CMD Ransomware
CMD Ransomware Image
In these times, it is easy than ever to create data-locking Trojans. Even cyber crooks with little experience can build one if they borrow the code of already existing ransomware threats and only slightly tweak it. And this is what the creators of the newly uncovered CMD Ransomware have done.
Table of Contents
Propagation and Encryption
Upon inspecting the CMD Ransomware, malware researchers concluded that this file-encrypting Trojan is a variant of the popular Dharma Ransomware. The propagation techniques involved in the spreading of the CMD Ransomware are not yet known. Some security experts believe that emails containing macro-laced attachments, fake software updates, and bogus pirated variants of popular applications may be among the infection vectors responsible for the propagation of the CMD Ransomware. When the CMD Ransomware compromises a PC, it will perform a brief scan. The scan located the files, which are of interest to this threat. Usually, cybercriminals that create ransomware threats make sure to target all the popular filetypes so that maximum damage would be ensured. After the completion of the scan, the CMD Ransomware will proceed to the next step of the attack – the encryption process. Once the CMD Ransomware encrypts a file, it will add a new extension at the end of the affected file's filename – '.id-
The Ransom Note
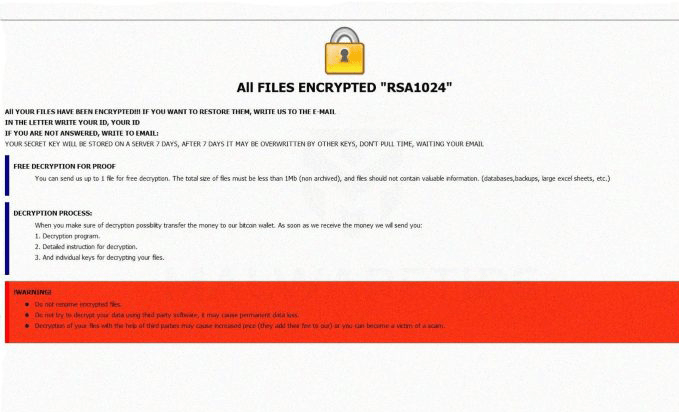
In the next stage of the attack, the CMD Ransomware will drop its ransom note. The name of the note is likely 'info.hta' and/or 'RETURN FILES.txt' and reads:
’All FILES ENCRYPTED "RSA1024"
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL jsmith1974@mail.fr
IN THE LETTER WRITE YOUR ID, YOUR ID
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: jsmith1974@mail.fr
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.’
In the message, the attackers do not specify a sum regarding the ransom fee. However, they demand the user gets in touch with them via email so that they would receive further instructions on how to pay up the sum demanded. The email address provided is 'jsmith1974@mail.fr.' The attackers are willing to unlock one file free of charge, provided that its size does not exceed 1MB. They also warn the user that if they do not get in touch within a week, it is likely that their decryption key will be wiped off permanently.
The CMD Ransomware was observed infecting machines by using Remote Desktop Services (RDP) ports. The attackers were scanning systems running RDP on TCP port 3389 and using brute force techniques to get the passwords to those targeted systems. Updated variants of this ransomware use ".[fox5sec@aol.com].cmd" extension for encrypted files.
The CMD Ransomware uses an RSA-1024 encryption algorithm to block access to affected files. Victims may contact the attackers, and they are given a chance to decrypt one single file with a size of no more than 1MB. That is used as a lure and a sign of goodwill. Users are advised to avoid any interaction with the attackers.
Keep your distance from cyber crooks like the ones responsible for the CMD Ransomware. They will likely take your money gladly and leave you hanging as there is no guarantee they will ever provide you with the decryption key promised. A safer option is to look into obtaining a reputable anti-virus application and use it to remove the CMD Ransomware safely from your PC.