NMoreira Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
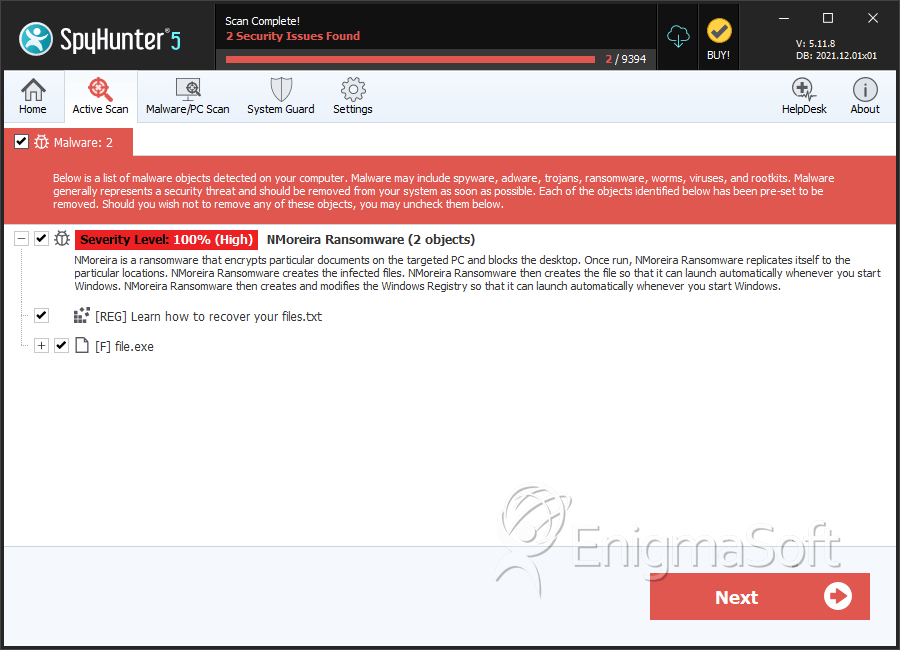
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | November 23, 2016 |
| Last Seen: | May 4, 2019 |
| OS(es) Affected: | Windows |
The NMoreira Ransomware is a ransomware Trojan that is being used to target computer users in Portuguese-speaking countries, particularly Brazil and Portugal. The purpose of the NMoreira Ransomware is to encrypt the victim's files to extort a ransom from the victim. If the NMoreira Ransomware is installed on your computer, PC security analysts advise against paying the ransom, despite that it may be impossible to decrypt files affected by the NMoreira Ransomware without access to the decryption key necessary to restore the infected files currently.
Table of Contents
The NMoreira Ransomware is not Related to the Maktub Ransomware
The NMoreira Ransomware is a ransomware Trojan that is similar to a previously known ransomware threat known as AiraCrop. PC security analysts suspect that the creators of the NMoreira Ransomware are the same as those that created XRat, a known Remote Access Trojan that allows third parties to control the infected computer from afar. The NMoreira Ransomware uses an asymmetric cryptographic method to encrypt the victim's files, making them inaccessible. Essentially, the NMoreira Ransomware encrypts them and then encrypts the decryption key with a different encryption algorithm. The NMoreira Ransomware identifies the files that have been encrypted with the extension '.maktub,' although there seems to be no direct connection between the creators of the NMoreira Ransomware and the creators of the Maktub Ransomware. It is very common for threat creators to misappropriate or recycle portions of their code, which may explain the extension used by the NMoreira Ransomware.
How the NMoreira Ransomware Demands Payment from Its Victims
The NMoreira Ransomware drops a text file on the victim's Desktop. This file is named 'Recupere seus arquivos. Leia-me!.txt,' Portuguese for 'Recover your files. Read me!' The NMoreira Ransomware ransom note is written in Portuguese. This note asks victims to contact the creators of the NMoreira Ransomware by using an included email address, contatomaktub@email.tg, to receive further instructions. Essentially, victims lose access to their files, and the con artists hold the decryption key that is necessary to recover the files. It is currently unknown exactly what ransom is demanded by the NMoreira Ransomware. However, previous variants of this attack demanded the payment of 0.5 BitCoin, which is equivalent to approximately $370 USD at the current exchange rate. The following is the full text of the ransom note that is used by this ransomware threat:
Olá, seus arquivos foram criptografados.
A única forma de tê-los de volta, é atraves de um software juntamente com sua chave privada.
Caso haja interesse em recuperar seus arquivos, entre em contato pelo seguinte email:
contatomaktub@email.tg
No campo do email, me envie sua chave pública que está logo a baixo.
Te responderei o mais rápido possível.
Essentially, the ransom note informs the victim that the files were encrypted and it is necessary to contact the fraudsters' email, finishing with a message that computer users should respond as soon as possible.
Dealing with the NMoreira Ransomware
Malware analysts strongly advise computer users to avoid contacting the people responsible for the NMoreira Ransomware or paying the ransom. Computer users may be cheated after contacting the con artists; either they will be ignored, the con artists may ask for more money, or the provided decryption key will simply not work. Even if the con artists provide you with a working decryption key, your payment finances further threat attacks, and you have no guarantee that your files will not become encrypted soon after payment.
The NMoreira Ransomware and other ransomware Trojans become completely ineffective if the victim can recover the files. Because of this, the best measure that computer users can take to prevent the NMoreira Ransomware and halt these attacks is to have backups of all files and update the backups regularly. Once computer users can recover their files from a backup quickly, the con artists have no way of demanding payments from the victim. Establishing effective backups on the cloud or an external memory device only costs a small fraction of what it would take to recover from a NMoreira Ransomware attack by paying the ransom.
SpyHunter Detects & Remove NMoreira Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | bdbb903591448a9cee8eb3dcc920beec | 0 |

