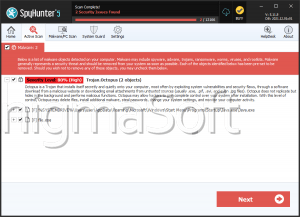
Octopus Trojan
The Octopus Trojan is an encryption ransomware Trojan that was first observed on October 2018. The Octopus Trojan attacks have been distributed using spam email messages, and attacks involving the Octopus Trojan targeted diplomats located in various Asian locations. The Octopus Trojan is distributed via emails claiming to include a new version of Telegram, an instant messaging application. This may be an attempt to exploit the fact that Telegram was blocked in various countries in the region by tricking computer users and government officials in particular into installing a new version of this program to bypass these restrictions. The Octopus Trojan is installed by these corrupted emails on the victim's computer. The Octopus Trojan is a RAT (Remote Access Trojan), a threat that allows the criminals to be in charge of the victim's computer from a remote location.
Table of Contents
This Octopus Limbs can Reach and Damage Your Most Precious Files
The Octopus Trojan allows criminals to download data from the infected computers, upload other threats, or carry out any operation types on the victim's computer. The Octopus Trojan can be used to collect important, confidential data, or use the infected computer to carry out other attacks, which is a threatening aspect of the Octopus Trojan particularly because it is being targeted towards diplomats and government officials specifically. The Octopus Trojan seems to have been created by a group known as DustSquad, that has been responsible for other threats with various similar aspects. PC security researchers strongly advise government officials and other possible targets of threats like the Octopus Trojan to have a strong security program and security measures on their computers to enable them to recover from threats like the Octopus Trojan.
How an Attack of Threats Like the Octopus Work
The Octopus Trojan operations seem to be targeted towards former Soviet states in central Asia and Afghanistan. As a result of an Octopus Trojan infection, the criminals can delete data, modify and copy information from the victim's computer, and gain access to the infected PC. The Octopus Trojan has various similarities to a different threat known as Zoo Park, which also mimicked a Telegram application in its distribution. PC security researchers have noted that in the last two years, various campaigns targeting diplomats in this region of the world have been detected, often in the form of Windows and Android malware designed to take control of victims' computers. This may be attributed to DustSquad, the criminal group that has been working in this region for several years consistently.
Preventing Infections with Threats Like the Octopus Trojan
The Octopus Trojan's infections should be prevented by individuals that deal with sensitive information such as government documents or corporate data especially. Some actions that can be executed to minimize the possibilities of becoming a victim of a threat like the Octopus Trojan include:
- Ensure that all staff knows how to use the Web and computers safely and how to recognize possible threats, such as unsafe files and suspicious emails or websites. Computer users should know never to download or open applications from an unknown source when delivered via unsolicited email messages particularly.
- It is important to ensure that all applications are safeguarded to ensure that any unwanted macro scripts or other content cannot take advantage of security loopholes to carry out attacks on the victim's computer.
- The Octopus Trojan and similar threats should be intercepted and removed by a dedicated threat removal took. It is also important that these security measures are enabled throughout an entire network to prevent these attacks from spreading.
- Since threats like the Octopus Trojan will often be installed by taking advantage of unpatched security holes or other outdated aspects of the victim's software, all security software and firmware should be updated regularly.