Wiki Ransomware
Wiki Ransomware Image
Ransomware threats have been one of the most popular security threats in the past few years. Unfortunately, they also are among the most harmful threats out there. One of the most well-known ransomware families is the Dharma Ransomware family. Cyber crooks have created countless variants of this infamous data-locking Trojan. Recently, a new variant of the Dharma Ransomware has emerged. Its name is Wiki Ransomware.
Propagation and Encryption
It is likely that the creators of the Wiki Ransomware are using emails containing macro-laced attachments to spread this nasty threat. It is also possible that they are employing bogus application downloads, torrent trackers, and fake copies of popular software tools to propagate the Wiki Ransomware. When the Wiki Ransomware compromises a computer, it will look for certain files to lock. Usually, ransomware threats are programmed to target a very long list of file types almost always including all of the most popular ones - .mp3, .png, .jpeg, .mov, .mp4, .docx, .ppt, .rar, etc. This makes sure that maximum damage is done to the compromised host, therefore, making it more likely that the victim may consider paying up. As with most Dharma Ransomware variants, as soon as a file undergoes the encryption process, its name will be altered by applying a certain pattern to change it - – '.id-
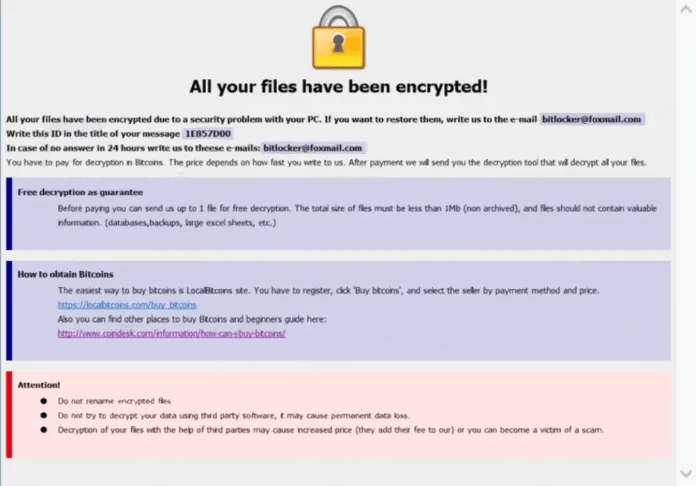
The Ransom Note
The Wiki Ransomware will then drop a ransom note that goes by the name 'FILES ENCRYPTED.txt.' It is a technique popular among cybercriminals to use all caps when naming ransom notes, as it is much more likely for the user to spot their message this way. The note does not state a specific ransom fee, which will be required in exchange for the potential decryption key, which the attackers are holding. However, ransom fees are rarely less than a couple of hundred dollars. There is an email address where the attackers demand to be contacted and where the victim is supposed to get additional instructions – ‘bitlocker@foxmail.com.'
Cooperating with cyber crooks is never a good idea. These people are used to lying through their teeth and will not hesitate to do so with you as long as this will help them get their hands on your hard-earned cash. It is safer to look into obtaining a reputable anti-virus software suite and use it to remove the Wiki Ransomware from your computer for good. You can also attempt to recover some of your files via a third-party data-recovery tool, but it is not likely that you will be satisfied with the results.