Dridex
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 13 |
| First Seen: | October 29, 2014 |
| Last Seen: | November 24, 2021 |
| OS(es) Affected: | Windows |
 The developers of the Trojan Cridex, also detected as Geodo, Feodo and Bugat, have released another version of this dreadful data collector Trojan called Dridex. Dridex main duty is to collect bank security data by adding automated scripts containing recurrent assignments into the Microsoft Office Package. Dridex started its infection campaign using Microsoft Word to dispatch messages allegedly, including financial documentation. Then, when the computer user opens the corrupted document, the added scripts may start executing their assignments and install Dridex.
The developers of the Trojan Cridex, also detected as Geodo, Feodo and Bugat, have released another version of this dreadful data collector Trojan called Dridex. Dridex main duty is to collect bank security data by adding automated scripts containing recurrent assignments into the Microsoft Office Package. Dridex started its infection campaign using Microsoft Word to dispatch messages allegedly, including financial documentation. Then, when the computer user opens the corrupted document, the added scripts may start executing their assignments and install Dridex.
By collecting your online banking-related data and sending it to remote servers, Dridex makes it possible for its creators to access your banking account and transfer the available money to their personal accounts. As any Trojan infection, Dridex is a highly harmful infection that must be removed upon detection. Manual removal is possible, however, due to its complexity, the safest removal method is using an up-to-date and reliable malware removal application.
Dridex, in its trojan horse form, dates back to 2015 but has had subsequent variations spotted beforehand. However, 2015 marks the year that Dridex made its biggest outbreak accounting for multiple campaigns targeting computer users throughout Europe. Dridex has been marked as most prevalent in the UK, Germany, France, and of course, the United States of America.
Table of Contents
Dridex’s complexities make it one of the most dangerous modern computer threats
Many newer versions of Dridex have appeared spreading various computer viruses. With its mass spread of malware threats, Dridex has earned itself a ranking of being one of the top 10 most popular threats of its type coming in at number seven in recent years, according to Flashpoint.
The many actions of Dridex range from it collecting personal data to injecting sites with malware. The primary objective of Dridex has been rather consistent residing with its ability to steal data, which is usually banking or login data where the hackers behind Dridex may leverage such information to eventually lead to theft of money or even cryptocurrency wallets.
There has been an ongoing change of hands of Dridex where it is actively sold to other cybercrooks who then utilize the malware to collect personal information of new victims. The action of Dridex injecting websites with malware eventually leads to actions that phish user logins and passwords.
Dridex has also been known to use a Botnet as a Service feature that makes infected PCs an attack source for future campaigns, essentially allowing the malware to spread faster and more efficiently. Such a notion has made threats like Dridex global sensations that have no geographic boundaries.
Who is behind Dridex?
The perpetrators behind Dridex, or what is referred to as "Evil Corp", the cybergang that created Dridex, come out of Russia where they have been seen living a rather lavish lifestyle driving supercars and evading law enforcement as a $5 million reward for their capture is being offered by the US Department of State.
The Evil Corp cybergang behind Dridex looks to have made away with millions of dollars in their endeavors of leveraging Dridex in many ways over the past few years. In that time, Dridex has seen ups and downs. Though, in recent months, Dridex has shown that it is not going anywhere, and the crooks behind the vicious malware are ramping up their efforts to make what was old all new again. In the battle against Dridex and similar threats, cybersecurity firms and antimalware researchers are having a difficult time tracing C&C servers associated with Dridex to ultimately bring the threat down. Dridex's advanced persistence mechanisms have kept the malware alive and thriving for many years.
Further uncovering Dridex and its lifecycle
The most recent development in combating Dridex at its source is the malware hunting service ANY.RUN, which has examined the lifecycle of Dridex not only detect the threat but to pinpoint its spreading methods and uncover ways that computer users may avoid future attacks.
The primary methods that Dridex uses to spread, also uncovered by ANY.RUN, is through spam email campaigns. Such a technique, which proves to be among the most effective way to spread malware even in today's landscape, allows cybercrooks to spread Dridex into targeted machines. Many of the spam messages are ones that are cleverly designed to look like financial related emails, most often containing a malicious MS Word document attachment.
Social engineering is commonly used to dupe computer users into opening and downloading the malicious attachments, which when they are run, they install the Dridex trojan.
Detection and removal of Dridex is left to antimalware software and sources like ANY.RUN, which has methods of unpacking the processes of Dridex when it infects a PC so it can then be safely detected and eliminated.
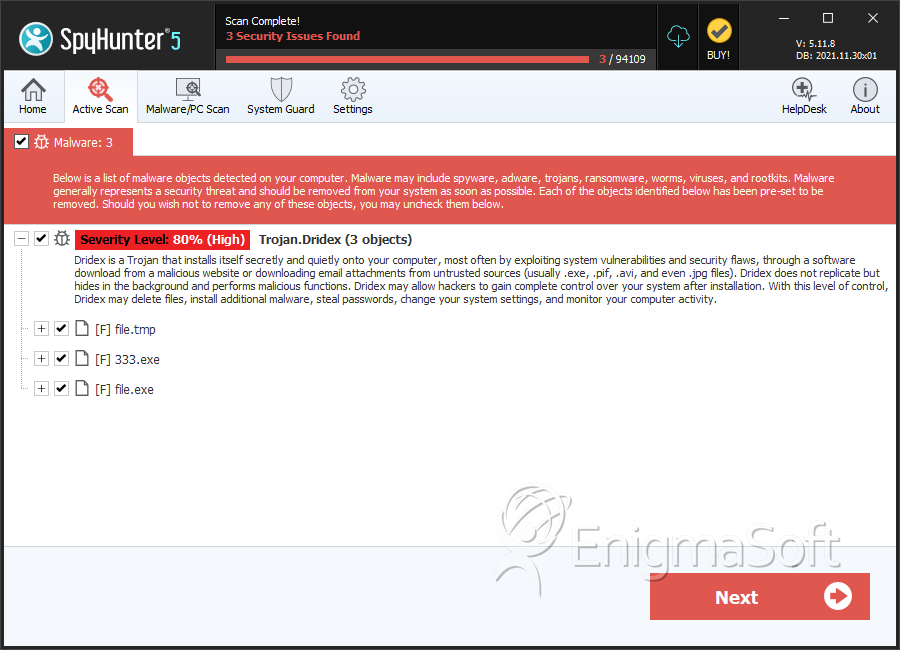
SpyHunter Detects & Remove Dridex
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.tmp | 33d137598c03069197bd47bdaab30774 | 1 |
| 2. | 333.exe | ac1d437e08bfe27942256da9e1ee1293 | 0 |
| 3. | file.exe | f86204bbaf52c0090f8c8ee4cd6a3ce8 | 0 |
| 4. | file.exe | 3fd1d6f9f3d2ea48c55f5db3192d3398 | 0 |
| 5. | file.exe | afcf32eab13b416eb43e5ff2f0367c8c | 0 |
| 6. | file.exe | c386007133c54d70b486ae182bb68eac | 0 |
| 7. | file.exe | aea48ee4aa6f4b44bde2ee2f44dfb95e | 0 |

