BestZiper
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 7,484 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 3,366 |
| First Seen: | April 27, 2017 |
| Last Seen: | March 25, 2026 |
| OS(es) Affected: | Windows |
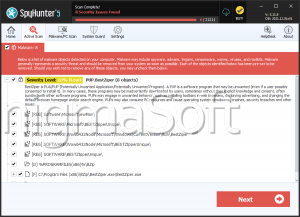
The BestZiper software that you may be invited to install via a free software package is deemed as riskware and Potentially Unwanted Program (PUP). The BestZiper program does not offer ownership information and valid digital signature. The tool is promoted as a viable alternative to apps like 7Zip, WinRAR and WinZip. The BestZiper app may enable users to open, pack and extract data in the 7ZIP, RAR, ZIP and TAR file formats. You can install BestZiper via freeware packages only and its site on bestziper.com features misleading information. There are no contact details at bestziper.com, and the marketing pitch says:
'WinZip is trusted by millions of businesses and consumers to boost productivity, simplify file sharing and keep information private. The world's number one compression and encryption software, WinZip offers apps for all of today's most popular platforms and devices, giving users a better way to exchange files in the cloud, email and social media.'
As you can see, the text above does not cover BestZiper, and it is a blatant copy/paste of text on winzip.com/about.html. The site is dedicated to an archive manager named WinZip, which is developed by the Corel Corporation and has nothing to do with the BestZiper software. Apparently, the Web designers responsible for bestziper.com have no regard for fair completion and copyrights. There is little or no viable information uploaded to bestziper.com regarding the functionality, purpose, and origin of the BestZiper software. PC users that have installed the BestZiper tool have reported that the main program window may include advertisements in the form of banners. Additionally, the BestZiper appears to run in the system background and might show notifications in the tray area, which refer to ad-supported programs and limited-time deals on online stores.
Computer security experts summarized that the BestZiper software is an ad-supported program with dubious origin and distribution mechanism. The ads brought by BestZiper may include links to unreliable online shops and misleading information. The BestZiper app does not compare favorably to alternatives like 7Zip, and PC users may not find it very helpful. You may want to take into consideration that the BestZiper app may record information like your Internet history and downloads log to help affiliated advertisers deliver personalized offers to your desktop. By installing a reliable anti-spyware instrument, you can remove BestZiper safely.
Table of Contents
Analysis Report
General information
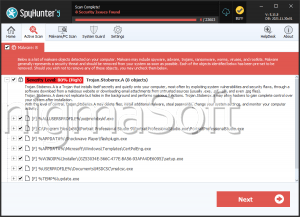
| Family Name: | Trojan.Emotet.AA |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
f11213570933c30421daad32df1ff562
SHA1:
f72fe9625ac38e6cad720f531d49152060dca64f
SHA256:
BA1A6EFBCCC3D06A3525B3D04504D25A53E292B0997F14DDF9D121E834FD05D4
File Size:
9.33 MB, 9326592 bytes
|
|
MD5:
f01d838f9e5c633433ed0badf1a041cf
SHA1:
8d191ba5255a7b695d1dfda3c70ace1879f7f7a6
SHA256:
F694AACDF769EEB343A1B0F013A28FF6889653494D7427F8C00A7EF5562725E7
File Size:
266.75 KB, 266752 bytes
|
|
MD5:
2f2605eba65246d08444f4f5ea395e47
SHA1:
c7c556036b55d370c9713b065c320985f404b807
SHA256:
C8F3E210518A02DC89BCBAA3BD48F0909C8AE5BE180DC52EF2916B4D5A78BC88
File Size:
585.22 KB, 585216 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | SystemSoft Corporation |
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Legal Trademarks | SystemWizard |
| Original Filename |
|
| Private Build | 06/04/1998 |
| Product Name |
|
| Product Version |
|
File Traits
- HighEntropy
- Installer Version
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,315 |
|---|---|
| Potentially Malicious Blocks: | 43 |
| Whitelisted Blocks: | 2,008 |
| Unknown Blocks: | 264 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\wzse684.tmp | Synchronize,Write Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|