Cerber3 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 9,198 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 71,874 |
| First Seen: | March 4, 2016 |
| Last Seen: | September 11, 2023 |
| OS(es) Affected: | Windows |
The Cerber3 Ransomware is a new version of a well-known ransomware Trojan. The Cerber Ransomware Trojan now uses a slightly different method during its attack. The main difference is that the files infected by the Cerber3 Ransomware can be identified through the use of .CERBER3 as the extension that identifies the files that have been encrypted in the attack. PC security analysts had observed a Cerber2 variant of this attack previously. This numbering system may indicate new versions of software, and threats are no exception. The appearance of the Cerber3 Ransomware indicates that the Cerber ransomware family is being developed and updated currently.
Table of Contents
The Cerber3 Ransomware and Possible Updates to this Threat
The Cerber3 Ransomware was discovered recently, around the end of August of 2016. The Cerber3 Ransomware presents minor differences from previous versions of this threat. However, it seems that most of the differences are external and that the threat attack is the same essentially. Since the Cerber3 Ransomware is being improved currently, it is likely that new versions or more differences will be uncovered in the following weeks. The reaction of the con artists responsible for this threat may be because a free decryption utility for this threat was released by PC security analysts this year. It seems that this free decryption utility will not work with the Cerber3 Ransomware variant on this attack.
The Cerber3 Ransomware is the Third Version of the Cerber Ransomware
The Cerber3 Ransomware delivers its ransom note in a file named '# HELP DECRYPT #.txt,' which is drops in directories where the Cerber3 Ransomware has encrypted files. The Cerber3 Ransomware ransom note contains information on how to pay by using BitCoins and the Tor browser, and about the attack. Before you pay the ransom, however, malware researchers advise computer users to consider that it is unlikely that the con artists will provide the means to decrypt the files immediately and, even if they do, the payment will be used to continue developing the Cerber3 Ransomware and other threats. It is highly likely that a new decryption tool will be released to deal with the Cerber3 Ransomware variant since it is still essentially the same attack as the first version of this threat.
How the Cerber3 Ransomware may Enter a Computer
The Cerber3 Ransomware, like most Trojans, enters a computer disguised as something else. Many situations may lead to an infection with Trojans like the Cerber3 Ransomware. The most common method is by opening a corrupted email attachment. The Cerber3 Ransomware also may be distributed through unsafe online advertisements or by distributing it on peer-to-peer file sharing networks. Malware analysts strongly advise that computer users take steps to avoid possibly unsafe websites and precautions when dealing with unsolicited email messages and attachments. The best method to ensure that the Cerber3 Ransomware does not enter your computer is to use a security app that is fully up-to-date and has a good anti-spam filter that will prevent corrupted email messages from entering your email inbox (or at least reduce their frequency greatly).
Dealing with the Cerber3 Ransomware
Unfortunately, the reason why threats like the Cerber3 Ransomware and other ransomware Trojans have become so popular among con artists is that they are very difficult to deal with. Even if the Cerber3 Ransomware is removed with an anti-virus program, the victim's files will still be encrypted and useless until the ransom is paid or an appropriate decryption utility is found (which is not common, since these threats tend to use strong encryption methods in their attacks). Because of this, it is important that computer users have good file backup procedures, and appropriate preventive measures and training are established to lower the risk of a Cerber3 Ransomware infection or other, similar ransomware Trojan attacks.
