Windows Defence Master
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 7 |
| First Seen: | March 15, 2014 |
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
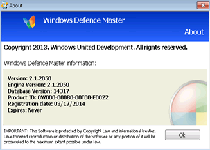
 Windows Defence Master is a rogue anti-malware program that is a new addition to the FakeVimes family of threats. Threats in the FakeVimes family are often disguised as legitimate security programs to trick inexperienced computer users into handing over their money. Windows Defence Master is no exception. Windows Defence Master uses an interface and approach that is similar to hundreds of variants in the FakeVimes family of threats. Like its many clones, the main purpose of Windows Defence Master is to profit at the expense of computer users by making them think that their computers have been compromised. Windows Defence Master will claim to have found numerous threats and then try to prove to unskilled PC users that they need to pay for a 'full version' of Windows Defence Master. Malware specialists vehemently advise computer users to disregard Windows Defence Master's warnings and instead delete Windows Defence Master with the collaboration of a real security program that is fully up to date.
Windows Defence Master is a rogue anti-malware program that is a new addition to the FakeVimes family of threats. Threats in the FakeVimes family are often disguised as legitimate security programs to trick inexperienced computer users into handing over their money. Windows Defence Master is no exception. Windows Defence Master uses an interface and approach that is similar to hundreds of variants in the FakeVimes family of threats. Like its many clones, the main purpose of Windows Defence Master is to profit at the expense of computer users by making them think that their computers have been compromised. Windows Defence Master will claim to have found numerous threats and then try to prove to unskilled PC users that they need to pay for a 'full version' of Windows Defence Master. Malware specialists vehemently advise computer users to disregard Windows Defence Master's warnings and instead delete Windows Defence Master with the collaboration of a real security program that is fully up to date.
Table of Contents
How Windows Defence Master Misleading Tactic Works
Windows Defence Master and its many clones usually follow the same approach when attacking a computer. The following are usually the steps that may be used by Windows Defence Master and its clones to attempt to steal your money:
- Windows Defence Master is installed automatically. Typically, Windows Defence Master is installed using threat delivery methods such as attack websites, spam email messages and social engineering tactics.
- Once installed, Windows Defence Master makes changes to the affected Web browser's settings. These changes allow Windows Defence Master to interfere with other software, cause the affected computer to display error messages and cause performance issues on the affected computer.
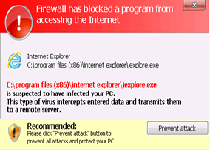
- Windows Defence Master spams the victim with bogus error messages and fake virus scan reports. All of these are meant to make computer users believe that Windows Defence Master has found numerous threat on the infected computer.
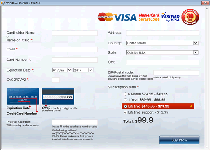
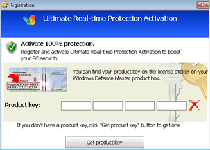
- If computer users try to use Windows Defence Master to fix these supposed threat problems, Windows Defence Master will display additional error messages claiming that it is necessary to spend money buying a unproductive 'full version' of Windows Defence Master.
The FakeVimes is a huge family of threats that have, among its many clones Virus Melt, Presto TuneUp, Fast Antivirus 2009, Extra Antivirus, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, PC Live Guard, Live PC Care, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security, Windows Protection Suite, Windows Work Catalyst.

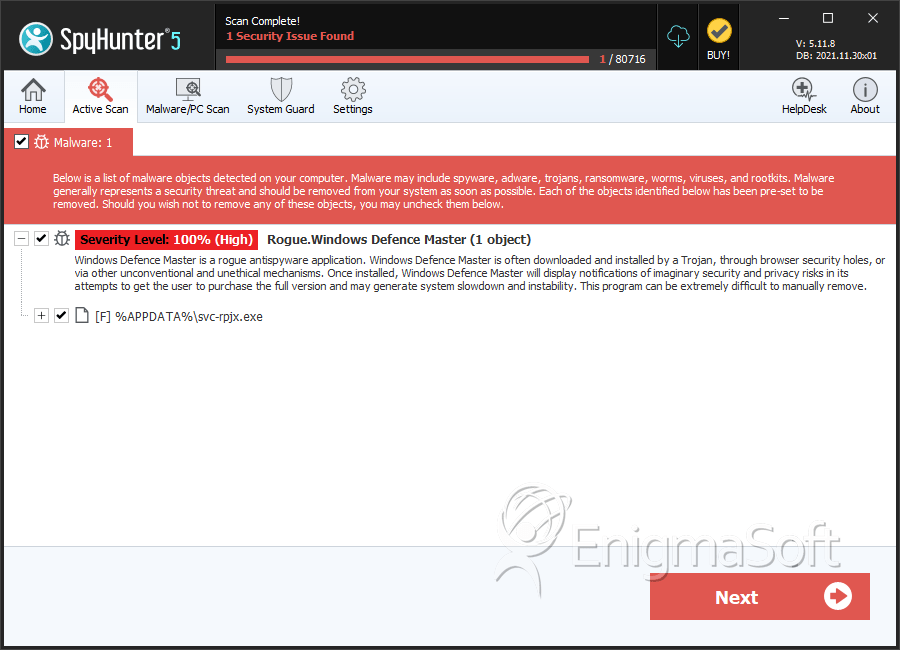
SpyHunter Detects & Remove Windows Defence Master
Windows Defence Master Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | svc-rpjx.exe | 18f5ab40c8d56cb4b0551c26a6c17ae9 | 2 |
| 2. | %AllUsersProfile%\Start Menu\Programs\Windows Defence Master.lnk | ||
| 3. | %AppData%\svc-[RANDOM].exe | ||
| 4. | %AppData%\data.sec | ||
| 5. | %UserProfile%\Desktop\Windows Defence Master.lnk |

