Globe Imposter Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 18,035 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 1,526 |
| First Seen: | January 3, 2017 |
| Last Seen: | March 14, 2026 |
| OS(es) Affected: | Windows |
The 'Globe Imposter' Ransomware is a ransomware Trojan that was first observed in the last weeks of 2016. The 'Globe Imposter' Ransomware is a bogus version of Globe Ransomware, a well-known ransomware Trojan. Hiding a less efficient threat by disguising it as a more powerful or better- known threat is a common deception method used by con artists, and this method was used before in ransomware attacks. For example, there are countless ransomware variants that impersonate the well-known CryptoLocker ransomware Trojan, despite using a less powerful encryption or not using encryption at all. The 'Globe Imposter' Ransomware is typically spread using corrupted email attachments that use macros to download and install the 'Globe Imposter' Ransomware on the victim's computer. Disabling macros, using a reliable security program, and avoiding unsolicited email attachments are all steps that can prevent the 'Globe Imposter' Ransomware from being installed on a computer.
How the 'Globe Imposter' Ransomware Carries out Its Attack
The 'Globe Imposter' Ransomware uses the AES-256 encryption to make the victim's files inaccessible. The 'Globe Imposter' Ransomware creates a list of files on the victim's computer that have certain file extensions and are suitable for the encryption attack. Although the 'Globe Imposter' Ransomware is not as sophisticated as other ransomware Trojans, its encryption method is powerful and will lock the victim's files completely, preventing the victim from accessing the encrypted files. The con artists responsible for the 'Globe Imposter' Ransomware attack will have the decryption key necessary to restore the affected files. In the 'Globe Imposter' Ransomware attack, the victim is instructed to pay a ransom in exchange for this decryption key. The 'Globe Imposter' Ransomware carries out its attack in the background and can take up to several hours, depending on the volume of data to be encrypted.
What are the Consequences of a 'Globe Imposter' Ransomware Infection
The files that are encrypted using the 'Globe Imposter' Ransomware are easy to identify since the extension '.crypt' will be appended to each file's name. Files encrypted by the 'Globe Imposter' Ransomware are not readable, and they will show up in Windows Explorer as a blank icon. The 'Globe Imposter' Ransomware delivers its ransom note in an HTA file named 'HOW_OPEN_FILES.hta' dropped on the affected computer's Desktop. The 'Globe Imposter' Ransomware ransom note imitates the ransom note used by the real Globe Ransomware and its variants. Below is the full text of the 'Globe Imposter' Ransomware ransom note:
'Your files are encrypted!
Your personal ID
***
All your important data has been encrypted. To recover data you need decryptor.
To get the decryptor you should:
pay for decrypt:
site for buy bitcoin:
Buy 1 BTC on one of these sites
1. https://localbitcoins.com
2. https://www.coinbase.com
3. https://xchange.cc
bitcoin adress for pay:
jlHqcdC83***:
Send 1 BTC for decrypt
After the payment:
Send screenshot of payment to alex_pup@list.ru . In the letter include your personal ID (look at the beginning of this document).
After you will receive a decryptor and instructions
Attention!
• No Payment = No decryption
• You realy get the decryptor after payment
• Do not attempt to remove the program or run the anti-virus tools
• Attempts to self-decrypting files will result in the loss of your data
• Decoders other users are not compatible with your data, because each user's unique encryption key'
Dealing with the 'Globe Imposter' Ransomware
Avoid paying the 'Globe Imposter' Ransomware ransom. The people responsible for these attacks may ignore victims, demand additional payments, or fail to deliver a working decryption key. More importantly, paying the 'Globe Imposter' Ransomware ransom allows these people to continue creating threats. Instead, computer users should back up their files regularly to the cloud or an external memory device. In the event of a 'Globe Imposter' Ransomware attack, computer users can then simply restore the affected files from the backup, nullifying the 'Globe Imposter' Ransomware infection.