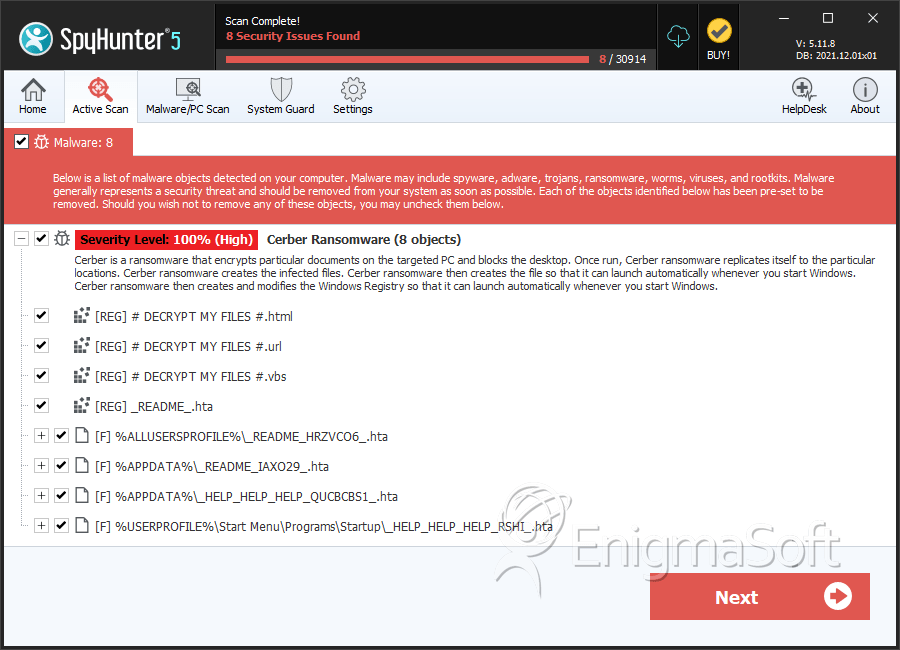
SpyHunter Detects & Remove Cerber3 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Readme.hta | e125ef487472bfdd17d7e3e7e237d0d9 | 167 |
| 2. | Readme.hta | 8f85ab4bb455ce6d413eff9e9d47a506 | 54 |
| 3. | README.hta | 777e13c9a5cad4e1d2134d5104188ff6 | 43 |
| 4. | README.hta | c4fff6005b70cccd895082e6c79595b3 | 36 |
| 5. | README.hta | e189ce9640edc95a1ba19d0d4d85691b | 24 |
| 6. | README.hta | 107ab5eae352dab9defab24d3ba77b4a | 18 |
| 7. | _HELP_HELP_HELP_QUCBCBS1_.hta | c042f1d91619e9b4f91bf1e1b78fee85 | 14 |
| 8. | _HELP_HELP_HELP_RSHI_.hta | a46e5f2ce8a20bbb8548959debb9ac0c | 10 |
| 9. | _HELP_HELP_HELP_STOV8H1_.hta | 1632ca0953d5499bf251455159a80ea0 | 6 |
| 10. | _HELP_HELP_HELP_ND8FZ.hta | 041ef4b6a12e0b3165172884301b0d1e | 5 |
| 11. | _HELP_HELP_HELP_Z49XU_.hta | 243d0fd4f4bee5f11698c20d43b958ff | 4 |
| 12. | _HELP_HELP_HELP_XFCV_.hta | 01ec9e50d17de043a23997d6562293ad | 3 |
| 13. | _HELP_HELP_HELP_2AK4U21_.hta | 55790c64ce1ff75647d5cadcadf3876e | 3 |
| 14. | _HELP_HELP_HELP_3NNARI.hta | 0ef13a9213c456db231825061eec294c | 2 |
| 15. | _HELP_HELP_HELP_L41VV_.hta | c63b4a524713e4c5f3802463cb46dab8 | 2 |
| 16. | _READ_THI$_FILE_L81EB65A_.hta | 2a6828d2ba37bb97efb4773619b80715 | 2 |
| 17. | _HELP_HELP_HELP_2R9I63OS.hta | a2daec078c54bb6bc5e96038a1506f2c | 1 |
| 18. | _HELP_HELP_HELP_UYUR4YE.hta | bc0c75128b9cbc02c8c053c1155fb6d9 | 1 |
| 19. | _HELP_HELP_HELP_CKJ4GL.hta | 99d3fc208d3623107cfb18a9069e23bd | 1 |
| 20. | _HELP_HELP_HELP_SUXEZY_.hta | 5190e890725bf431ba44001e190c70f5 | 1 |
| 21. | _HELP_HELP_HELP_GLP9_.hta | 5f7533c663ddb4c0ae4dbbaafb50d491 | 1 |
| 22. | _HELP_HELP_HELP_HUUKTW_.hta | 0224da72bc3638b351cf509cdfc443c2 | 1 |
| 23. | _READ_THI$_FILE_DB3DT9_.hta | 7476a75b0680d99f5338b886bc7def62 | 1 |
| 24. | wP6fT.exe | 731279e3c09f8e52a849c0a9c1043bb5 | 1 |
| 25. | cmdkey.exe | 27cf39d205567505d840391e4761a7a0 | 1 |
| 26. | file.exe | 212fa73fd6ed39b4720bcfd8d97426d5 | 0 |

