Mike Ransomware
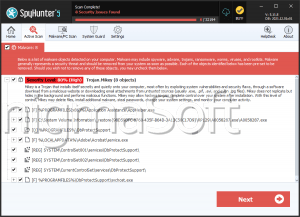
One of the most recently detected ransomware threats is called Mike Ransomware, and it appears to be a variant of the HildaCrypt Ransomware. However, there is one significant difference between the HildaCrypt Ransomware and the Mike Ransomware; the latter is built to masquerade as a copy of the notorious STOP Ransomware. Malware researchers have not determined why the authors of the Mike Ransomware would take such an unusual approach.
Propagation and Encryption
It is not yet known what infection vectors are employed in the propagation of this data-locking Trojan. Spam emails containing infected attachments, as well as fake application updates, and bogus pirated copies of legitimate applications are among the most popular propagation methods linked to the spreading of ransomware threats. When the Mike Ransomware infiltrates a system, it will scan the data present to locate the files, which will be locked later. Once the Mike Ransomware executes its encryption process, all the newly locked files will have a new extension added to their names - ‘.mike.’ This means that a file that was called ‘nbg.mp3’ originally will be renamed to ‘nbg.mp3.mike’ once the encryption process is through.
The Ransom Note
The Mike Ransomware also drops a ransom note called ‘_readme.txt.’ Almost all ransomware threats that belong to the STOP ransomware family have their ransom notes called ‘_readme.txt,’ and since the Mike Ransomware is posing as a STOP Ransomware variant, the attackers have opted to adopt the same name. In the note, the attackers demand $980 as a fee. However, they also claim that victims who manage to get in touch with them within 72 hours of the attack will get a 50% discount, and the ransom fee will drop to $490. As usual, the ransom fee is required to be in the shape of Bitcoin, as this helps the cyber crooks keep their anonymity. The authors of the Mike Ransomware have even used the same email addresses that most STOP Ransomware variants use - ‘gorentos@bitmessage.ch’ and ‘gerentoshelp@firemail.cc.’
If you are a victim of the Mike Ransomware, do not fret since this is not a variant of the STOP Ransomware, but a copy of the HildaCrypt Ransomware and there is a free decryption tool available. Also, make sure you download and install a reputable anti-spyware application that will keep your system secure in the future.