Elite Enterprise Ransomware
Protecting systems against modern malware is no longer optional, it is a fundamental requirement for both individuals and organizations. Ransomware threats continue to evolve in sophistication, targeting not only files but entire infrastructures. One particularly alarming example is Elite Enterprise Ransomware, a threat designed to maximize disruption, fear, and financial pressure on victims.
Table of Contents
A Silent but Devastating Encryption Strategy
Elite Enterprise Ransomware distinguishes itself through a deceptive encryption method. Unlike most ransomware families that append recognizable extensions to locked files, this threat leaves filenames completely unchanged. At a glance, the affected data appears normal, but in reality, it is entirely inaccessible.
The malware employs a hybrid cryptographic model using AES-256 for file encryption and RSA-4096 for key protection. When properly implemented, this combination creates an extremely strong barrier against decryption attempts, effectively preventing victims from restoring files without access to the attackers' private keys.
Psychological Pressure Through Ransom Messaging
Following the encryption phase, the ransomware deploys two ransom notes: an HTML file named 'elite_ransom.html' and a text file titled '!!!ELITE_ENTERPRISE_RANSOMWARE!!!.txt.' These notes are crafted to instill urgency and hopelessness.
The HTML note presents a dramatic overview of the attack, claiming widespread destruction, including the immediate loss of a portion of devices and the elimination of backups. A countdown timer of 168 hours reinforces the pressure, paired with a staggering demand of 227 BTC.
Even more unusual is the complete absence of communication channels. No email addresses, Tor portals, or negotiation mechanisms are provided. Victims are instructed to transfer the full ransom amount to a specified wallet, with a claim that decryption will occur automatically, an assertion that raises serious doubts about credibility.
Claimed Capabilities and System-Level Damage
The text-based ransom note expands on the technical scope of the attack, portraying a highly coordinated and destructive campaign. It describes a five-day silent propagation phase during which the malware allegedly spread across the network undetected.
According to the note, the attack includes:
- Disabling MSP and administrative management tools
- Deleting cloud-based resources
- Corrupting network infrastructure components
- Infecting MBR and VBR boot sectors
- Deleting Volume Shadow Copies to prevent restoration
- Introducing intermittent file corruption for additional damage
While some claims may be exaggerated for psychological impact, the described techniques align with tactics used in advanced, enterprise-targeting ransomware operations.
Why Paying the Ransom Is a Risky Gamble
Despite the severe consequences outlined in the ransom notes, paying the demanded 227 BTC offers no guarantee of recovery. Cybercriminal groups often fail to deliver functional decryption tools, and in this case, the absence of communication channels eliminates any possibility of support or verification.
Additionally, the supposed 'automatic decryption' mechanism lacks transparency and reliability. Without interaction or validation, victims have no assurance that payment will trigger any recovery process. Funding such operations also contributes to these types of cybercrime campaigns.
Infection Vectors and Target Profile
Elite Enterprise appears to be tailored primarily for corporate environments. Its described capabilities, such as network-wide propagation and infrastructure disruption, suggest a focus on high-value targets.
Common infection methods associated with ransomware of this class include:
- Phishing emails carrying malicious attachments or links
- Compromised Remote Desktop Protocol (RDP) access
- Trojanized software downloads or pirated applications
- Malicious advertisements and drive-by downloads
- Fake software update prompts and exploit kits
These vectors highlight the importance of both user awareness and technical safeguards in preventing initial compromise.
Strengthening Defenses Against Advanced Ransomware
Defending against threats like Elite Enterprise requires a multi-layered approach that combines technical controls with user discipline. Organizations and individuals should prioritize resilience, detection, and recovery readiness.
Key security practices include:
- Maintaining regular, offline backups stored on disconnected or remote systems
- Implementing strong access controls, including multi-factor authentication
- Keeping operating systems and software fully updated with security patches
- Disabling unnecessary services such as exposed RDP ports
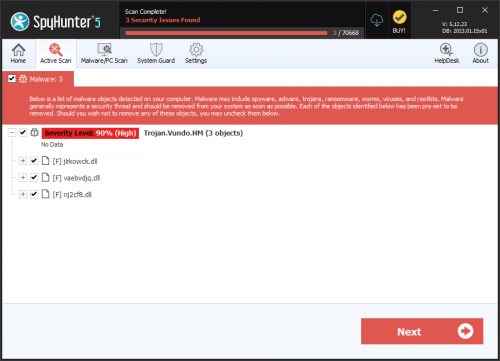
- Using reputable endpoint protection and intrusion detection systems
- Training users to recognize phishing attempts and suspicious content
- Restricting the use of macros and executable attachments from untrusted sources
Beyond these measures, continuous monitoring and incident response planning are critical. Early detection can significantly reduce the scale of damage in the event of an intrusion.
Final Assessment
Elite Enterprise Ransomware represents a highly aggressive and psychologically manipulative threat, combining strong encryption with tactics aimed at overwhelming victims. Its lack of communication channels and extreme ransom demand further differentiate it from conventional ransomware campaigns.
The most reliable recovery strategy remains prevention and preparedness. Once encryption is complete, options become severely limited. A strong security posture, combined with resilient backup strategies, is the only dependable defense against such advanced attacks.