Internet Security 2014
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 35 |
| First Seen: | May 28, 2013 |
| Last Seen: | November 26, 2022 |
| OS(es) Affected: | Windows |
Internet Security 2014 is one of the many fake security programs that exist to scam inexperienced computer users. Like its predecessors from the FakeRean family, Internet Security 2014 is part of a convoluted scam that is used to attempt to steal your money. If a supposed security program named Internet Security 2014 is installed on your computer, beware! ESG security analysts strongly advise that you ignore all messages and 'warnings' issued by Internet Security 2014 and instead use a genuine anti-malware tool to erase this infection from your computer.
The Internet Security 2014 rogue security application is designed to trick PC users and make them purchase a 'full version' of this fake security program. There are many ways in which Internet Security 2014 forces computer users to do this, the most common of which is convincing the victim that their computer is severely infected. Internet Security 2014 pretends to be a real security program, running a fake scan of the victim's computer and using an interface that is highly authentic looking. However, regardless of the actual state of the infected computer, Internet Security 2014 will claim to have found dozens of viruses, Trojans, worms and other problems. Internet Security 2014 uses alarming messages and system alerts to trick the computer user into believing this lie. Internet Security 2014 will also cause infection symptoms deliberately, such as preventing the victim from accessing security software, files or browsing the Internet normally. However, as you will see, trying to use Internet Security 2014 to fix these supposed problems is useless.
Table of Contents
How Internet Security 2014 Steals Your Money
Whenever the affected computer user attempts to use Internet Security 2014 to fix these supposed problems, this fake security program will claim that Internet Security 2014 needs to be updated. Of course, this supposed update is not free and will generally cost the victim quite a bit of money. Even worse, purchasing a fake 'update' for Internet Security 2014 allows the criminals responsible for Internet Security 2014 to gain access to your credit card information since it can be used to get hold of your money or identity.
Other fake security programs that belong to the FakeRean family, clones of Internet Security 2014 are Antivirus 2008, Windows Antivirus 2008, Vista Antivirus 2008, Antivirus Pro 2009, AntiSpy Safeguard, ThinkPoint, Spyware Protection 2010, Internet Antivirus 2011, Palladium Pro, XP Anti-Virus 2011, CleanThis, PC Clean Pro, XP Home Security 2012, Windows Clear Problems, XP Security 2012, Antivirus PRO 2015.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Kaspersky | UDS:DangerousObject.Multi.Generic |
| McAfee | Artemis!6635981975FC |
| Panda | Suspicious file |
| AVG | Agent |
| Fortinet | W32/Kryptik.Y!tr |
| AhnLab-V3 | Trojan/Win32.FakeAV |
| McAfee-GW-Edition | Heuristic.LooksLike.Win32.SuspiciousPE.F!83 |
| AntiVir | TR/Crypt.ZPACK.Gen2 |
| BitDefender | Gen:Variant.Kazy.178480 |
| McAfee | ZeroAccess-FCDE!27B5F2A62882 |
| Panda | Trj/Genetic.gen |
| Fortinet | W32/Kryptik.BCAD |
| Ikarus | Trojan.Win32.FakeAV |
| AhnLab-V3 | Trojan/Win32.Agent |
| Microsoft | Rogue:Win32/FakeRean |
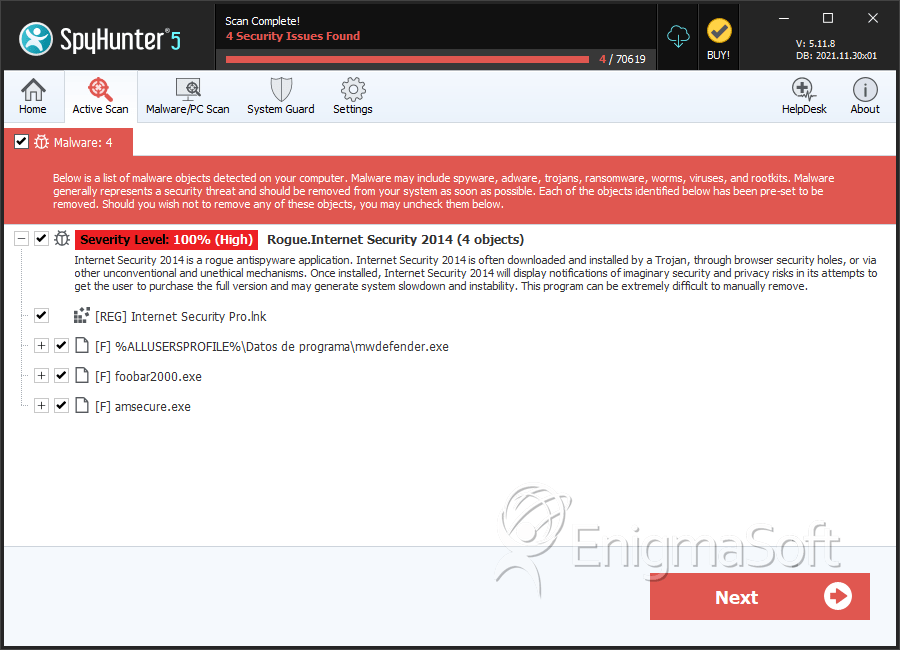
SpyHunter Detects & Remove Internet Security 2014
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | mwdefender.exe | d76a89ff3f1d3c7e7f76a7f361040422 | 1 |
| 2. | mwdefender.exe | 5fb755eed77a7554a729375881674ccd | 1 |
| 3. | mwdefender.exe | 6635981975fc0448dcee267b7826a931 | 1 |
| 4. | %AppData%\Insecure.exe | ||
| 5. | %Desktop%\Internet Security 2014.lnk | ||
| 6. | foobar2000.exe | d4cd609a6fcca97fd62caf78da658286 | 0 |
| 7. | amsecure.exe | 27b5f2a6288219a37e8d5b7eb3bafcf1 | 0 |