SpyHunter Detects & Remove Globe Imposter Ransomware
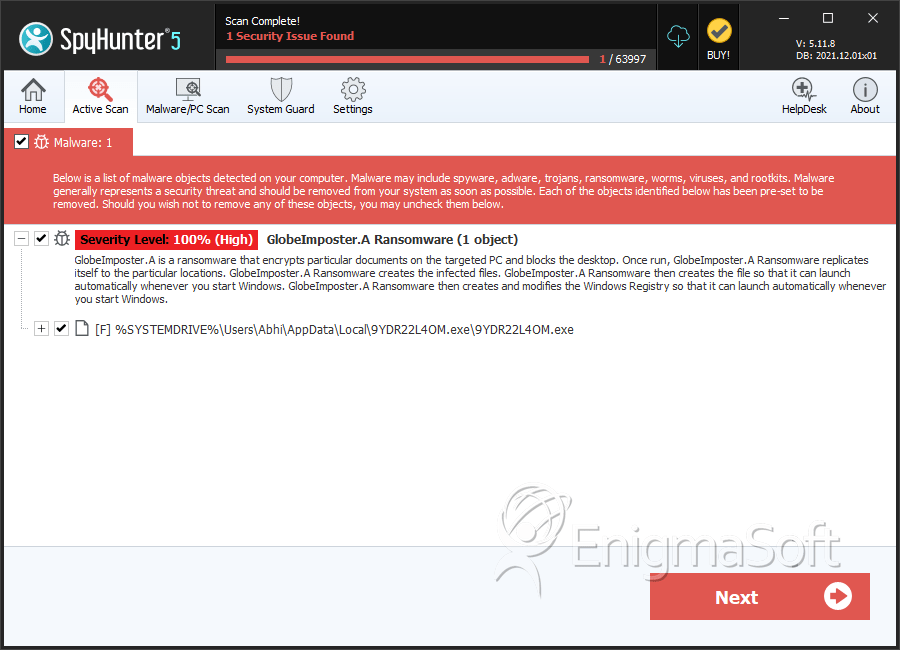
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 9YDR22L4OM.exe | d6c7bbffa256e952070a2cd84bfea821 | 418 |
Analysis Report
General information
| Family Name: | GlobeImposter.A Ransomware |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
ded8314004b6cc954c4168c232a3245f
SHA1:
2b2e9e6691b3a213c9610d3a53318d28fc16f676
SHA256:
29B01C1FE867AC1D3B57D22060B6EB1ACA2CDD52AECC602F6AAF0B04F044DD9D
File Size:
54.27 KB, 54272 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- No Version Info
- ntdll
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 142 |
|---|---|
| Potentially Malicious Blocks: | 106 |
| Whitelisted Blocks: | 36 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- GlobeImposter.A
- GlobeImposter.E
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| \\ | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\bootmgr | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\bootmgr | Synchronize,Write Attributes |
| c:\bootmgr.datakill | Synchronize,Write Data |
| c:\bootnxt | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\bootnxt.datakill | Synchronize,Write Data |
| c:\dumpstack.log.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\how_to_back_files.html | Generic Write,Read Attributes |
| c:\sandbox_stage\how_to_back_files.html | Generic Write,Read Attributes |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\03\14\0314ae54cd57eb38bee31339ba1ed80cc105127d_0000059240 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Show More
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\03\d8\03d8cc9fc82dd3a258f9a1360b17fdaf3d52061a_0000090960 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\04\ba\04ba8325e6d1ec0e5bb8bad7133b90dbc5397d49_0000097872 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\09\0d\090dfacbee3eb2f6326d59fd59d59b39ddffbb6b_0000098624 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\09\e5\09e5f89038ea122648f88e79e7211a6549211baf_0000388888 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\0a\99\0a990e86adeaa2f564a0cc242ffd4849fa5396a7_0000043608 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\0a\c8\0ac860699528b948907f67699c4f1ba54dbd0490_0000112488 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\0a\fe\0afec9db6a116179905347f038e8040cd96047c0_0001020200 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\0c\26\0c26c21f709416f7aada1e9265976406fc89eb1b_0000089984 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\0e\1a\0e1ad270d620f142847b72fd04ade2fd3901d577_0000785696 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\11\33\1133ccbc2e34f044a4b2fe0c305ff27037871104_0000037248 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\14\0f\140f5341e90f5db72daedbf436469c53155f9a5c_0000080144 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\15\8b\158bb837ae0f8ca4b36eaea71c00e31fa7f5ce45_0000918344 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\18\9f\189fc68a165e2e9e979b6db5a03ac08c796a9de3_0000136576 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\18\e9\18e943b54f146f5adaa3bb0fee8fb4668f287874_0000228184 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\19\2d\192d6dd759f5cbeb6551e12982d270bfe13a4de9_0000203408 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\19\93\19934f6506676062d94f034ee06f0787c5006b75_0000017232 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\1c\31\1c31c0d5b7c866472a283b87399ffb075d1a4a50_0000257408 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\1c\4b\1c4bf478e42f53b0acdbd54edd88e693cb9caee9_0000068928 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\1f\37\1f37b51413fb298130b1ee43d4f174786b690b0d_0000491008 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\1f\f8\1ff88f7980ded35a9375ed07d4f278650bf64ea5_0000642320 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\20\43\20435cdb7b3bfb86919481e69c40c363a51e611a_0000052888 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\21\c8\21c86ea4745c4bfb65ffd29f7093dab654944893_0000982124 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\22\3c\223c9bd2434a2e5ffb8efb6c0ff616992d28fd3c_0000154384 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\24\99\2499704eebcdd6e8661c99828ec52231395b9839_0000167424 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\25\2e\252e45fd7845b7b702d0514052bc9fbc42987896_0000189771 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\26\36\2636bf99081b851a103e31ccde56149634cb5a08_0000291864 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\26\cb\26cb2aa9c21097b8c82ba92df84b4e20c39afff2_0000048456 