Anubis Trojan
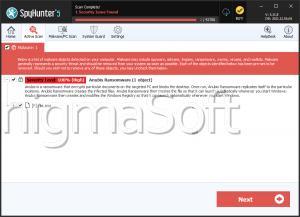
The Anubis Trojan is a banking Trojan that has managed to enter the Google Play Store surreptitiously and is designed to attack Android devices after being placed on the victim's device by a Trojan downloader. Once inside the device, the Anubis Trojan will start its harmful tasks, which encompass sound recording, the encryption of the files from the exterior storage of the device, location tracking, the collection of PayPal credentials, send SMS spam messages, collect the user's online banking credentials and more. The Anubis Trojan also will lock the device's screen turning it into black and will give its admins access to the infected device through a RAT backdoor. The Anubis Trojan has the capacity of taking screenshots of the device's screen if the device's user types an application credential.
The Anubis Trojan also can enter the device disguised as a shopping or financial application to fool the device's user into opening it, which will trigger the download of the threat. The Anubis Trojan was removed by Google the first time it was uncovered; however, other downloaders of the Trojan have entered the Google Play Store recently. The Anubis Trojan's displays an Access request asking the user's permission to access the device, simulating to be a Google Protect Request. When executed, the Anubis Trojan conceals it shortcut icon and places an additional Jar file through run time and stays in the background until it can perform additional tasksThe Anubis Trojan, to make things worse, al has ransomware features, which adds an extra layer of danger to this infamous threat.