Cerber 4.0 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 9,198 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 71,874 |
| First Seen: | March 4, 2016 |
| Last Seen: | September 11, 2023 |
| OS(es) Affected: | Windows |
The Cerber 4.0 Ransomware represents the next generation in development of the '.cerber' line of encryption Trojans. The Cerber 4.0 Ransomware joins other threats like the ORX-Locker and the Stampado Ransomware, which are offered as Ransomware-as-a-Service package. The RaaS business was pioneered by Encryptor RaaS in early 2015 and the developers of Cerber want a share of the market for ransomware. It appears that the coders behind the Cerber 4.0 Ransomware decided to open their product to foreign programmers and benefit from the expanded distribution network.
Table of Contents
A New JS Loader, New Obfuscation Layers, Customizable Encryption Engine and More
The Cerber 4.0 Ransomware is said to boast several significant improvements compared to the Cerber v3. The Cerber v4 creates a unique file extension marker for every victim, and the Trojan is programmed to bypass all security mechanisms employed by modern AV products. An updated encryption engine is combined with new layers of obfuscation and a JS loader to ensure a hassle-free operation of the Cerber 4.0 Ransomware. The makers of the Cerber v4 offer several strands of their threat for distribution to potential customers. Researchers note that the new Cerber Trojan shifted from a TXT-based ransom note to an HTA format that offers extended functionality and customization. Cyber crooks that wish to deploy their brand of ransomware are welcomed to buy the original Cerber engine and add a personal touch. You can find an example of the new ransom message below:
'CERBER RANSOMWARE
Instructions
Can't you find the necessary files?
Is the content of your files not readable?
It is normal because the files' names and the data in your files have been encrypted by "Cerber Ransomware".
It means your files are NOT damaged! Your files are modified only. This modification is reversible.
From now it is not possible to use your files until they will be decrypted.
The only way to decrypt your files safely is to buy the special decryption software "Cerber Decryptor".
Any attempts to restore your files with the third-party software will be fatal for your files!
You can proceed with purchasing of the decryption software at your personal page:
[links to pages on the TOR Network]
If this page cannot be opened click here to generate a new address to your personal page. '
A Upgraded Distribution Network for the Cerber V4
The Cerber 4.0 Ransomware is deployed to users via spam emails loaded with macro-enabled documents and malvertising. Reports from several AV vendors and Web filtering services reveal that the Cerber 4.0 Ransomware is delivered to users via unsafe advertisements on compromised sites, casino-themed gaming portals, and pages with adult-rated content. In most cases, the RIG Exploit Kit is used to inject the Cerber v4 into vulnerable systems with outdated software and bad port configuration. The RIG EK gained popularity while spreading other threats including the CrypMIC Ransomware and switched to Cerber on October 1st 2016. We should add another exploit kit to the tools used to spread the Cerber 4.0 Ransomware, which is Neutrino. The Neutrino EK became quite popular thanks to a success in deploying the CryptXXX Ransomware.
Computer users can protect their OSes from variants of the Cerber 4.0 Ransomware by creating backups regularly and keeping their software up-to-date. Using an ad-blocker may limit the attack surface for the cyber crooks that utilize malvertising to spread the Cerber v4 as well. However, your first line of defense should be a trusted anti-malware shield that can filter your connection to the Internet and prevent ransomware from loading in Windows.