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\27\92\2792859513a9637281b0ef26fcbcfd5ec22dacb3_0000047944 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\28\7f\287f1441b57a06c3b04cf2cba15a310ed70af6a6_0000040208 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\2a\92\2a92aa2410b3e23af9be77629f7508a7366d9dd1_0000018954 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\2b\1d\2b1dd7545572cf4972e4a0f16460e4f7088004dd_0000082760 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\2d\c0\2dc00c28db405dfea4cac74d128cbe3d705f603c_0005718872 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\2d\f2\2df243f0f2958c799e4c848419498e0f23123d88_0000456280 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\2f\0d\2f0d6072865e71693cd131c0949f768681de8cae_0002103120 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\2f\b4\2fb453460158e3d23d1ac7b0c9f3ed71bfd9140c_0000992009 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\30\81\3081baff4fc49c2bc5610bd4fbae4228c52538f8_0000073024 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\31\87\3187a4bd82f7bab337edc2d5b268b6251fad6657_0000066376 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\35\58\35582c22b407a840dd3b12c029a2af38a225a6dd_0000114264 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\36\18\36184a6a2d69e0a6185c605b8e4708fc438bc4d4_0000347496 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\36\a3\36a3e8071ca97be5c53c865b2b524c527545c740_0000056128 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\3b\f1\3bf12583e8c69de866cd9f8532f449bed3a46443_0000095568 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\3c\8f\3c8ff7c07f4a760f76f9e7bf3c8fa250ec560b78_0000288080 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\3d\c0\3dc0fedb744d6f57d4f94b2e7ae2b8ebef901acb_0000163416 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\3e\53\3e53580b3ef3380bf951630153bf808a36c115ff_0000439136 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\3e\a6\3ea6405d187b6bb93567cd546aa3530de618ec06_0000047432 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\3f\7f\3f7f93b93ec2d6ac51f330b16ac106c6ef63fbbe_0000111936 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\40\6d\406d0d70ea72db3476740e39eaa4e0b3e3ea1ad8_0000073544 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\40\d3\40d3874b2a6fbed3710a00c5a92b801ebb0ac92e_0000814288 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\41\86\418666a289daa472beb9c7df1078cd25eb5cea38_0001107724 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\42\00\42002361dfdc6693e3c1b9c22be0344d243ca7b6_0000222720 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\44\64\446480c82d116c3f55db2606cda27e5d60501f54_0000038784 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\46\5f\465f35c8a865b5904474bef9be163e680549f360_0000496912 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\4c\65\4c6554df22ce31c6b18c52c288fbbcba2440d036_0000026432 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\4c\8d\4c8d18c1386d6e33256d2d89a34129eddaa6084e_0000348416 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\4d\35\4d355b87caf047e88294bc9e6f9a6894d18d96b5_0000259672 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\4e\8f\4e8f03f4a3cdc48f0d67672e563de78589905ad5_0000038208 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\51\a1\51a1207ca4915c5160faf0470e89291dd825a5be_0000014656 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\52\39\523924d8d3550a2a04300a31fd10f34745677abd_0000056000 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\52\bd\52bd4d66f142965c6309228c2fcb7959f0403f48_0000917992 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\53\ef\53efbca83efaac3104b255b56e2c5ac1342d0447_0000057672 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\56\d6\56d6bfec743f99887a185078a6a5d3286be4ecae_0000087880 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\56\ed\56edf5c03750d5833f1f5538cb7ff61f334f4afe_0000078664 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\59\bb\59bb81d6579dc7c9cfb7b4e28831b57504b006cd_0000042160 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\5b\6c\5b6cbcbe5b3cb6fb91ef11ec412ac287604f9f7e_0000035160 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\5b\81\5b81c0894829e1cdb5aae757340a2dad126295ed_0000221008 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\5c\b3\5cb3c18afe98b6fb86d9901b1069e86a8e445934_0000991448 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\60\7b\607b961cc8d008a524a021302216c936eaf316e8_0000026472 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\60\c4\60c427c056e2c0c43b73dbee38ecb286a559e06b_0000143680 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\61\19\6119c26c40306cdb272f3add083dbe656ea4996f_0000035136 