XPan Ransomware
PC security researchers have observed various ransomware campaigns active in Brazil currently. The XPan Ransomware is being used to target small and medium businesses located in Brazil (although there is nothing limiting these attacks only to Brazil since these threat attacks can target computers anywhere). Taking advantage of remote desktop connections protected poorly is carrying out the XPan Ransomware attacks. Exploiting poor password protection and security measures, con artists can install the XPan Ransomware on the victims' computers, as well as carry out other threatening operations.
Table of Contents
Although not Identified Yet, the XPan Ransomware Distribution Method is Highly Effective
The current the XPan Ransomware campaign is being targeted towards servers with exposed remote desktop protocol connections on the Internet specifically. Using brute force attacks, taking advantage of weak passwords and security measures, con artists may install the XPan Ransomware manually on the targeted computer. This method of distribution is common, although not as common as the usual tactic of using spam email messages to deliver these attacks. Once the XPan Ransomware has been installed on the victim's computer, the con artists will delete the tracks of their intrusion, making it difficult for PC security researchers to determine how the infiltration occurred or the nature of the ransomware installer. Variants of the XPan Ransomware have been around since October 2016, and it seems that the variant being used in the attacks in Brazil currently is nearly identical to the original incarnation of this ransomware family.
The Misdeeds of the XPan Ransomware
Fortunately, computer users and companies can recover from the XPan Ransomware attack since PC security researchers have released a decryption utility. The XPan Ransomware attacks have been fairly standard when it comes to the actual ransomware portion. The XPan Ransomware will encrypt the victim's files, marking files encrypted during the attack with the file extension '.one.' Victims of the attack are asked to pay 0.3 BitCoin (approximately $400 USD) to recover from the attack. The file encryption is carried out using the AES-256 encryption in combination with other methods. Fortunately, the XPan Ransomware variants have been studied extensively and reverse engineered since their first appearance in 2016.
There are several ransomware Trojans that have been tied to the same group responsible for the XPan Ransomware, a group of Brazilian hackers calling themselves 'TeamXRat' and responsible for such ransomware Trojans as the NMoreira Ransomware and the Xrat Ransomware. The XPan Ransomware also is identical to the AiraCrop ransomware and has several variants. The XPan Ransomware delivers a ransom note named 'Recupere seus arquivos aqui.txt' (Recover your files here.txt), which includes a short message alerting the victim of the attack and asking that the victim contacts the con artists through email. The following is the text of the XPan Ransomware's ransom note:
'Your files have been encrypted.
This is your key: - [RANDOM CHARACTERS]
To recover them please contact us by email: one@proxy.tg by sending your key.
We will reply your email at 24h.'
Dealing with a XPan Ransomware Attack
Fortunately, computer users can recover from the XPan Ransomware attack using the available decryption utility. However, this is an exception – in most ransomware attacks, there is no decryption utility available, and computer users have no recourse to recover their files after the attack. Because of this, it is essential to take preventive measures to ensure that computers are well protected. Securing RDP connections and fixing other vulnerabilities can prevent threats like the XPan Ransomware from being installed in the first place. Having file backups on an external memory device or the cloud can help computer users recover from the XPan Ransomware attacks or other ransomware Trojans while negating any need to pay a ransom (since the victim can recover the files from the backup directly. A reliable security program that is fully up to date can also help intercept attacks, prevent ransomware like the XPan Ransomware from carrying out its encryption routine, and avoid other threat issues.
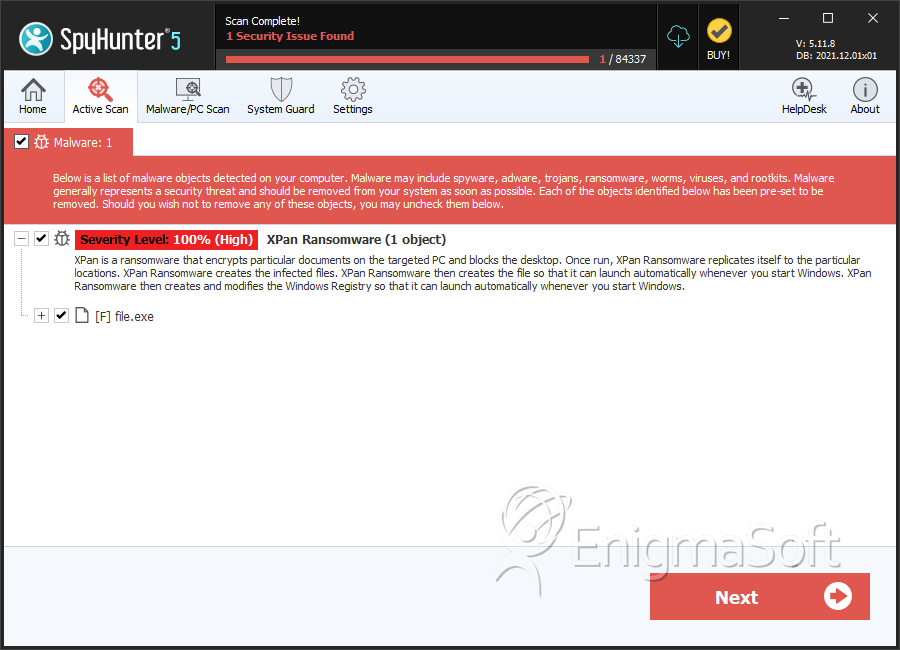
SpyHunter Detects & Remove XPan Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 34260178f9e3b2e769accdee56dac793 | 0 |

