Windows Activity Debugger
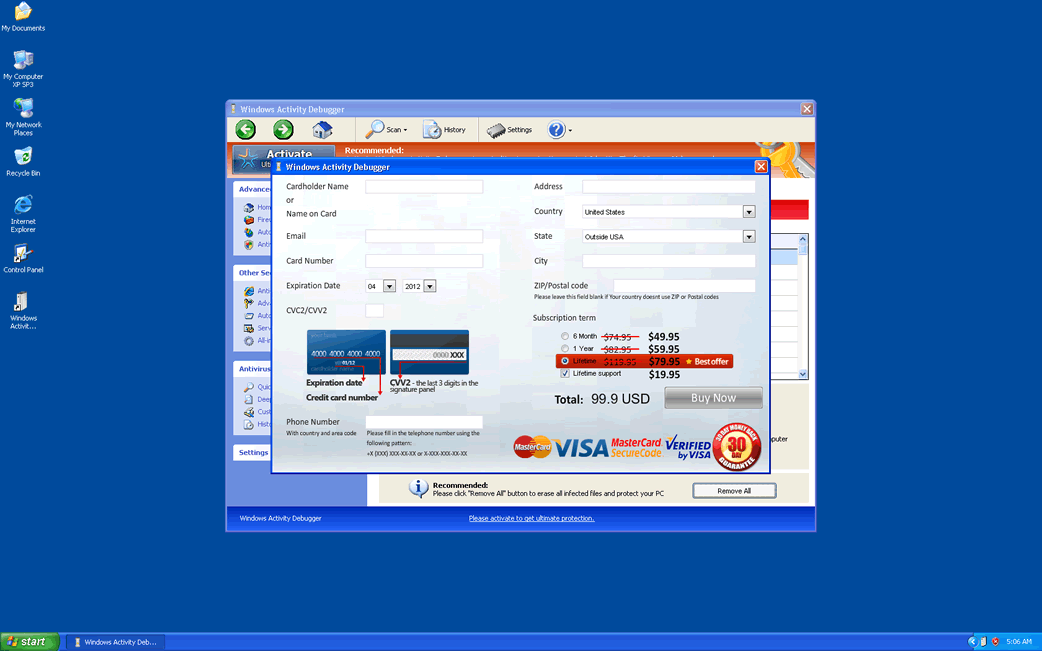
Windows Activity Debugger Image
Windows Activity Debugger has no way to debug your computer system! ESG security analysts have issued a warning regarding the fake security program Windows Activity Debugger, which is part of a recent batch of rogue security programs in the FakeVimes family of malware. Applications like Windows Activity Debugger are often installed on the victim's computer through a Trojan infection. Once installed, they are designed to imitate a security program. However, Windows Activity Debugger and its clones have no way of fixing your computer; they are mainly designed to create non-stop error messages, so inexperienced computer users will panic.
There are dozens of fake security programs in the FakeVimes family of malware, which has been around since 2009. Some examples of clones of Windows Activity Debugger include Virus Melt, Presto TuneUp, Fast Antivirus 2009, Extra Antivirus, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, PC Live Guard, Live PC Care, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security, Windows Protection Suite, Windows Work Catalyst.
Regardless of their name, all of these programs are essentially the same malicious application, with a different title slapped onto very similar user interfaces. While the FakeVimes rogue security programs are very similar to rogue security programs in other families of rogue security software, they are often distinguished by their unique user interface, a loading screen with a large Microsoft Security Center logo and file names that include a characteristic string made up of three random letters. In the batch of FakeVimes clones that include Windows Activity Debugger, these file names are usually preceded with the string 'protector-' (this is the case of Windows Activity Debugger) or 'inspector-'.
Table of Contents
Removing Windows Activity Debugger from Your Computer System
Fortunately, PC security analysts have had plenty of time to get acquainted with Windows Activity Debugger and its clones, since the FakeVimes family of malware has been around for several years. This means that most legitimate security programs have no problem detecting and stopping a Windows Activity Debugger infection in its tracks. However, criminals have bypassed these by including a rootkit component in their latest batch of Windows Activity Debugger clones which disables security software and makes Windows Activity Debugger undetectable. This rootkit component is usually a version of the ZeroAccess rootkit. To remove this threat, ESG malware analysts first recommend using a reliable anti-rootkit utility or an advanced anti-malware program with the capacity to deal with rootkit infections. Whatever you do, do not pay for a 'full version' of Windows Activity Debugger, even if you only do it to stop its annoying messages. 'Registering' Windows Activity Debugger will not remove the malware infection from your computer; it only stop its pop-up windows momentarily.













Windows Activity Debugger Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%Protector-[RANDOM 3 CHARACTERS].exe.exe | |
| 2. | %AppData%NPSWF32.dll | |
| 3. | %Desktop%Windows Activity Debugger.lnk | |
| 4. | %StartMenu%ProgramsWindows Activity Debugger.lnk | |
| 5. | %AppData%\result.db |

