Ursu Trojan
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
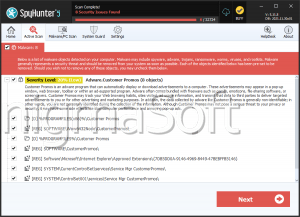
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 18,101 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 105,072 |
| First Seen: | September 15, 2015 |
| Last Seen: | February 25, 2026 |
| OS(es) Affected: | Windows |
Ursu is a threatening Trojan that infiltrates your computer without your knowledge or consent, often by exploiting system vulnerabilities and security flaws. It can be downloaded from corrupted websites or email attachments from untrusted sources. The weaponized files can be from various different types, such as .exe, .pif, .avi and even .jpg files.
Once installed, Ursu remains hidden in the background and will likely perform various harmful functions that allow threat actors to gain complete control over the victim's system. The threatening capabilities of the Ursu Trojan may include deleting files, installing additional malware, collecting passwords, changing system settings and monitoring the computer activity. As Ursu does not have the ability to replicate itself, computer users need to take measures to protect their machines against it to prevent its installation on their computers.
Table of Contents
How Harmful are Threats Like the Ursu Trojan
A Trojan threat is malware that could be injected into or disguised as legitimate software or files, which is usually spread via file sharing, downloads or emails. Once inside your computer, it can cause damage by disabling system functions, hijacking personal information, accessing other devices connected to the network or providing its operators with remote access to the breached device.
Typically, Trojans are used to give hackers access to a user's device, taking control of its resources and opening up opportunities for further attacks, such as ransomware and data theft. In some cases, they are deployed by hackers to create Distributed Denial-of-Service (DDoS) attacks on networks and websites. Alternatively, they may be used to install additional threatening software onto PCs, such as keyloggers, crypto-miners, etc.
How to Avoid the Ursu Trojan Attacks?
Keeping all installed programs up-to-date helps protect against security vulnerabilities targeted by attackers. This applies not only to your operating system but also to any applications you might have, such as browsers or email clients. Routinely backing up essential data could provide an easy way to restore lost data in case something happens due to the effects of a harmful tool infiltrating your machine.
It also is crucial always to be careful when clicking links sent through unsolicited emails – this tactic is often employed by attackers trying to trick users into downloading corrupted files. If you receive suspicious emails containing attachments from unknown senders, try not to interact with them until you have managed to verify the legitimacy of their senders.
Registry Details
Analysis Report
General information
| Family Name: | Trojan.Ursu.A |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
05028cb6c42afa3c0f88162fa4ed96cd
SHA1:
f89be7fece20f436fd5552e904f971b0bcde99e3
SHA256:
4505DFE008D464402C753E1C1FCF1E4EB5D1B486E52BF67FFBE525148383E6E2
File Size:
740.86 KB, 740864 bytes
|
|
MD5:
afc6d2ec749317227235b3c951971f0f
SHA1:
9e4b676c8eb3afff6966537534693d1f36dab1e4
SHA256:
E935C660D03DD8F022FAB4870E984595D33D78690BAB7CEEABB34CB121A30A6E
File Size:
13.31 KB, 13312 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File is .NET application
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 1.0.0.0 |
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- .NET
- dll
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 22 |
|---|---|
| Potentially Malicious Blocks: | 3 |
| Whitelisted Blocks: | 17 |
| Unknown Blocks: | 2 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- MSIL.Gamehack.OS
- MSIL.Kryptik.AR
- MSIL.Rozena.GG
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\ixp000.tmp\rmm41wz.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\ixp000.tmp\rmm41wz.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\ixp000.tmp\sgt41kb.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\ixp000.tmp\sgt41kb.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\ixp000.tmp\tmp4351$.tmp | Generic Write,Read Attributes,Delete |
| c:\users\user\appdata\local\temp\ixp001.tmp\noi55bm.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\ixp001.tmp\noi55bm.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\ixp001.tmp\seb00mz.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\ixp001.tmp\seb00mz.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\ixp001.tmp\tmp4351$.tmp | Generic Write,Read Attributes,Delete |
Show More
| c:\users\user\appdata\local\temp\ixp002.tmp\kyo67cp.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\ixp002.tmp\kyo67cp.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\ixp002.tmp\mti66.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\ixp002.tmp\mti66.exe | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\ixp002.tmp\tmp4351$.tmp | Generic Write,Read Attributes,Delete |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\wow6432node\microsoft\windows\currentversion\runonce::wextract_cleanup0 | rundll32.exe C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\Ygrbwppu\AppData\Local\Temp\IXP000.TMP\" | RegNtPreCreateKey |
| HKLM\software\wow6432node\microsoft\windows\currentversion\runonce::wextract_cleanup1 | rundll32.exe C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\Ygrbwppu\AppData\Local\Temp\IXP001.TMP\" | RegNtPreCreateKey |
| HKLM\software\wow6432node\microsoft\windows\currentversion\runonce::wextract_cleanup2 | rundll32.exe C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\Ygrbwppu\AppData\Local\Temp\IXP002.TMP\" | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| User Data Access |
|
| Encryption Used |
|
| Anti Debug |
|
| Syscall Use |
Show More
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\Users\Ygrbwppu\AppData\Local\Temp\IXP000.TMP\sgt41Kb.exe
|
C:\Users\Ygrbwppu\AppData\Local\Temp\IXP001.TMP\sEB00mZ.exe
|
C:\Users\Ygrbwppu\AppData\Local\Temp\IXP002.TMP\kYo67Cp.exe
|