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\63\56\6356014c2f77f3b2243520415a0252ac3ee80eca_0000325440 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\63\96\63961cf5c7ab1775a24de1b720da5dbd4d79cdd0_0000024128 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\64\06\6406b4a2ead1842236621965522fab1533b74216_0007020336 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\65\23\6523163f5c7eba49a9915aa1122d40aee90065a6_0005373632 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\65\69\65695b52f58ef0b9991edf2c434c0bb9e77f54ae_0000154424 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\65\79\6579af37ff6336d9fa20f1a5458ace3e7542ceba_0000088336 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\67\0e\670e66c29a073348c0caccd303fb4facc888c6a0_0001106633 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\67\69\67697c4f5ae6dc933493e177701dead90f4a684b_0000184144 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\68\2c\682c4dc5460fcd7f283e85398f3645ded29b494d_0000046352 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\68\78\68787bc71bb1825ab10eb32c5bc44d96c5f9112e_0000193034 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\68\b8\68b828bb74900cfc6891a2a562ea1343791d4636_0000070976 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6c\21\6c21484ca7b1fa4daac7d1576c430a8df13c63d5_0000139264 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6c\ad\6cad4efbc262788779637653eb209dea2c02dd46_0000127672 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6d\63\6d63736f39e728ce3f4cd5adf6ccc9c56c200e87_0000040960 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6d\80\6d80f83f10ec2bfcb3a51280ccda13c75e3131bf_0000098112 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6d\bb\6dbb44d79339c9cd691ed5e822a6408e61e5cc55_0000199832 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6e\6b\6e6b184a2473de3a5c73e4569b0b8705d4896fab_0000739136 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\6f\19\6f19625644de0954d0309d5c5a508d006387a9d8_0000102912 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\71\18\7118e5f7d5f7c332790eae27cfcd4a9e840cac0e_0000216424 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\71\41\71411f50fbfbb9f77d61860aac3b9133d428274f_0000284160 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\71\4e\714ed3e2e57700bab8ec44a415de7e3d06117253_0000051528 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\71\b4\71b4727f354f1f8bced5c1feb5f26ef5eb00b2cc_0000030992 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\73\50\73505eb20ecb566b8c32f498b6103ec654830626_0000025846 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\75\64\75642098aa8a6bb5207965313678fe3b40a8bf30_0000069464 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\78\c1\78c1b3a4466de76cddc25a2693f0367148fabfc5_0000365928 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\79\0b\790b3e9f68b37adf26b3c40cf2a74b89acc58d19_0001071555 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\7a\bc\7abcd08f5d305064814d9b2465c2c24ed146edf1_0000028496 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\7b\c6\7bc690a423ca0fd4cbeb13b44d860a72ca047fce_0000287056 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\7d\d9\7dd913669e5c478a90324dab68b9d28420134733_0000019792 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\7f\d7\7fd7f36b5acbe69de6c966b397341fd1ddbb04a1_0000055632 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\82\fb\82fb9815eac82faeef7d14e7d29ca84f5f060005_0000080656 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\83\e7\83e7c2759a4ef06e6e8918bed7deb5ea145378d9_0000020864 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\84\f9\84f908c727213c1ab4516e95ff5f36cccd39f43e_0000063304 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\85\cc\85cca7f8313c147653c57b36ef82dcc60b105de6_0000453448 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\86\46\86468d3cfd1be9ed56b186f5209f76394cc01e2b_0000342344 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\86\67\866728449a92a56cf533fdeea8ae1d1af1d91108_0000076112 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\86\76\86760a3383a2c0da67bfc0929ed5417d19e36bcd_0000116824 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\87\10\87103a892bb514a93d485fba221bacb9da3aae25_0000057344 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\88\50\8850c653010181bc974b76d274f912cbfc07382b_0000202088 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\89\02\89022f5b02de51bff5fedba4184501b4a21f23ec_0000191064 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\8b\17\8b17f476b880e801e564b18de0835df8f89d2d67_0000207632 