ZIPE Ransomware
The ZIPE Ransomware is a newly spotted variant of the infamous STOP Ransomware. The STOP Ransomware is one of the most active ransomware families drawing a lot of attention in 2019. However, the interest in spawning new copies of the STOP Ransomware has not diminished much in 2020 either.
Table of Contents
Propagation and Encryption
The ZIPE Ransomware is likely to be spread via several means:
• Torrent trackers – Users should avoid pirated content as it hides many dangers.
• Malvertising operations –Corrupted advertisements designed to trick users into installing threats on their systems.
• Phishing emails – Fraudulent emails that contain infected attachments or unsafe links.
• Fake software downloads/updates – Bogus prompts that urge users to download/update an application, which triggers the installation of a threat on their systems.
After compromising a targeted PC, the ZIPE Ransomware will scan its contents. The goal of the ZIPE Ransomware is to encrypt a large variety of filetypes, including documents, images, audio files, videos, spreadsheets, presentations, databases, archives, etc. After the encryption process, the affected files will have their names changed as the ZIPE Ransomware adds the ‘.zipe’ extension to them. This means that a file called ‘summer-night.jpeg’ originally will be renamed to ‘summer-night.jpeg.zipe.’
The Ransom Note
_readme.txt:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-sBwlEg46JX
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
helpmanager@mail.chReserve e-mail address to contact us:
restoremanager@firemail.ccYour personal ID
After completing the encryption process, the ZIPE Ransomware will drop a ransom note on the compromised host. The name of the note is ‘_readme.txt.’ In the ransom message, the authors of the ZIPE Ransomware state that they demand $980 as a ransom fee. However, they make it clear that the victims who contact them within three days of the attack successfully, will receive a 50% discount and would have to pay $490. The creators of the ZIPE Ransomware offer to decrypt one file free of charge as long as it does not contain valuable information. The attackers offer up two email addresses as contact details – ‘helpmanager@mail.ch’ and ‘restoremanager@firemail.cc.’
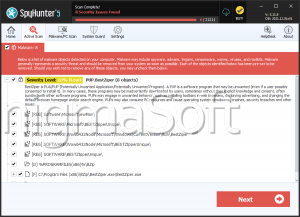
You should avoid contacting cyber crooks as nothing good comes out of it. There is no warranty that you will be allowed to access the decryption key you need even if you pay the fee demanded. Remove the ZIPE Ransomware from your PC with the help of a reliable, reputable anti-malware solution.
How did the ZIPE Ransomware find itself on your computer?
The ZIPE ransomware is being distributed through spam emails with infected attachments, or by exploiting vulnerabilities in the operating systems and any installed programs.
Cybercriminals may send of spam emails, ones with forged header information, tricking users into believing they are from a legitimate shipping company like FedEx or DHL. The email claims the senders tried to deliver a package, but failed for one reason or another. Sometimes the emaisl claim to contain notifications of a shipment that needs to be made. If the users decide to check them and open the attached file, their device gets infected with the ZIPE ransomware. Exploiting of vulnerabilities was also observed with the ransomware, specifically those of the operating system, installed browsers, Microsoft Office and other applications.