Trojan.Mikey
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
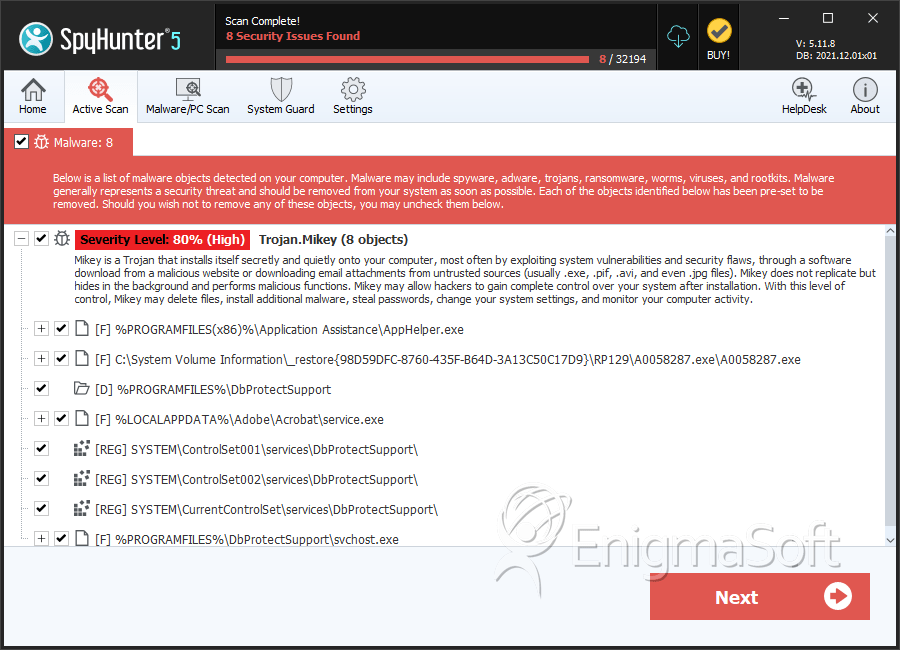
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 17,066 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 20,701 |
| First Seen: | April 20, 2015 |
| Last Seen: | October 7, 2023 |
| OS(es) Affected: | Windows |
Trojan.Mikey is a computer threat that may infect computers silently and create multiple files that may be used to execute threatening operations, as well as to communicate with remote Command & Control (C&C) servers. Con artists may use Trojan.Mikey to execute a large number of harmful actions such as downloading additional threats, turning the infected computer as part of a botnet, gaining illicit access to the user's data, etc.
The scariest thing about threats such as Trojan.Mikey is that they may use advanced methods to make their presence unknown. Trojan.Mikey may place its files in multiple system folders, and Trojan.Mikey may create Windows processes with unsuspicious names, which users would never associate with a threatening Trojan. The fact that Trojan.Mikey may stay hidden on an infected system and execute its threatening operations without ever giving out its presence is certainly something to be afraid of. That's why it is important always to keep your computer shielded with a reliable and up-to-date anti-malware software that can detect and eliminate threats like Trojan.Mikey as soon as they attempt to do something bad.
The Trojan.Mikey's distribution may occur with the help of several threat propagation techniques such as pirated software, corrupted e-mail attachments and fake downloads. Apart from securing your computer with a good anti-malware program, you also should avoid downloading software from untrustworthy Web destinations. The same applies for e-mail messages – never open messages from unknown senders, especially if they contain links or unknown attachments that you didn't expect to receive.
Table of Contents
SpyHunter Detects & Remove Trojan.Mikey
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | service.exe | e17fa9d8b4f3932fff737f8775286e75 | 181 |
| 2. | svchost.exe | b326845d692c766adea130bb9a57eedf | 148 |
| 3. | service.exe | 4cc97bd0d7fc0da6b2c7829460bcfc73 | 14 |
| 4. | msiql.exe | cb8986e89cf21fcd243c0aaa53417fe6 | 3 |
| 5. | svchost.exe | ba9f9c7b08ace02aea022878a9895df3 | 2 |
| 6. | svchost.exe | dff11ef6ede23f8b17dffbf01638cf85 | 1 |
| 7. | svchost.exe | 7039f234a0c71d0d4c8a40516d214b71 | 1 |
| 8. | junlsen.exe | 8efc257946d9ca90c1e48e8b5d24037d | 1 |
| 9. | cmutXP32.exe | 1d2a8b21bf33f1b68bf73c7e74c7c468 | 1 |
| 10. | svchost.exe | 960d2800811bb950462305004b06c70a | 1 |
| 11. | svchost.exe | 683d6050fc73c31174a9470bc169a250 | 1 |
| 12. | msiql.exe | e79083cc7ba95c44c5441a7b42f1df93 | 1 |
| 13. | msiql.exe | 942d0f872b35b541c5831f3880ab59e4 | 1 |
| 14. | msiql.exe | e8e7829763487ca324102f961baa2a5f | 1 |
| 15. | msiql.exe | e319063d9917961c1a44d62bde129bd3 | 1 |
| 16. | msiql.exe | 5367c593583f80bb6ba859da2a65bdfa | 1 |
| 17. | msiql.exe | 3425dae667df5ff0e51ea1be624f3b3f | 1 |
| 18. | msiql.exe | b599ceeb3b5028076e03e7ffa6b79205 | 1 |
| 19. | msiql.exe | 163598700e93f1d65a0acc18eaf30870 | 1 |
| 20. | msiql.exe | a9785938a2b76d9296ed8ff7e571180f | 1 |
| 21. | svchost.exe | c7798850d520b6ddabfc853329d996d4 | 1 |
| 22. | msiql.exe | 0883c5f3c9cc9d6eeba6b63a2fb6914b | 1 |
| 23. | svchost.exe | f64fe81747c11222d1b8c266ce8525ec | 1 |
| 24. | Dq1njlO3qzrRK.exe | 7c4c9ffc4359beefc8d96ffc063f914f | 1 |
| 25. | rekgernel.exe | d8729ba91a0a86a3e04b091ec529e1a5 | 0 |
| 26. | file.exe | 8c06b8e0f91aa4e56a6d686a54c59eb0 | 0 |
| 27. | 7895dfd152460b755407afff38944ee4 | 7895dfd152460b755407afff38944ee4 | 0 |
| 28. | bd579517b4977d4807e1e5ac39fddb03 | bd579517b4977d4807e1e5ac39fddb03 | 0 |
Registry Details
Directories
Trojan.Mikey may create the following directory or directories:
| %APPDATA%\BoldSound |
| %PROGRAMFILES%\DbProtectSupport |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.