CRBR Encryptor Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 9,198 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 71,874 |
| First Seen: | March 4, 2016 |
| Last Seen: | September 11, 2023 |
| OS(es) Affected: | Windows |
The CRBR Encryptor Ransomware seems to be a variant of Cerber 6, a ransomware Trojan that was turned into a RaaS (Ransomware as a Service) platform recently. The CRBR Encryptor Ransomware is only a version of the infamous Cerber ransomware family that was modified slightly, which is the most disseminated and active ransomware family today. There is little to differentiate the CRBR Encryptor Ransomware from the many other ransomware Trojans active currently, and it is identical to the Cerber family variants virtually. The CRBR Encryptor Ransomware will mark the encrypted files with an extension made up of four random characters. The CRBR Encryptor Ransomware displays its ransom note using a program window with the title 'Crbr Encryptor Instructions.' This ransom note notifies the victim of the attack and demands the payment of a ransom.
Table of Contents
How the CRBR Encryptor Ransomware may be Distributed
The CRBR Encryptor Ransomware and other Cerber variants can be distributed in a wide variety of ways. The following methods have been used to distribute the variants of the CRBR Encryptor Ransomware:
- The CRBR Encryptor Ransomware may be distributed using attack websites, which will use exploit kits to distribute threats like the CRBR Encryptor Ransomware to visitors. The CRBR Encryptor Ransomware, in particular, has been linked to attacks using the Magnitude Exploit Kit.
- The CRBR Encryptor Ransomware and other ransomware Trojans may be distributed using corrupted Microsoft Word Documents, which will include compromised macros that download and install the CRBR Encryptor Ransomware onto the victim's computer and may be delivered through the use of spam email messages.
- The CRBR Encryptor Ransomware also may be distributed through email attachments claiming to be PDF files, but are executable files or JavaScript files that use a double extension to hide their true nature from the victim.
The not that Cheap Ransom Demanded by theCRBR Encryptor Ransomware
The CRBR Encryptor Ransomware is among the most threatening and sophisticated ransomware Trojans. This is because the CRBR Encryptor Ransomware combines a strong encryption (RSA 2048) with a large distribution network, which includes its RaaS platform.) During its attack, the CRBR Encryptor Ransomware will delete the Windows Shadow Volume Copies and the Windows Restore points, preventing victims from recovering their files. The CRBR Encryptor Ransomware will target a wide variety of file types, which may include the following:
.r3d, .rwl, .rx2, .p12, .sbs, .sldasm, .wps, .sldprt, .odc, .odb, .old, .nbd, .nx1, .nrw, .orf, .ppt, .mov, .mpeg, .csv, .mdb, .cer, .arj, .ods, .mkv, .avi, .odt, .pdf, .docx, .gzip, .m2v, .cpt, .raw, .cdr, .cdx, .1cd, .3gp, .7z, .rar, .db3, .zip, .xlsx, .xls, .rtf, .doc, .jpeg, .jpg, .psd, .zip, .ert, .bak, .xml, .cf, .mdf, .fil, .spr, .accdb, .abf, .a3d, .asm, .fbx, .fbw, .fbk, .fdb, .fbf, .max, .m3d, .dbf, .ldf, .keystore, .iv2i, .gbk, .gho, .sn1, .sna, .spf, .sr2, .srf, .srw, .tis, .tbl, .x3f, .ods, .pef, .pptm, .txt, .pst, .ptx, .pz3, .mp3, .odp, .qic, .wps.
The CRBR Encryptor Ransomware will change the infected filenames by encrypting the filenames using a base-64 algorithm and adding a file extension made of up of four random characters to the end of each affected file's name. The CRBR Encryptor Ransomware's ransom note is delivered in a file named '_R_E_A_D___T_H_I_S___[RANDOM CHARS]_.hta' and '_R_E_A_D___T_H_I_S___[RANDOM CHARS]_.txt,' both dropped on the infected computer's desktop. The CRBR Encryptor Ransomware ransom note will tell victims to download the TOR browser to pay the CRBR Encryptor Ransomware ransom anonymously (it will be around 0.5 BTC, about $1250 USD at the current exchange rate).
Protecting Your Data from Threats Like the CRBR Encryptor Ransomware
The best protection against the CRBR Encryptor Ransomware and the many other Cerber ransomware variants is to have backups of your files. Having backups of the files on the cloud or an external memory device, makes the people responsible for the CRBR Encryptor Ransomware attack lose any leverage they have over the victim, enabling them to demand a ransom payment. Beside having file backups, PC security researchers also advise computer users to take steps to protect their machines with a reliable security program.
