable Remote Desktop Protocol (RDP): If not required, disable RDP. If necessary, secure it with strong passwords, two-factor authentication, and limit the IP addresses that can access it.
- Monitor Network and System Activity: Regularly monitor system logs and alerts for any suspicious activity that may indicate a ransomware attack. Implement invasion detection and prevention systems to identify and stop potential threats.
By implementing these measures, users are likely to significantly diminish the risk of being victim to ransomware infections and ensure the safety of your devices and data.
The full ransom note generated by the QRYPT Ransomware is:
'[ Hello, Victim's Name ]
BY QRYPT\n"www.gram,ggragrgra
What happened?
Your data has been encrypted. We used robust encryption algorithms, making it impossible to decrypt your data without our help.
However, you can restore everything by acquiring a decoder program from us. This program will restore all your encrypted data.
Follow our instructions below, and you will retrieve all your data.
If you continue to ignore this message, we will report the hack to the mainstream media and publish your data on the dark web.What guarantees?
We value our reputation. If we fail to fulfill our obligations, no one will pay us, and this is not in our interest.
Our decryption software is thoroughly tested, and we guarantee that it will decrypt your data. We will also provide guidance on how to use it.
We guarantee to decrypt up to 03 files for free. Visit our website and contact us.What information was compromised?
We have copied over 50 GB from your network. Here are some proofs, for additional confirmations.
If you ignore us, the information will be disclosed to the public.
ProofsHow to contact us?
Download the TOR browser (TOR).
Access our website (QRYPT).
RoomID: -
Password: -
!!! DANGER !!!
DO NOT MODIFY or attempt to RECOVER any files on your own. If you corrupt any file, the decryption software WILL NOT be able to RESTORE THEM.
!!! DANGER !!!'