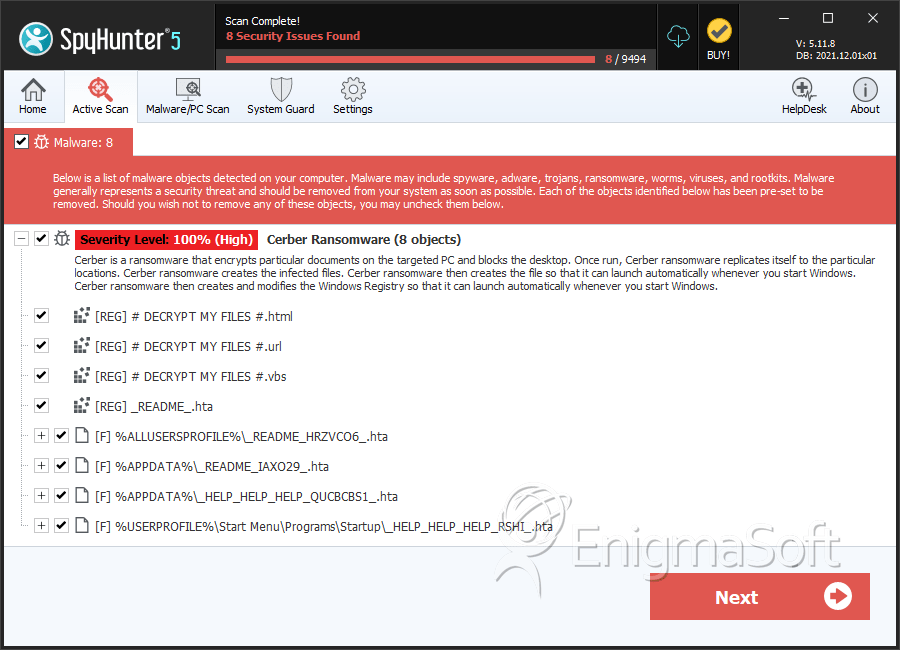
SpyHunter Detects & Remove Cerber 4.0 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Readme.hta | e125ef487472bfdd17d7e3e7e237d0d9 | 167 |
| 2. | Readme.hta | 8f85ab4bb455ce6d413eff9e9d47a506 | 54 |
| 3. | README.hta | 777e13c9a5cad4e1d2134d5104188ff6 | 43 |
| 4. | README.hta | c4fff6005b70cccd895082e6c79595b3 | 36 |
| 5. | README.hta | e189ce9640edc95a1ba19d0d4d85691b | 24 |
| 6. | README.hta | 107ab5eae352dab9defab24d3ba77b4a | 18 |
| 7. | _HELP_HELP_HELP_QUCBCBS1_.hta | c042f1d91619e9b4f91bf1e1b78fee85 | 14 |
| 8. | _HELP_HELP_HELP_RSHI_.hta | a46e5f2ce8a20bbb8548959debb9ac0c | 10 |
| 9. | _HELP_HELP_HELP_STOV8H1_.hta | 1632ca0953d5499bf251455159a80ea0 | 6 |
| 10. | _HELP_HELP_HELP_ND8FZ.hta | 041ef4b6a12e0b3165172884301b0d1e | 5 |
| 11. | _HELP_HELP_HELP_Z49XU_.hta | 243d0fd4f4bee5f11698c20d43b958ff | 4 |
| 12. | _HELP_HELP_HELP_XFCV_.hta | 01ec9e50d17de043a23997d6562293ad | 3 |
| 13. | _HELP_HELP_HELP_2AK4U21_.hta | 55790c64ce1ff75647d5cadcadf3876e | 3 |
| 14. | _HELP_HELP_HELP_3NNARI.hta | 0ef13a9213c456db231825061eec294c | 2 |
| 15. | _HELP_HELP_HELP_L41VV_.hta | c63b4a524713e4c5f3802463cb46dab8 | 2 |
| 16. | _READ_THI$_FILE_L81EB65A_.hta | 2a6828d2ba37bb97efb4773619b80715 | 2 |
| 17. | _HELP_HELP_HELP_2R9I63OS.hta | a2daec078c54bb6bc5e96038a1506f2c | 1 |
| 18. | _HELP_HELP_HELP_UYUR4YE.hta | bc0c75128b9cbc02c8c053c1155fb6d9 | 1 |
| 19. | _HELP_HELP_HELP_CKJ4GL.hta | 99d3fc208d3623107cfb18a9069e23bd | 1 |
| 20. | _HELP_HELP_HELP_SUXEZY_.hta | 5190e890725bf431ba44001e190c70f5 | 1 |
| 21. | _HELP_HELP_HELP_GLP9_.hta | 5f7533c663ddb4c0ae4dbbaafb50d491 | 1 |
| 22. | _HELP_HELP_HELP_HUUKTW_.hta | 0224da72bc3638b351cf509cdfc443c2 | 1 |
| 23. | _READ_THI$_FILE_DB3DT9_.hta | 7476a75b0680d99f5338b886bc7def62 | 1 |
| 24. | wP6fT.exe | 731279e3c09f8e52a849c0a9c1043bb5 | 1 |
| 25. | cmdkey.exe | 27cf39d205567505d840391e4761a7a0 | 1 |
| 26. | file.exe | 212fa73fd6ed39b4720bcfd8d97426d5 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.