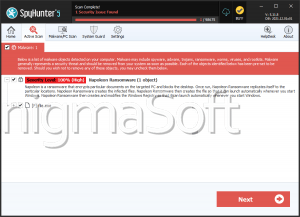
Leon Ransomware
The Leon Ransomware is an encryption ransomware Trojan that belongs to a family of ransomware that also includes the Blind and the Skeleton Ransomware. The Leon Ransomware was first observed on January 4th, 2017, and seems to have been under development since late 2017 along with other ransomware in its family. The Leon Ransomware, like other, similar threats, is typically distributed using spam email campaigns. The victims will get a spam email message that uses social engineering to try to induce the victim into opening an attached file. The messages are often disguised to appear as emails from legitimate sources, such as Amazon, Facebook, FedEx or numerous others. When the corrupted file is opened, a macro script downloads and installs the Leon Ransomware onto the victim's computer.
The Common Attack Executed by the Leon Ransomware
Once the Leon Ransomware is installed on the victim's computer, the Leon Ransomware will disable several Windows safety features such as the System Recover and the Shadow Volume Copies, and then will use the AES 256 encryption to make the victim's files inaccessible. The Leon Ransomware will target the user-generated files, which may include files with the following file extensions:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks,.jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The Leon Ransomware will mark the files encrypted in the Leon Ransomware attack by adding the file extension '.[atilla666@tutanota.com].leon,' which includes the email address that is used to contact the people associated with the Leon Ransomware. PC security researchers also have uncovered a variant of the Leon Ransomware that marks affected files with the file extension '.[kill@rape.lol].kill,' added to each encrypted file.
The Leon Ransomware's Ransom Demand
The Leon Ransomware will deliver its ransom note in the form of an HTA file dropped on the victim's computer after compromising the victim's files. The file, named 'How_Decrypt_Files.hta,' contains the following ransom note message:
'All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail atila666@tutanota.com You have to pay for decryption in Bitcoins. The pace depends on how fast you write to us. After payment, we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee Before paying you can send us up to 3 files for free decryption. The total size of files must be less than 1Mb (non archived), and lies should not contain valuable information. (databases,backups, large excel sheets, etc.)
Flow to obtain Sitcoins The easiest way to buy btcoins 5 LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price. hxxps://localbrtcoins.corn/buy_btcoins Also you can find other places to buy Btcoins and beginners guide here: hxxp://coindesk.com/information/how-can-i-buv-brtcoinsi
Your personal identification number: [RANDOM CHARCTERS]'
This ransom note is delivered in a program window with either the title 'Leon' or the title 'Kill.' The cybercrooks demand a payment that can range from 200 to 600 USD to be paid in Bitcoin. However, computer users shouldn't contact the people responsible for the Leon Ransomware attack or make the Leon Ransomware's ransom payment. Instead, they should ensure that their files are backed up to the cloud or an external memory device. Being able to restore the files encrypted by the Leon Ransomware attack is the best way to guarantee that there will never be any need to negotiate or even contact the people responsible for the Leon Ransomware attack.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.