Windows Expert Console
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 1 |
| First Seen: | November 25, 2013 |
| OS(es) Affected: | Windows |
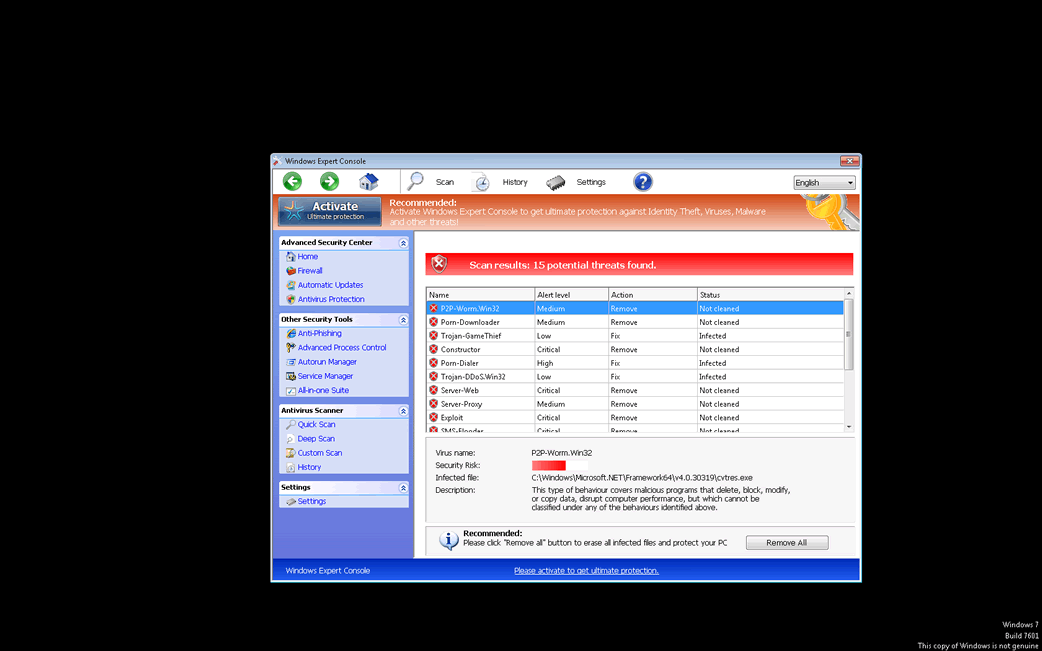
Windows Expert Console Image
Windows Expert Console is a rogue security application. Windows Expert Console belongs to an enormous family or rogue security programs, the FakeVimes family. Threats in Windows Expert Console's family use very similar naming patterns that seem to be generated automatically using a thesaurus, often to the point of not making sense. Regardless of the name of the particular variant of Windows Expert Console infecting a computer, all of these fake security applications carry out the same basic scam. Because of this, Windows Expert Console or its variants should be removed at once from an infected computer.
Table of Contents
Windows Expert Console Scam’s Expertise is to Steal Money from Credible PC Users
Rogue security applications like Windows Expert Console have been active for at least nearly a decade, in one way or another. Although their tactics for evading detection and removal have become increasingly advanced, the same basic strategy behind infections like Windows Expert Console remains the same. Typically, programs like Windows Expert Console enter a computer often using typical threat delivery methods such as attack websites and social engineering tactics or through the use of secondary Trojan or rootkit infections designed to download and install threats on the victim's computer. Once Windows Expert Console has been installed, Windows Expert Console effectively takes over the affected computer. Windows Expert Console pretends to be a real security application, claiming that the victim's computer is infected with various Trojans, viruses or worms. When the computer user tries to use Windows Expert Console to remove these bogus threats, Windows Expert Console displays a message claiming that it is necessary to pay for an expensive, fake 'full version' of Windows Expert Console.
Deleting Windows Expert Console for Good
Malware researchers strongly advise computer users to avoid paying for this fake upgrade. Instead, Windows Expert Console should be removed with the help of an actual security program. Starting up the affected computer in Safe Mode can prevent Windows Expert Console from defending itself by interfering with your anti-virus software. Windows Expert Console's clones use names such as Virus Melt, Presto TuneUp, Fast Antivirus 2009, Extra Antivirus, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, PC Live Guard, Live PC Care, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security, Windows Protection Suite, Windows Work Catalyst.
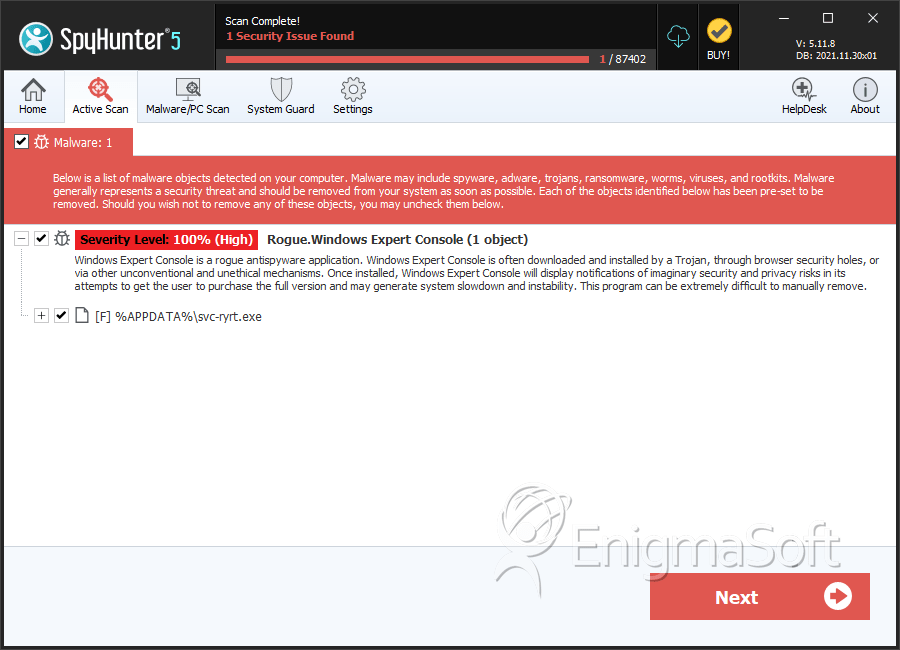
SpyHunter Detects & Remove Windows Expert Console
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | svc-ryrt.exe | 0e8e56ab76b42e2527caa10cba692d55 | 1 |
| 2. | %AppData%\guard-fvtb.exe | ||
| 3. | %AppData%\results1.db |

