Mlock Ransomware
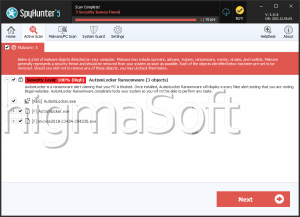
Cybercriminals are using another threatening malware to lock users out from their own devices. The malware threat is named Mlock Ransomware, is a variant from the MeduseLocker Ransomware family, and is capable of rendering a large list of file types completely unusable, via encryption with a combination of cryptographic algorithms.
After a successful infection, the attackers use a double-extortion scheme to get their victims to pay a ransom. Indeed, apart from locking the user's files, the hackers claim to have collected sensitive information from the compromised system that will be released to the public if their demands are not met.
Technical Details
Once deployed on the system, Mlock will scan the files stored there and encrypt those that match its list of targeted file types. Each file locked in this manner will be marked by having '.mlock5' appended to its original name. The threat may avoid tampering with several essential directories not to cause critical system errors that could make the whole system unstable. When it has finished its encryption process, the Mlock Ransomware will drop a ransom note on the system. The message will be created on the device's desktop as an HTML file named 'HOW_TO_RECOVER_DATA.html.'
Mlock Ransomware's Demands
According to the note, Mlock uses both the RSA and AES encryption algorithms to lock the victim's files. To receive the required decryption key and stop the hackers from releasing or reselling the personal or corporate data they claim to have collected, victims are expected to initiate communication and then pay a ransom. The amount that they will have to pay is going to be higher if they do not contact the cybercriminals within the first 72 hours following the Mlock Ransomware infection.
The main communication channel mentioned in the note is a dedicated website hosted on the TOR network. However, to reach the site, users need to download a specific browser and follow several other steps. To avoid the hassle, victims also are left with two email addresses - 'restoreassistance@decorous.cyou' and 'restoreassistance@wholeness.business.' As part of their message, users are allowed to send up to three encrypted files that the attackers promise to unlock and return for free. The chosen files must not contain any valuable information.
The full text of Mlock Ransomware's note is:
'YOUR PERSONAL ID:
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.No software available on internet can help you. We are the only ones able to
solve your problem.We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..We only seek money and our goal is not to damage your reputation or prevent
your business from running.You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.Contact us for price and get decryption software.
qd7pcafncosqfqu3ha6fcx4h6sr7tzwagzpcdcnytiw3b6varaeqv5yd.onion
Note that this server is available via Tor browser only
Follow the instructions to open the link:Type the addres "hxxps://www.torproject.org" in your Internet browser. It opens the Tor site.
Press "Download Tor", then press "Download Tor Browser Bundle", install and run it.
Now you have Tor browser. In the Tor Browser open qd7pcafncosqfqu3ha6fcx4h6sr7tzwagzpcdcnytiw3b6varaeqv5yd.onion
Start a chat and follow the further instructions.
If you can not use the above link, use the email:
restoreassistance@decorous.cyou
restoreassistance@wholeness.businessTo contact us, create a new free email account on the site: protonmail.com
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.'