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\8b\30\8b30a4b163fef5d2441de1e4d34aee6d55e93668_0000109656 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\8c\27\8c272a12aeb499401aa0f17c6f5b725323475d9f_0000024848 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\8e\a0\8ea0d8ef63aa5de09c2998177291eb8bdd9fb301_0000090112 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\8f\6d\8f6d42ef5e2809572651b70da0f16551ec0d3d4f_0000024848 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\8f\d8\8fd8b2470e3dc684ce45dc14689dc6df95ec0721_0000989016 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\91\67\91670367087fa5baf2f89f705f08a8b0ecb42fe9_0000055112 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\93\19\93192a5c75867600a563b154797f35025fe832c2_0001094446 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\94\b4\94b4ec8580cc26db875ad3fd318a9645267dd68c_0000074672 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\95\d7\95d7fca7a1b6e3fcc7c36bc9278f410f50b391e8_0000084328 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\98\9a\989adfdd5b0b6f3d8711a294423c37b549480c43_0000077184 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\99\67\9967319345b84634a95f9df9089a9b4486f7c10a_0000019840 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\9a\2b\9a2b32982aa72c387877fb045d9618f47899df81_0000024896 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\9c\03\9c039156bd63700fcd7bfcd2c985e08dac1f97b6_0000154384 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\9c\b5\9cb595055b44e5569da650cd232a4448e5d2e38f_0000042152 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\9e\6a\9e6a0421c29afdee8263c5a49bc1bfab67c79708_0000263168 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\a1\af\a1af4a9f163a45dcc9f4a6903ac02df0e141e632_0000333600 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\a1\d2\a1d2aa82b7d2bc0fe2d116aa908af8847ee92dac_0000982312 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\a3\3f\a33f933b6192ad4a8f921bad822ce69576635d9f_0000042168 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\a4\fc\a4fc5b01bb3c8cacdd75ebf398be244ca5ae859d_0000719521 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\aa\35\aa35f5a24683d421b8c95e45c1020fa9acdf892f_0000142336 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ba\67\ba675fc5a72b2c9c6f7387a91555e7a5f542e853_0000022872 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ba\8f\ba8fb85f0a8fa5c97299ce9acd7f72f351767d2b_0000069440 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\bb\aa\bbaaf5bb82635e2fb45d5bd6179387bc65b070b1_0000374624 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\bd\be\bdbe8f3e52ba540ff897fdf3af4d1174dc69009a_0000382792 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\bf\61\bf618549b330c40a6e8ed0156106963dfd8479a0_0000033552 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\bf\89\bf89db52f2409c81bb771933e148cffe4fa52ef5_0000071504 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\c0\7b\c07b2ec98f4ab7281c2a53c6330c6c72d959765b_0000855320 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\c1\16\c116aa50948135da83d16373070d41d8f4bb5cac_0000370496 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\c3\42\c34215683eca6e9cc470198bfa59bd67d5d3868d_0000821608 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\c4\ac\c4ac4568eecacd57e0aea7e8ba7d43e83e0dfef3_0000088400 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\c8\32\c8321cb4f2fa7cd14f27d3f37cda066d8c8ab502_0000128856 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\c9\22\c922e9ce75c78d464c5eae656a2b46bb2e2377de_0000045256 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\cd\6e\cd6e4c2efbe22e5712de745f7d9cdebd29ac117c_0000073536 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\cd\93\cd93daaf961d61fe82ae2489e786d08efb9da466_0000072032 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ce\4b\ce4b9bf4c3b0f7c2787bb384f5b140a2837fc2c3_0000029968 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ce\c5\cec559ad6d5bcc6bcf6d36b20edd27937b87d33b_0000048968 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d0\a5\d0a57fe98e8dfe652e316cf03c95cbf29b94a8d6_0001063280 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d1\40\d1400e46208c6cd523f4aef61af7513363c1c5a9_0000021832 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d1\9e\d19e655b2d61d92a8eb1a5062c0f85a2df7ac42c_0001961561 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d3\0f\d30f8cfcdb977d1670af7f5aa5a16d152f901694_0000496912 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d3\4a\d34a1b1fa173bb331c58fea9a7a332c1d396f1ba_0000027520 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d4\32\d4329f51662ee69f89cfa3b17ac5bb2bb9e9090a_0000119320 