Windows Antivirus Care
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 6,791 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 2,656 |
| First Seen: | April 19, 2012 |
| Last Seen: | September 18, 2023 |
| OS(es) Affected: | Windows |
The FakeVimes family of rogue anti-virus programs is composed of dozens of dangerous scamware programs that pretend to be legitimate anti-virus applications; Windows Antivirus Care is one of these fake anti-virus programs. The main way in which Windows Antivirus Care tries to scam its victims is by making them believe that their computer is under attack. To accomplish this, Windows Antivirus Care is designed to attack the victim with a continuous stream of alarming error messages. Windows Antivirus Care also uses a GUI that is very similar to the one used by real security programs. Once a victim has fallen for the scam, Windows Antivirus Care will attempt to convince them to upgrade to the "full version" of Windows Antivirus Care in order to stop the imaginary virus attack. However, it is important to remind computer users that, despite its appearance, Windows Antivirus Care is a malware infection itself.
Apart from its scam, Windows Antivirus Care can cause many other problems on the infected computer system. Some typical symptoms of a Windows Antivirus Care include frequent system crashes, decreased system performance, browser redirects, and problems accessing files on the infected computer. These, coupled with Windows Antivirus Care's annoying error messages and fake system scans, can quickly make a computer system practically unusable. Because of this, Windows Antivirus Care is not a simple annoyance but a severe security threat that should be eliminated with a reliable anti-malware program.
Table of Contents
A General Overview of the Windows Antivirus Care Rogue Anti-Virus Program
It is important to note that Windows Antivirus Care is not connected in any way to Windows or to Microsoft, despite the fact that Windows Antivirus Care uses trademarked logos in its GUI as well as an interface that borrows heavily from legitimate Windows security components. Windows Antivirus Care's family of malware is quite large and has been active since 2009. Windows Antivirus Care belongs to a particular batch of FakeVimes rogue anti-virus programs that have been active since January of 2012. Some other fake anti-virus applications belonging to this same batch of malware include such fake security programs as Virus Melt, Presto TuneUp, Fast Antivirus 2009, Extra Antivirus, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, PC Live Guard, Live PC Care, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security, Windows Protection Suite, Windows Work Catalyst.
Windows Antivirus Care asks for a registration code in order to supposedly upgrade to its "full version". ESG malware analysts have provided the registration code 0W000-000B0-00T00-E0020 as a possible way of stopping Windows Antivirus Care's most annoying evidences. However, it is crucial to note that this registration code will not remove Windows Antivirus Care or clean your system; it will merely stop Windows Antivirus Care from displaying error messages and browser redirects. Windows Antivirus Care should still be removed with a reliable security tool.
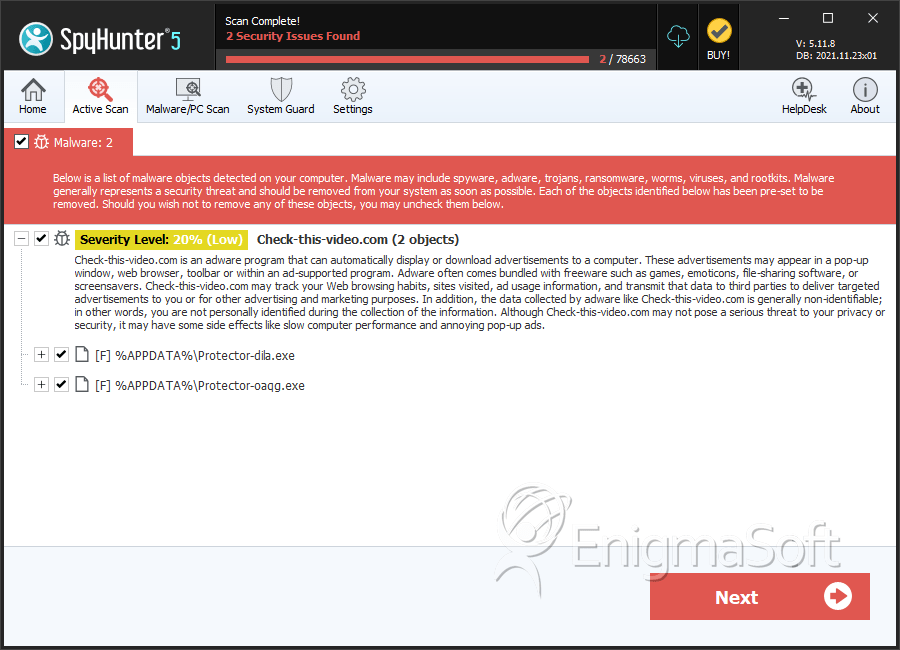
SpyHunter Detects & Remove Windows Antivirus Care
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Protector-dila.exe | 312aad289605205c7cbb6a46393b2f40 | 1 |
| 2. | Protector-oaqg.exe | cf8bad01080ea7d2d6839e8837ac6845 | 1 |
| 3. | %AppData%\Protector-[RANDOM CHARACTERS].exe | ||
| 4. | %AppData%\Inspector-[RANDOM CHARACTERS].exe |
Registry Details
URLs
Windows Antivirus Care may call the following URLs:
| check-this-video.com |

