Spark
The Spark threat is a backdoor Trojan, which appears to be the creation of the Palestinian hacking group known as Molerats. Having in mind the tensions in the Middle East, it comes as no surprise that the Molerats hacking group has been very active recently.
The Spark Trojan appears to be propagated via phishing emails that have been specifically crafted to grab the attention of users in the Middle East who are interested in the political situation in the region. The emails in question would often appear to be in regard to the assassination of the top-general Qasem Soleimani, the conflict between Israel and Palestine, or similar events of significance to the region and its residents. Upon receiving the email, the user will be asked to open the attached file, presenting it as a harmless document that contains important information. Opening the attached document will allow the malicious file to exploit various vulnerabilities that may be present on the Microsoft Office service installed on the targeted computer. Some emails which were part of the campaign of the Molerats hacking group were not as sophisticated and had an executable file attached instead of a malicious RTF document.
Hackers from Gaza are targeting Palestinian territories, organizations, and governments using espionage and hacking campaigns. The results of the research into these campaigns prove that there is a new backdoor the hackers use to spy on government targets.
Cybereason Nocturnus have spent several months tracking espionage campaigns across the Middle East and discovered the Spark Backdoor, as well as other attacks that target individuals and entities in Palestine.
Researchers are unable to say for sure who is behind the campaign, but they have noticed the campaign is similar to previous attacks from MoleRATs. MoleRATs also operates under the name The Gaza Cybergang and is known to get involved with political campaigns. The group has run operations in the Middle East since 2012. It’s possible that another group is trying to pose as the Gazan hackers and are using MoleRATs to hide their identity through similar attack vectors.
The Stealthy Spark Campaign
The Spark Campaign uses social engineering to trick victims into an infection through the Spark Backdoor. This Spark backdoor isn’t new as it first came into the public eye back in January 2019 and has been used ever since.
MoleRATs use social engineering tactics that rely on geopolitical events, in particular the tensions and conflicts between Israel and Palestine, the assassination of the Iranian general Qasem Soleimani, and the conflicts between Hamas and Fatah in Palestine.
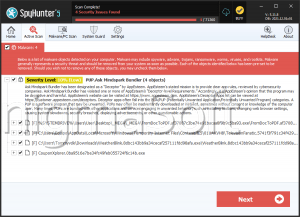
The image below shows an example of what the documents used in the campaign look like. Victims are tricked into downloading and accessing these documents, which will then go on to infect their computers.
The people behind the Spark backdoor campaign have done an excellent job of keeping under the radar. Researchers explain that the malware is packed with a powerful commercial tool known as Enigma Packer. The packer uses language checks to ensure that the target is an Arabic speaker before infecting them. These measures mean that it is more difficult to spot an infection, and it reduces the risk the campaign will hit the wrong target.
Researchers believe that the group is targeting Palestinians, in particular, Palestinians with ties to the government, to obtain sensitive information. The group will use the information to gain leverage and achieve their goals, whatever they are.
The Ongoing Espionage
The idea of an espionage campaign like this is nothing new. Espionage is a game that all countries play with each other. Nation-states use espionage as a means to breach security and obtain information in a game with very high stakes.
Campaigns like this are useful because they allow governments and groups to target ring leaders. A carefully conducted plan can also disrupt communications and plans and sew the seeds of mistrust between leaders.
The Molerats hacking group has made sure to heavily obfuscate the Spark Trojan with the help of several publicly available tools. The Spark is able to detect what is the default set language on the compromised computer. This backdoor Trojan is programmed to only target machines that have Arabic as default set language. If the default language set is anything but Arabic, it is likely that the Spark will halt its operation.
The Spark backdoor Trojan connects to the attackers' C&C (Command & Control) server to receive commands from its operators. All the traffic between the C&C server and the Spark threat is securely encrypted to avoid the prying eyes of cybersecurity researchers. Once the Spark Trojan has compromised its target, it will be able to:
- Download and execute additional files.
- Execute remote commands from the C&C server.
- Record audio via the system's microphone.
- Record video via the system's camera.
- Launch a keylogging module.
- Collect information regarding the system's hardware and software.
- Encrypt and archive all the collected information.
- Transfer the collected information to the C&C server.
According to reports, the Molerats hacking group has released a new and updated variant of the Spark Trojan, which has been dubbed the EnigmaSpark Trojan. Both threats are capable of causing significant harm to the targeted systems. It is best to invest in a legitimate anti-virus application that will protect your PC from cybercriminals.