AutismLocker Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 11 |
| First Seen: | April 11, 2018 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
PC security researchers first observed the AutismLocker Ransomware, an encryption ransomware Trojan, on April 3, 2018. It seems that the AutismLocker Ransomware is still under development, and some of its features are not fully implemented. However, the AutismLocker Ransomware does seem to encrypt victim's files and carry out a ransomware attack. PC security researchers have not associated the AutismLocker Ransomware with an active distribution campaign, however.
Table of Contents
How the AutismLocker Ransomware Attacks a Computer
The AutismLocker Ransomware, like most encryption ransomware Trojans, is designed to take the victims' files hostage by using a highly effective encryption algorithm to make the files inaccessible and then demanding a ransom for the decryption software, needed to restore the affected files. The AutismLocker Ransomware uses the AES 256 encryption, a strong encryption method that results in files that cannot be recovered with currently available means. Threats like the AutismLocker Ransomware tend to target the user-generated files while avoiding the Windows system files or executable files since they rely on victims being able to access the affected computer to read a ransom note and then pay a ransom using their Web browser. Examples of the many file types that threats like the AutismLocker Ransomware will target in their attack include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The AutismLocker Ransomware will delete the Shadow Volume copies of the affected files, as well as the Windows Restore points, which could help computer users find alternate methods to recover the files, apart from encrypting the victim's files. The AutismLocker Ransomware will add a string of random characters to the affected files' names, making it simple to recognize which files have been compromised. The AutismLocker Ransomware will deliver a ransom note to the victim's machine, which seems to be anti-Semitic nonsense created for shock value purely. It is likely that the 'ransom note' is merely a placeholder while the full version of the AutismLocker Ransomware is released. Currently, the ransom note delivered to the victim's computer is contained in a text file named 'listen to me you big juicy nut.txt,' which contains the following text:
'Your computer has been locked...
There are 2 ways to unlock it. In order to get the special code..
You must record yourself gunning down innocent children or send e 15 of your nudes.
Send the recording or the nudes to jewsaintpeople@india.com and we will make sure you kill more than 17 people in the re cording or make sure the nudes belong to you, and then you will get the code.
Once I get the recording/pics I will put them on.
Remember, Hitler did nothing wrong'
Protecting Your Data from Threats Like the AutismLocker Ransomware
The best protection against threats like the AutismLocker Ransomware is to take preventive measures to ensure that your files are safe and the best prevention is to have backup copies of your files. This allows you to recover the affected files by replacing the corrupted versions with a backup copy. A trusty security program that is fully up-to-date can intercept the AutismLocker Ransomware infections, preventing this threat from being installed in the first place.
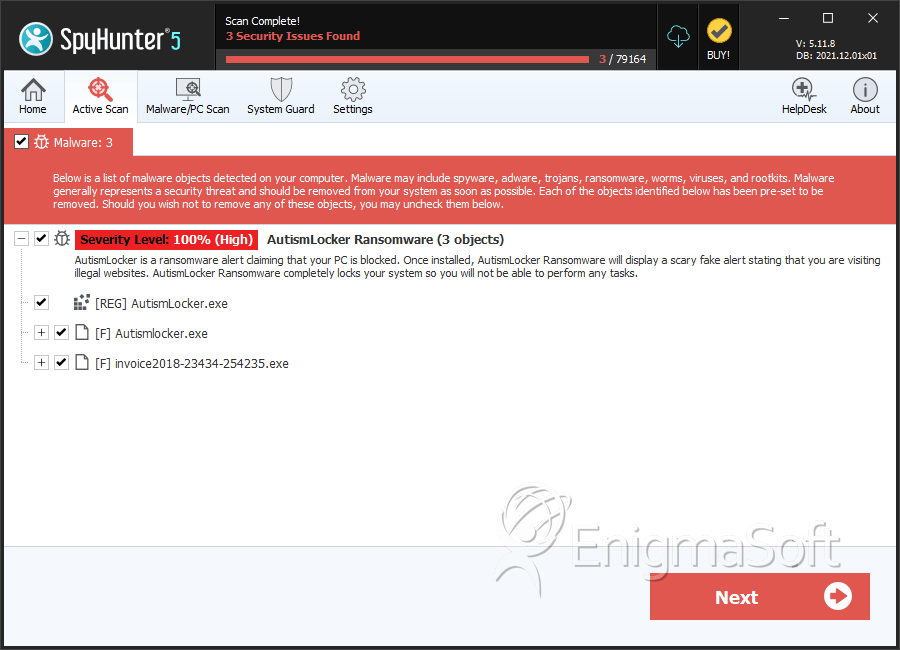
SpyHunter Detects & Remove AutismLocker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Autismlocker.exe | 2fe6cdccb7f08682128d12ab81245d58 | 3 |
| 2. | invoice2018-23434-254235.exe | bae9420047ab0b758adfc8d175006980 | 1 |
