CONTI Ransomware
 Ransomware threats are one of the worst pests one can come across online. A threat of this type would infect your computer, encrypt your data, and demand cash in exchange for a decryption key. Among the newest spotted data-locking Trojans on the Web is the CONTI Ransomware.
Ransomware threats are one of the worst pests one can come across online. A threat of this type would infect your computer, encrypt your data, and demand cash in exchange for a decryption key. Among the newest spotted data-locking Trojans on the Web is the CONTI Ransomware.
Propagation and Encryption
The CONTI Ransomware is likely being propagated via spam emails. Usually, cybercriminals would target random users who would receive a fake email containing an infected attachment. If the user opens the attached file, their system would be compromised. Malvertising campaigns, pirated content, bogus software updates, and torrent trackers are among other commonly utilized infection vectors. The CONTI Ransomware would scan the user’s system and then trigger its encryption process. This file-locking Trojan uses a secure encryption algorithm to lock all the targeted files. It is likely that all the documents, images, audio files, videos, databases, and spreadsheets present on the system will be encrypted. The newly locked files would get an additional extension ‘.CONTI.’ This means that a file, which was named ‘silver-can.jpg,’ will be renamed to ‘silver-can.jpg.CONTI’ after the encryption process has been completed.
This Week in Malware Episode 18 Part 1: CONTI Ransomware May Be Successor to PC-Hostage & Data-Encrypting Ryuk Ransomware
On the surface, CONTI works like other ransomware of its kind, but with some differences involved. The CONTI ransomware can support multi-threaded operations as part of its work. Although this isn't unique since other malware does the same, this particular ransomware manages a large number of threads – 32 to be precise. That allows the CONTI ransomware to encrypt files faster compared to other threats of its kind.
Other unique details seen in CONTI include exceptional control over encryption targets using a command-line client. The ransomware can be configured to skip encrypting local drives, aiming at data on networked SMB shares by using a list of IP addresses fed through the command line. That allows the threat to cause targeted damage in infected environments. The added benefit of reducing the overall impact of an attack enables it to show fewer signs of infection on multiple systems, since the infection may not be seen for a while unless a user accesses the data.
The third unique method used by the CONTI ransomware includes its abuse of Windows Restart Manager. The manager allows the unlocking of files before an OS restart is performed. The threat uses the manager to unlock and shut down apps so it can encrypt their data. That is especially successful on Windows Servers, where databases are almost always up and running.
The Ransom Note
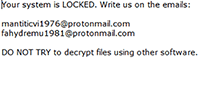
Next, the CONTI Ransomware drops a ransom note on the user’s desktop. The name of the ransom note is ‘CONTI_README.txt.’ Often, authors of ransomware threats would use all caps when giving the ransom note a name as it increases the chances of the user spotting the attackers’ message. The ransom message is very brief. The attackers do not say what the ransom fee is. However, they demand to be contacted via email and provide two email addresses for this purpose – ‘mantiticvi1976@protonmail.com’ and ‘fahydremu1981@protonmail.com.’
It is not advisable to make contact with the cyber crooks responsible for the CONTI Ransomware. Even if you pay the ransom fee, the attackers would demand there is no guarantee that they will honor their end of the deal and provide you with the decryption tool you need to recover your data. This is why instead of trusting the word of cybercriminals, you should install a legitimate anti-malware tool that will remove the CONTI Ransomware from your system safely.