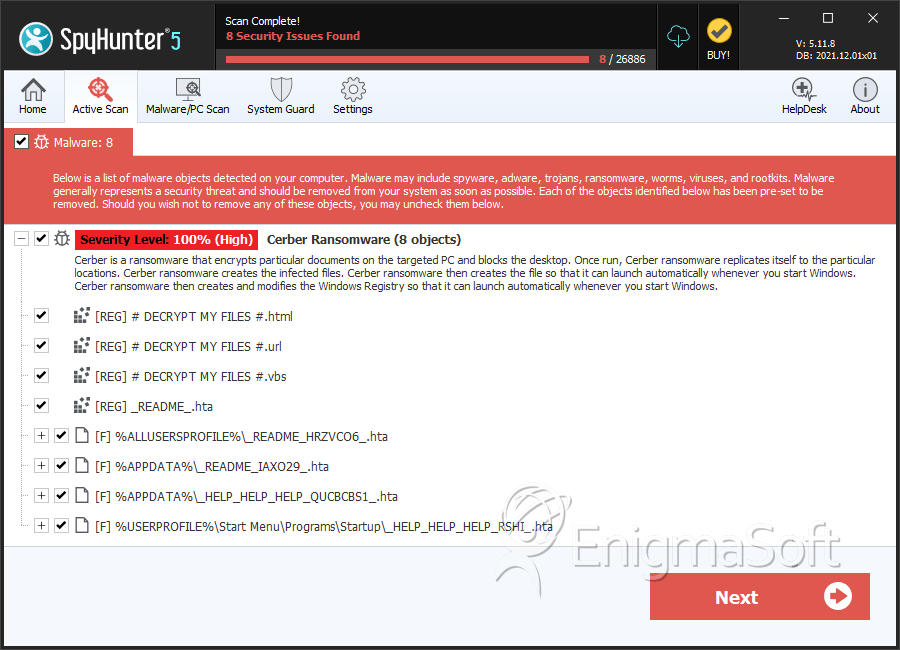
SpyHunter Detects & Remove CRBR Encryptor Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Readme.hta | e125ef487472bfdd17d7e3e7e237d0d9 | 167 |
| 2. | Readme.hta | 8f85ab4bb455ce6d413eff9e9d47a506 | 54 |
| 3. | README.hta | 777e13c9a5cad4e1d2134d5104188ff6 | 43 |
| 4. | README.hta | c4fff6005b70cccd895082e6c79595b3 | 36 |
| 5. | README.hta | e189ce9640edc95a1ba19d0d4d85691b | 24 |
| 6. | README.hta | 107ab5eae352dab9defab24d3ba77b4a | 18 |
| 7. | _HELP_HELP_HELP_QUCBCBS1_.hta | c042f1d91619e9b4f91bf1e1b78fee85 | 14 |
| 8. | _HELP_HELP_HELP_RSHI_.hta | a46e5f2ce8a20bbb8548959debb9ac0c | 10 |
| 9. | _HELP_HELP_HELP_STOV8H1_.hta | 1632ca0953d5499bf251455159a80ea0 | 6 |
| 10. | _HELP_HELP_HELP_ND8FZ.hta | 041ef4b6a12e0b3165172884301b0d1e | 5 |
| 11. | _HELP_HELP_HELP_Z49XU_.hta | 243d0fd4f4bee5f11698c20d43b958ff | 4 |
| 12. | _HELP_HELP_HELP_XFCV_.hta | 01ec9e50d17de043a23997d6562293ad | 3 |
| 13. | _HELP_HELP_HELP_2AK4U21_.hta | 55790c64ce1ff75647d5cadcadf3876e | 3 |
| 14. | _HELP_HELP_HELP_3NNARI.hta | 0ef13a9213c456db231825061eec294c | 2 |
| 15. | _HELP_HELP_HELP_L41VV_.hta | c63b4a524713e4c5f3802463cb46dab8 | 2 |
| 16. | _READ_THI$_FILE_L81EB65A_.hta | 2a6828d2ba37bb97efb4773619b80715 | 2 |
| 17. | _HELP_HELP_HELP_2R9I63OS.hta | a2daec078c54bb6bc5e96038a1506f2c | 1 |
| 18. | _HELP_HELP_HELP_UYUR4YE.hta | bc0c75128b9cbc02c8c053c1155fb6d9 | 1 |
| 19. | _HELP_HELP_HELP_CKJ4GL.hta | 99d3fc208d3623107cfb18a9069e23bd | 1 |
| 20. | _HELP_HELP_HELP_SUXEZY_.hta | 5190e890725bf431ba44001e190c70f5 | 1 |
| 21. | _HELP_HELP_HELP_GLP9_.hta | 5f7533c663ddb4c0ae4dbbaafb50d491 | 1 |
| 22. | _HELP_HELP_HELP_HUUKTW_.hta | 0224da72bc3638b351cf509cdfc443c2 | 1 |
| 23. | _READ_THI$_FILE_DB3DT9_.hta | 7476a75b0680d99f5338b886bc7def62 | 1 |
| 24. | wP6fT.exe | 731279e3c09f8e52a849c0a9c1043bb5 | 1 |
| 25. | cmdkey.exe | 27cf39d205567505d840391e4761a7a0 | 1 |
| 26. | file.exe | 212fa73fd6ed39b4720bcfd8d97426d5 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.