MetaMask 2FA Activation Scam
Fraudulent campaigns that impersonate popular crypto services continue to circulate widely, and one of the latest examples involves misleading messages known as the MetaMask 2FA Activation Scam. These emails push false security claims in an attempt to mislead recipients into surrendering access to their digital assets. The messages are not affiliated with MetaMask, Consensys, or any other legitimate company, organization, or service provider.
Table of Contents
A False Security Notice Disguised as Urgency
The scam begins with emails that claim MetaMask has introduced mandatory Two-Factor Authentication. According to the message, users must enable this feature before a stated deadline or risk losing access to key wallet functions. None of these claims are true. Real MetaMask services do not require such activation, and the contents of these emails are completely fabricated.
When recipients click the prominently placed 'Enable 2FA Now!' button, they are redirected to a counterfeit MetaMask page. This bogus site pretends to guide users through enabling the non-existent feature while praising supposed security improvements. In reality, the attackers use this setup to capture sensitive wallet information and ultimately steal cryptocurrency.
Irreversible Losses and High Stakes
One of the most damaging aspects of this scam is that cryptocurrency transactions offer virtually no recourse. Transfers recorded on the blockchain cannot be reversed, and victims who unknowingly expose their wallets through this scam lose both control of their accounts and the funds inside. This highlights the critical importance of verifying the authenticity of any unexpected email urging account action.
How Spam Fuels a Broad Spectrum of Cyber Threats
Scammers frequently rely on bulk email distribution to spread deceptive content and lure users into dangerous interactions. This technique drives a wide variety of malicious operations, such as:
- Phishing schemes and advance-fee swindles
- Refund, sextortion, and fabricated technical support scenarios
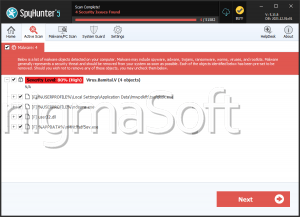
These campaigns also act as delivery channels for malware families, including spyware, ransomware, information stealers, and remote-access tools. Unlike popular belief, spam messages are not always sloppy or full of errors. Many are meticulously crafted to look legitimate and impersonate familiar services with convincing accuracy.
Malicious Attachments and Infection Methods
A second major danger within spam campaigns lies in malicious files delivered through attachments or embedded links. These payloads appear in many formats:
- Executables (EXE, RUN) and compressed archives (ZIP, RAR)
- Documents such as PDF, Microsoft Office, and OneNote files
- Scripts, including JavaScript and similar formats
Some files launch malware immediately once opened, while others rely on user interaction. For instance, Office documents may prompt users to enable macros, and OneNote files may hide links or attachments that trigger payload downloads. Any such interaction could expose a system to significant compromise.
Recognizing the Threat Behind the Message
The MetaMask 2FA Activation Scam takes advantage of trust in established crypto tools by mimicking legitimate security procedures and weaponizing urgency. The campaign's only objective is to hijack victims' digital wallets and drain their holdings. Users should always scrutinize unexpected emails, avoid clicking embedded buttons, and verify account-related notices directly through official channels rather than through links provided in unsolicited messages.
Staying vigilant is the strongest defense against scams designed to exploit both curiosity and fear, especially when dealing with financial platforms where mistakes can result in permanent losses.