Reco Ransomware
File-encryption Trojans continue to be the most important part of the toolkit of any cybercriminal – these destructive cyber-threats are the perfect extortion tool for anonymous cyber crooks, as they give them a very strong bargaining chip by holding the victim's files as hostages. Unfortunately, recovering from ransomware attacks is often an impossible task, and victims end up having to ask the attackers for help that never comes for free.
The Reco Ransomware is one of the latest file-lockers to look out for, and a closer analysis of its behavior revealed that it is not an entirely new threat – it is based on the STOP Ransomware project, and uses an identical file-encryption routine to damage the files of its victims. The distribution techniques that the authors of the Reco Ransomware use to spread their threatening program may vary – some of their preferred tricks are:
- Phishing emails that contain a bogus attachment.
- Files hosted on warez websites.
- Pirated software and media.
- Fake downloads and updates that are promoted via malvertising campaigns.
It is not a good idea to mess with shady digital content so that we advise you to avoid downloading programs and media from torrent trackers or other non-trustworthy sources. Furthermore, you should never rely on safe browsing habits to keep ransomware away on their own – it also is advisable to invest in a reputable cybersecurity software suite that will keep potentially harmful files away from your computer.
The Reco Ransomware Causes Long-Term Damage to Your Files – Backups may be the Only Salvation
Failing to stop the Reco Ransomware's attack is guaranteed to have devastating consequences due to this file-locker's ability to encrypt a wide range of file formats and render their contents inaccessible. The information needed to complete the data decryption process is generated for each victim of the Reco Ransomware randomly, and it is transferred to a control server owned by the ransomware's authors. They offer to sell this key piece of information to their victims, but their price tag is rather high - $490 for the first 72 hours and $980 after this. Naturally, the crooks behind the Reco Ransomware are asking to receive the payment via a Bitcoin transaction since this can preserve their anonymity, and also make it impossible for the victim to reverse the transaction. The full version of the message of the attackers can be found in the file '_readme.txt,' which should be present on all computers infected by the Reco Ransomware.
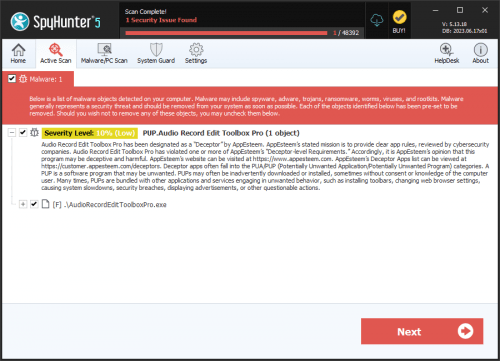
The attackers ask to be contacted via the emails gorentos@bitmessage.ch and gerentoshelp@firemail.cc, and also claim to be willing to decrypt 1-2 files for free so that the user will have no doubts about the ‘honesty’ of the criminals. While it is recommended to take advantage of this opportunity, we assure you that paying the price is not advisable! You may end up being tricked, and will never be able to recover your money. The best steps to take is to eliminate the Reco Ransomware with the use of an anti-malware utility, and then look for popular data recovery options.