Vect Ransomware
Protecting digital environments from modern malware threats has become a critical necessity as cybercriminal operations grow increasingly sophisticated. Ransomware, in particular, poses a severe risk by locking users out of their own data and leveraging extortion tactics. One such emerging threat is Vect Ransomware, a highly disruptive strain designed to encrypt, manipulate, and potentially expose sensitive information.
Table of Contents
A Closer Look at Vect Ransomware
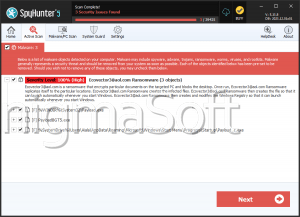
Vect Ransomware represents a complex and multi-layered cyber threat identified by cybersecurity researchers. Once it infiltrates a system, it begins executing a series of damaging actions that go beyond simple file encryption. Victims quickly notice that their files are renamed with an added '.vect' extension, transforming filenames like '1.png' into '1.png.vect.' This renaming convention serves as a clear marker of infection.
However, Vect's behavior is not uniform across all files. Some data is permanently deleted, some is encrypted, and others are both encrypted and hidden from the user. This uneven treatment increases confusion and complicates recovery efforts, making the attack more psychologically and technically impactful.
Encryption and Double Extortion Tactics
Vect employs the ChaCha20 encryption algorithm, a fast and secure cryptographic method that makes unauthorized decryption virtually impossible without the corresponding key. The ransomware's ransom note, named '!!!READ_ME!!!.txt,' informs victims that their files have been locked and can only be restored through a paid decryption tool.
In addition to encryption, Vect incorporates double extortion tactics. Attackers claim to have exfiltrated sensitive data such as databases, backups, and personal files. Victims are threatened with public data leaks if payment is not made, increasing pressure to comply. This dual threat, data loss and data exposure, significantly raises the stakes.
Ransom Demand and Communication Channels
The ransom note directs victims to access a payment portal via the Tor Browser, emphasizing anonymity and reducing traceability. Once connected, victims are instructed to engage in a chat session where attackers offer to decrypt a few small files as proof of their capabilities.
After this demonstration, payment instructions are provided. The attackers promise that, upon payment, a decryption tool will be delivered. The note also includes warnings against tampering with encrypted files, using third-party recovery tools, or reinstalling the operating system, claiming such actions could result in permanent data loss. Additional details, such as a unique victim ID and a backup communication method via Qtox, are included to streamline negotiations.
Despite these assurances, paying the ransom remains highly risky. There is no guarantee that attackers will provide a working decryption tool or refrain from leaking stolen data.
Infection Vectors and Distribution Methods
Vect Ransomware spreads through a wide range of deceptive and opportunistic techniques. Attackers exploit both human behavior and technical vulnerabilities to gain access to systems.
Common infection channels include:
- Malicious email attachments or embedded links disguised as legitimate documents
- Fake software updates and fraudulent technical support schemes
- Exploitation of unpatched software vulnerabilities
- Downloads from compromised websites or peer-to-peer networks
- Use of infected USB drives and pirated software tools, such as key generators
These diverse distribution methods make Vect a versatile threat capable of targeting both individuals and organizations.
Recovery Challenges and System Impact
Recovering from a Vect infection is particularly difficult. Without access to external backups, encrypted files are typically unrecoverable without the attackers' decryption key. Additionally, the ransomware's ability to delete or hide certain files further complicates restoration efforts.
It is essential to remove the ransomware from the infected system as soon as possible to prevent additional damage and stop lateral movement across networks. Failure to do so may result in further encryption or data exfiltration.
Strengthening Defenses Against Ransomware
Mitigating the risk of ransomware infections like Vect requires a proactive and layered security approach. Users and organizations must adopt strong cybersecurity habits and maintain robust defenses.
Key security practices include:
- Regularly backing up important data to offline or cloud-based storage
- Keeping operating systems and software fully updated with the latest patches
- Using reputable antivirus and anti-malware solutions with real-time protection
- Exercising caution with email attachments, links, and downloads from unknown sources
- Avoiding pirated software and unofficial activation tools
- Restricting user permissions and disabling macros in documents by default
Beyond these measures, network monitoring, employee awareness training, and incident response planning play a vital role in minimizing damage during an attack.
Final Assessment
Vect Ransomware exemplifies the evolving nature of cyber threats, combining strong encryption with data theft and psychological pressure. Its ability to selectively manipulate files and employ multiple attack vectors makes it particularly dangerous. Effective defense depends not only on technical safeguards but also on informed and cautious user behavior.