WebIntegration
Potentially Unwanted Programs (PUPs) pose a significant risk to device security and user privacy. These intrusive applications often operate under the guise of being valuable tools but instead engage in activities that compromise user safety. WebIntegration, an application with adware-like characteristics, exemplifies the risks associated with PUPs. Understanding its behavior and distribution tactics is essential for safeguarding your devices.
Table of Contents
WebIntegration’s Intrusive Behavior: How It Impacts Users
Once installed, WebIntegration may initiate a barrage of intrusive advertisements, including pop-ups, banners, in-text links, and full-page advertisements. These advertisements could redirect users to websites promoting dubious software, fake technical support services or phishing schemes. Some advertisements may even lead to fraudulent sites that distribute harmful software.
The risks extend beyond mere inconvenience. Users could encounter tactics such as fake lotteries, deceptive surveys, or fraudulent giveaways that might coax them into sharing private information like login credentials or financial details. These tactics could result in monetary losses, data breaches, or even identity theft.
Furthermore, WebIntegration could collect data about users' browsing activities, including search terms, visited URLs, IP addresses and system specifications. In more invasive cases, the application might access private information such as login details or financial data. This information could be exploited for targeted advertising, purchased by third parties or misused for unsafe purposes.
How WebIntegration Slips through the Cracks: Questionable Distribution Tactics
One of the most concerning aspects of WebIntegration is how it infiltrates devices. PUPs like WebIntegration frequently employ deceptive distribution methods to catch users off guard:
- Bundled Software: WebIntegration may be packaged with free software downloaded from unofficial or unreliable sources. Users who skip through installation processes without carefully reviewing settings, particularly options like "Advanced" or "Custom," risk unknowingly installing additional programs like WebIntegration.
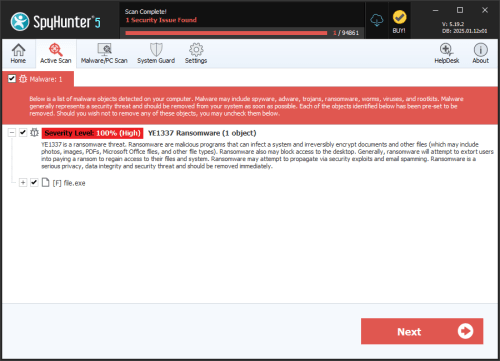
- Deceptive Advertisements: PUPs often use misleading ads or pop-ups to promote their installation. These advertisements may falsely claim that a system update, security scan, or critical software installation is necessary, tricking users into downloading the application.
- Fraudulent Email Campaigns: Links and attachments in phishing emails or direct messages could lead users to download WebIntegration or similar intrusive programs. These messages are often crafted to appear legitimate, increasing the likelihood of user interaction.
- Untrusted Sources: PUPs are frequently distributed through third-party downloaders, unofficial app stores, or P2P (Peer-to-Peer) networks. These sources lack oversight, making them a haven for bundling legitimate software with unwanted programs.
Strengthening Your Defenses: How to Avoid Intrusive Applications
To protect your Mac from intrusive applications like WebIntegration, consider implementing these security practices:
- Be Vigilant During Installations: Always select "Advanced" or "Custom" options when installing software to review and deselect any bundled programs. Avoid downloading software from unverified sources, as these often package legitimate programs with PUPs.
- Scrutinize Online Interactions: Do not click on suspicious ads, pop-ups, or links, especially those offering software updates or system alerts.: Practice caution when interacting with email attachments or links, even if the sender appears trustworthy.
- Keep Your System Updated: Regularly update your operating system and software to patch vulnerabilities that could be exploited by intrusive applications.
- Use Robust Security Measures: Employ reliable security tools to detect and block PUPs and other threats in real-time.: Enable browser extensions that warn against visiting suspicious websites or downloading harmful content.
- Educate Yourself: Familiarize yourself with common PUP distribution tactics and stay informed about emerging threats.
Staying Ahead of Intrusive Applications
WebIntegration serves as a reminder of the privacy and security risks associated with PUPs. By understanding its behavior and recognizing the tactics used to distribute it, users can take proactive steps to protect their devices. Vigilance, coupled with strong security practices, remains the cornerstone of digital safety.