Octopus Ransomware
A growing number of file-locking Trojans is being spotted daily as more and more cybercriminals dip their toes in the opportunities that ransomware threats offer. If one uses a ransomware building kit or borrows the code of an already established threat of this kind, it can be fairly easy to create a data-encrypting Trojan. This has lowered the entry bar for cyber crooks greatly and made ransomware threats wildly popular. One of the latest spotted ransomware threats is called the Octopus Ransomware. The Octopus Ransomware is a variant of the nefarious Phobos Ransomware.
Propagation and Encryption
The propagation method behind the Octopus Ransomware is yet to be revealed. Some researchers speculate that the attackers may have used the most common technique of spreading file-locking Trojans – spam email campaigns. This involves the sending of an email that contains a fraudulent message aiming at convincing the targets that they should open the seemingly harmless attached file. However, the attachment is certainly not harmless and would carry the unsafe payload of the threat. Cybercriminals can use other alternative propagation methods such as fake pirated variants of popular applications, bogus software updates, and torrent trackers, among many others. The Octopus Ransomware targets countless file types and makes sure to lock them using an encryption algorithm. Once a file undergoes the encryption process of the Octopus Ransomware, you will notice that its extension has been altered. This is because the Octopus Ransomware appends a '.id[
The Ransom Note
Next, the Octopus Ransomware will drop a concise ransom note called 'info.txt,' which states:
’ !!!All of your files are encrypted!!!
To decrypt them send e-mail to this address: octopusdoc@mail.ee.
If we don't answer in 24h., send e-mail to this address: octopusdoc@airmail.cc’
In the note, the attackers inform the users that all their data has been locked and they must pay a ransom fee if they want to retrieve their files. The authors of the Octopus Ransomware provide a primary and secondary email address, which are as follows – ‘octopusdoc@mail.ee' and ‘octopusdoc@airmail.cc.' The latter is given as a backup plan, in case the victim does not receive a reply from the first one within 24 hours.
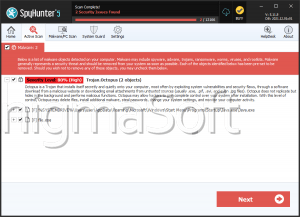
We would advise you to keep away from the authors of the Octopus Ransomware. Even users who pay up are often left empty-handed by cyber crooks like these. Instead, you should obtain a reputable anti-malware solution, which will help you remove the Octopus Ransomware from your computer and keep it safe in the future.