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d5\22\d52217280f93870d4940d1727941fdb3b29ede83_0000070992 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d7\12\d712667b72d23443fd8d4d2db703f100b52df2f4_0001104686 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d7\d7\d7d7bf0d13d4d441b27fd2dfea0534b990d1df6e_0000030544 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d8\43\d8433cd98974970a0f16cc42f26eb9082a5b3694_0000139264 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d8\e4\d8e4417807e31c2363526f62a51c3926b92297b5_0000038760 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\d9\06\d9066c707e6f6ec05d8dd18f557202ff9397b7e5_0000134144 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\dd\e8\dde85fa1488657a11bf250c467620ebdfae8cfee_0000026965 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e1\52\e152a19931907d7500de3cc356ca92b51793aae2_0000157056 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e2\27\e2274d095b0dc6ce94492d34d4838ea3522f9a67_0000102912 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e3\d1\e3d1e4d26bbf7c1f1a96159e215f8dde08dc7672_0000139264 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e4\60\e46096f1dd0003459bd9788dbc2b63af139a55a7_0000042312 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e4\8b\e48bb5fb086a6892be0fe42469b9d32b98ee35ba_0000698712 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e4\d9\e4d982f5a3b2b72a3b3dbda78a868ffa88cff4d3_0000018240 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e5\13\e513dd19714559226cd52169fbb4489ca5740e88_0001475584 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e5\46\e5461252501ab2aff5e30b36361760beca56e305_0000141088 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e7\15\e715f4b669911eae050e48e21041041ebdf5344b_0000097040 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e7\41\e741ed30e98f9910c51ee36abf343fcab271abf1_0000139264 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e8\08\e8082f195480295c6f5f8d5340cfbe0471dfd099_0000052752 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e8\20\e82066a1723ea04bad3df976bce42470007a53fd_0000158592 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e8\e8\e8e86def440f0a60f557624f11563734adc67a99_0000160016 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\e9\ef\e9efcaa597f28e9d1002207e6da5e3559cff1830_0000126272 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ec\d2\ecd220a20092c0a03a9f122ad6ca849bb4714cb8_0000142664 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ed\5f\ed5fe0d60bc3f41c01ccc3f756145c3bf61ebba4_0000511360 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ed\f9\edf955d1ae4fd25d120af8eac863dc7fd6ba275b_0000102400 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ee\90\ee90175c171638661cc0f4c65104946d6be9025b_0000195432 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\ef\99\ef99998c7157e0be17940ced8a275af5c4e0fd6b_0000067584 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f0\6a\f06aff4b352fe2ec5452ba56602a941bbd48eaa8_0000406376 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f0\b6\f0b6a7890b6ecd649e4fc8f76a435490084bd8a8_0000313880 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f1\f2\f1f27cdc70f5456fc0e4e28ea1ead8a0372d689f_0000019328 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f2\b1\f2b106447748206ce783ba0bd8ba2baeba0865e0_0005073240 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f5\15\f5152bc047ddc2097db222364f3a5b71d713d87e_0000997861 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f6\b8\f6b8ddfc5031d4c34e7cd12e759c723783a09e81_0000095552 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f7\1e\f71e364d71ce68918ba1d04fd1888e8a63538808_0000139776 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f7\b3\f7b3c52d7a5a0108e9dfd350e989f28f9f7f5a15_0000188736 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f7\b5\f7b5fd4c7f08f2127e2a5fbabe04cc06df1276dd_0041213008 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f9\07\f9079abaaa6e2dd1d4c7ec339a378325146f7475_0000022352 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f9\1a\f91a4485b3210b4b4b5e835f0919459f13ee8e44_0000027920 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\sandbox_stage\mnt\nas\stage\samples\whitelist\f9\90\f9902b184ad03f3770ca273ef7c0ea2b9cdf970d_0000025896 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
15 additional files are not displayed above.
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKCU\software\microsoft\windows\currentversion\runonce::browserupdatecheck | C:\Users\Ervtkylc\AppData\Local\2b2e9e6691b3a213c9610d3a53318d28fc16f676_0000054272 | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Encryption Used |
|