Jhash Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 1,768 |
| First Seen: | March 27, 2019 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
The Jhash Ransomware is one of the many variants of HiddenTear that exist today. HiddenTear is an open source encryption ransomware Trojan first observed in August 2015. The Jhash Ransomware, released on November 8, 2017, is just one of many ransomware Trojans that are based on this freely available ransomware engine. The Jhash Ransomware's victims seem to be located in Venezuela, mainly. In the case of the Jhash Ransomware, it seems that it is being delivered to victims through corrupted documents, which include macro scripts that download and install the Jhash Ransomware onto the victim's computer. These will often be delivered to the victim's computer through phishing email messages.
Table of Contents
The Well-Known Attack Executed by the Jhash Ransomware
There is very little about the Jhash Ransomware that is different from most ransomware Trojans. The Jhash Ransomware will encrypt the user-generated files on the victim's computer to take them hostage. The Jhash Ransomware will mark the files it encrypts by adding the file extension '.locky' to the affected files' names. The Jhash Ransomware takes the victim's files hostage to demand a ransom payment to release the decryption key. Samples of the file types that may be targeted by the Jhash Ransomware Trojan in its attack include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
Although the '.locky" file extension was first observed in the infamous Locky Ransomware, this file extension has been used by numerous other ransomware Trojans to mark the affected files, and does not indicate any relationship between Locky and the Jhash Ransomware.
How Cybercrooks may Profit from a Jhash Ransomware Attack
Unfortunately, the Jhash Ransomware uses a combination of the AES and RSA encryptions, which means that the files encrypted by the Jhash Ransomware attack are nearly impossible to recover without the decryption key. The Jhash Ransomware delivers its ransom note in a text file named 'Leeme.txt' (Spanish for 'Readme.txt'), which is dropped on the infected computer. The following is the text of the Jhash Ransomware's ransom note, translated into English:
'This computer has been hacked,
Your personal information has been encrypted, you send us $ 10 through PAYZA to the following payment address: jhash.bancaenlinea@zoho.com, and you will send a screenshot of the transaction to the same email. After that, we will send you a guide to recover your precious files. One wrong step and you will lose all your files, do not make mistakes.'
The victim's Desktop image will be changed to display the following text:
'You should not be scared ... But we have blocked all your files so that they are unusable.
If you want to unlock them ... Open the File Readme.txt that is on your desktop. And carefully follow the instructions.
One wrong step and there will be irreparable damage.'
Dealing with the Jhash Ransomware Infection
Computer users must refrain from following the instructions in the Jhash Ransomware ransom note. Instead, they should restore the files affected by the Jhash Ransomware attack by using file backups. Having file backups on external devices is the only guaranteed way to make sure that your data will not be lost after a threat attack like the Jhash Ransomware.
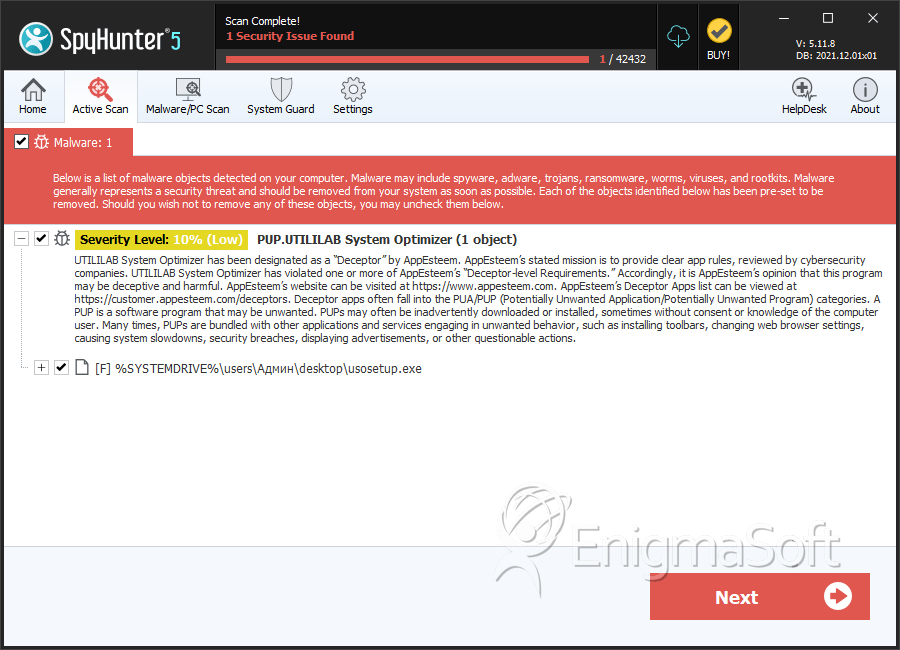
SpyHunter Detects & Remove Jhash Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | usosetup.exe | 890682fe942ba4e2e37e7e4068d6bc6a | 847 |
