WastedLocker Ransomware
WastedLocker Ransomware Image
Ransomware threats often target unsuspecting users at random, using different propagation tricks. However, this is not the case with the newly uncovered WastedLocker Ransomware. It would appear that the WastedLocker Ransomware only goes after businesses located in the United States. After security experts studied this new file-locker, they found that it is likely created by the cybercriminals that developed and distributed the notorious Dridex banking Trojan. According to researchers, the con-artists in question have also launched campaigns propagating the BitPaymer Ransomware and the Locky Ransomware.
This Week In Malware Ep 13: Evil Corp Hackers Blocked from Deploying WastedLocker Ransomware
Recently, authors of ransomware threats have been using a new trick to further pressure their victims into paying the ransom fee. Many contemporary file-lockers threaten to leak the victim's data online if they do not pay up. This can be a technique particularly useful if the attackers are targeting a company, due to the propensity of business to have sensitive data and confidential documents, which they would not want to be released online. However, the WastedLocker Ransomware creators do not appear to use this technique, which came as a surprise for malware analysts. However, even without using this trick, the WastedLocker Ransomware is fully capable of wreaking havoc on the targeted systems.
Table of Contents
How WastedLocker Targets Computers
The WastedLocker Ransomware appears to be installed on the targeted systems manually. Security researchers believe that this is the case because upon encrypting a file, the WastedLocker Ransomware appends '.wasted' as an extension alongside the name of the victim. It would appear that the authors of the WastedLocker Ransomware have borrowed some of the code from the BitPaymer Ransomware, as both threats seem to have some identical features.
The ransom fee seems to be calculated on an individual basis. However, the attackers usually ask for several million dollars. According to reports, so far, the highest ransom fee set by the WastedLocker Ransomware is approximately $10 million. The WastedLocker Ransomware has a low-infection rate because the propagation of this threat is not automated as the attackers only deploy it against specific targets they pick carefully.
Reports state that there have not been any businesses that have paid the astronomical ransom fees demanded by the WastedLocker Ransomware. Unfortunately, the WastedLocker Ransomware is not decryptable for free.
WastedLocker’s Payload and Methods of Distribution are Unique
WastedLocker is still using the SocGholish fake update framework to distribute the ransomware. The main purpose of the framework is to determine whether the victim’s computer is part of a larger network or not. A JavaScript bot scrapes a lot of system information from the victim, then sends it back to a SocGholish server. Based on this information, the server returns a payload to the victim. This is the chief method of propagation that is still used by Evil Corp.
To protect its payload, WastedLocker uses junk code aiming to increase entropy and obfuscate the real code. The crypter that takes care of this obfuscation first checks the system registry for two specific keys related to Windows script interfaces and if they are not found, it either terminates itself or enters an infinite loop. During the next step, the crypter creates a memory buffer, strings a series of data blobs in that buffer and decrypts the buffer using an XOR algorithm. Once decryption is complete, the buffer is revealed to be shellcode that is in charge of deploying the real payload. The shellcode creates a new buffer and copies the payload in it, decrypts it using another XOR algorithm and finally swaps the crypter code that is already in memory with the payload’s code, then skips to the payload’s entry point.
Before decrypting any files on the victim’s system, WastedLocker first runs a few routine checks to ensure smooth operation. The ransomware uses a random executable or DLL found in the Windows system32 directory to elevate its privileges if it does not have admin control by hijacking a new copy of the legitimate file that is injected with the ransomware.
Security researchers also discovered a bug in the code that WastedLocker uses to determine whether the ransomware is running on a 32-bit or 64-bit system. The ransomware reads the KUSER_SHARED_DATA structure and checks the value of its pointer. If the pointer is zero, this would mean that the payload is running a 32-bit version on a 64-bit system. However, this is not a method that works for Windows 10 systems.
Once WastedLocker gets to encrypting files, it searches for all types of large storage devices, including fixed, removable, shared and remote drives. The ransomware works using an exclusion list instead of the common list of encrypted file types. Miniature files under 10 bytes in size are ignored and huge files are chunked and encrypted in 64MB blocks. Encryption uses an AES algorithm.
WastedLocker Ransom Note
For each encrypted file, the ransomware creates an additional ransom note. The encrypted files use a complex naming convention that includes the name of the organization or institution targeted and the wasted suffix. This means that a file named "report.xlsx" will turn into "report.xlsx.targetnamewasted".
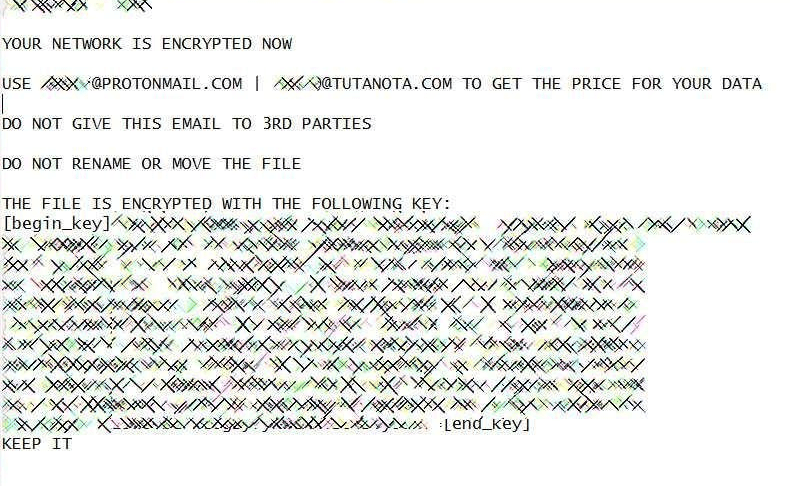
The ransom note used by WastedLocker is as follows:
[Name of victim / organization]
YOUR NETWORK IS ENCRYPTED NOW
USE [EMAIL] | [EMAIL2] TO GET THE PRICE FOR YOUR DATA
DO NOT GIVE THIS EMAIL TO 3RD PARTIES
DO NOT RENAME OR MOVE THE FILE
THE FILE IS ENCRYPTED WITH THE FOLLOWING KEY:
[key start]*[key end]
KEEP IT
The encryption exclusion list that WastedLocker uses is as follows:
- *.386
- *.adv
- *.ani
- *.bak
- *.bat
- *.bin
- *.cab
- *.cmd
- *.com
- *.cpl
- *.cur
- *.dat
- *.diagcab
- *.diagcfg
- *.dll
- *.drv
- *.exe
- *.hlp
- *.hta
- *.icl
- *.icns
- *.ics
- *.idx
- *.ini
- *.key
- *.lnk
- *.mod
- *.msc
- *.msi
- *.msp
- *.msstyles
- *.msu
- *.nls
- *.nomedia
- *.ocx
- *.ps1
- *.rom
- *.rtp
- *.scr
- *.sdi
- *.shs
- *.sys
- *.theme
- *.themepack
- *.wim
- *.wpx

